Half a century after the public learned that boys at a Belfast group home were sexually assaulted by senior staff, a key question remains unanswered: was British intelligence implicated in the abuse conspiracy, and did Kincora serve as a ‘honeypot’ to entrap and blackmail powerful figures?
A vast trove of declassified files on Jeffrey Epstein’s sexual, political, and intelligence escapades released by the US Department of Justice has once again thrust disgraced former Prince Andrew Mountbatten-Windsor into the spotlight. With British police reportedly reviewing Andrew’s past sexual activities and links to Epstein, questions are growing about whether Britain’s spy agencies were aware of Andrew’s alleged escapades with minors.
If the darkest rumors turn out to be true, it will not be the first time a British royal had been embroiled in a child rape conspiracy with spy agency involvement. Back in 1980, a scandal erupted when the Kincora Boys’ Home in occupied Ireland was exposed as a secret brothel run by powerful pedophiles. Chief among the alleged perpetrators was Lord Mountbatten — Andrew’s great-uncle.
From the very beginning, hints began to appear that MI5/MI6 knew of the child abuse taking place Kincora, and could have even been running the group home as part of a dastardly intelligence plot. With Britain’s domestic and foreign spies engaged in a savage dirty war in Ireland, and both services running operatives in Republican and Unionist paramilitaries, Kincora would have provided an ideal means of recruiting and compromising potential assets. Official investigations have strongly insinuated British intelligence chiefs had a close bond with many individuals who ran the Boys’ Home.
In May 2025, veteran BBC journalist Chris Moore published a forensic account of the case titled Kincora: Britain’s Shame. Featuring four and a half decades of firsthand research by the author, its groundbreaking contents have been met with general silence by British mainstream media.
In the book, Moore argues persuasively that the Boys’ Home was just one component of a more extensive child abuse network extending across British-occupied Ireland and beyond — in which London’s spying apparatus was not only aware, but likely complicit.
In 2023, Moore met personally with Kincora victim Arthur Smyth in Australia. Smyth’s stay at the Home was brief, but the horrors he endured there left him scarred forever.
“Having interviewed a number of Kincora survivors, I found Arthur’s story familiar. Sent to the Boys’ Home by a Belfast divorce court judge aged 11, he was continually preyed upon by the pedophiles who ran it, and intimidated into silence,” Moore told The Grayzone. “Arthur was also brutally abused repeatedly by a man he knew only as ‘Dickie’, who raped him while bending him over a desk.”
In August 1979, two years after Smyth escaped Kincora, he learned the true identity of ‘Dickie’ was none other than Louis Francis Albert Victor Nicholas Mountbatten, a member of the royal family and Queen Elizabeth II’s cousin. Mountbatten had just been murdered in an apparent IRA bombing attack on his fishing boat off the coast of Ireland. Though the British government appears to remain committed to concealing his crimes from the public, Mountbatten’s pedophilia was common knowledge among both British and US intelligence for decades.
As early as World War II, the FBI had identified Mountbatten as “a homosexual with a perversion for young boys.” A Bureau file detailing this was later identified by historian Andrew Lownie. After requesting other files the Bureau maintained on the royal, Lownie was informed by US authorities they had been destroyed.
Lownie says he was told by an FBI official that the files were only disposed of “after [he] asked for them” — indicating they were “clearly” shredded at the request of the British government.
Kincora conspiracy begins to unravel
Within months of Kincora’s opening in 1958, boys at the facility began coming forward to inform the adults around them that they were being routinely sexually abused. The Boys’ Home was repeatedly visited by police throughout the decades that followed in response to reports of rape and other mistreatment. Despite repeated investigations, time and time again, complaints were ultimately dismissed by the police.
Reports of sexual abuse spiked dramatically in 1971, when a prominent loyalist named William McGrath became the group home’s housefather, and was placed directly in charge of the boys’ day-to-to lives. Moore documented numerous harrowing accounts in which victims described being sadistically raped by McGrath to the point of internal bleeding, with the boys’ silence ensured by threats of violence.
Moore attributes police inaction to the “skillful manipulation” of Kincora’s director, Joe Mains, who successfully convinced officers that accusers were simply lying as revenge for perceived slights by the staff.
As an extremely well-networked figure in British-occupied Ireland, with deep links to prominent Unionist politicians and Protestant paramilitary groups, McGrath enjoyed virtual impunity. He also headed Tara, an armed Masonic loyalist faction covertly run by the British Army, which effectively functioned as an intelligence operation.
In conversations with colleagues, McGrath was known to boast about his work with British intelligence, and the regular trips to London which it entailed. A police source confirmed to Moore that MI6 had an interest in McGrath since the late 1950s, and that “everything McGrath did from this point on was known” to British intelligence. Small wonder campaigners firmly believe Kincora was exploited to compromise and control Unionists, who committed pedophilic offenses at the Home.
The horrifying abuse at Kincora finally surfaced in January 1980 when the Irish Times published an explosive report that triggered a police investigation, which was led by a veteran detective named George Caskey. According to Moore, it took Caskey just three days to decide that Kincora’s leadership were likely guilty.
Within weeks, Caskey’s team had identified dozens of victims of McGrath and others at Kincora, who each gave detailed statements about the abuse they suffered there. Based on their testimony, Mains, McGrath and fellow high-ranking staffer Raymond Semple were suspended from the group home, and arrested a month later. Curiously, Mains and Semple readily admitted their offenses to police, but McGrath aggressively protested his innocence. Resisting interrogation with such skill that investigating officers believed he had rehearsed for their questioning in advance, he made a number of bizarre, cryptic comments.
For one, McGrath declared he was the victim of political intrigue and the accusations against him were bogusly cooked up by the pro-British Ulster Volunteer Force paramilitary faction, among other people “out to destroy me.” He refused to elaborate on who they were, or why he believed he was being maliciously targeted in this manner. McGrath furthermore promised “other stories” and a “rebuttal to these allegations” would “come out in court,” but again declined to expand any further.
In December 1981, Mains, McGrath, Semple and three other individuals found to have abused young boys at two other state-run group homes in occupied Ireland finally stood trial. McGrath was the only defendant to plead not guilty. Present in court at the time, Moore recalls widespread anticipation McGrath’s testimony would “open a Pandora’s Box, laying bare the truth about Kincora and exposing an uncomfortable – some might say unholy – alliance between the British government and unionism, and perhaps even details of a secret MI5 operation.”
However, at the last minute, McGrath’s lawyer made a shock announcement – his client had changed his plea to guilty. McGrath’s volte face elicited a ripple of exasperated sighs across the courtroom, where over 30 Kincora victims had gathered, preparing to testify. Though all six men were convicted of sexual abuse of boys across three Belfast children’s homes, their relatively light sentences drew outrage. In the end, Mains was jailed for six years, while Semple received five years and McGrath, just four.
MI5 proposes creating ‘false files’ to sabotage investigations
For Moore, McGrath’s change of heart raises obvious suspicions that someone persuaded him to keep his mouth shut about “what had been said to him and by whom.” The police investigation established the six men knew each other and shared information about abused children in state-run boys’ homes, but did not explore the possibility they were part of a wider pedophile ring. The most significant official probe into Kincora since, the Northern Ireland Historical Institutional Abuse Inquiry (HIA), initially raised hopes such information might emerge when it was launched in 2013.
That probe, which centered around allegations by British intelligence whistleblowers Colin Wallace and Fred Holroyd that the UK security state was complicit in systematic child rape at Kincora, appeared to leave MI5 extremely uneasy about the potential for British spies’ darkest secrets coming to light in occupied Ireland.
The HIA, however, appears to have been set up to fail. With no ability to compel MI5 or MI6 to produce records, the commission was forced to accept only whatever heavily redacted files the agencies voluntarily provided.
The decision to limit the scope of the HIA’s oversight came despite appeals by prominent figures including victims of sex abuse at Kincora, parliament’s home affairs committee, and former military officials, who claimed British intelligence was complicit in abuses at Kincora, and demanded the Inquiry be granted the ability to subpoena sensitive documents and witnesses.
As anonymous security and intelligence operatives spoke via videolink in the HIA hearings, Inquiry chair Judge Anthony Hart appeared to take their testimony at face value.
The Inquiry’s handling is all the more shocking given the contents of a June 1982 document provided by MI5 to the HIA showing how the agency’s higherups planned to counteract the inquiry itself.
Anxious to distance themselves from the horrors of Kincora, the British spy agency discussed creating “false files” to counteract “lines of enquiry which it was anticipated” that Caskey might pursue. In other words, MI5 was actively seeking to deceive police investigators through forgery.
But the HIA later declared it was “satisfied” that “the suggestion was not pursued,” concluding that the “false files” were not produced for the purposes of misdirecting the inquiry.
Kincora coverup continues
In 2020, it was revealed that extensive police records on investigations into Kincora from 1980 to 1983 had conveniently been destroyed roughly around the time the Inquiry was established.
The files which survived show the HIA received a number of tips suggesting MI5/6 were indeed entangled in pedophilic abuse at Kincora, only to consistently understate their significance.
For example, MI5 told HIA it had no records of William McGrath working for the agency. Conversely, documents produced by the intelligence service indicate how in April 1972, McGrath, who was “commanding officer of the Tara Brigade,” had not only been plausibly “accused of assaulting small boys,” but “could not account for any cash that had been handed to him over a period of a year.”
The HIA accepted MI5’s risible explanation that this information was not passed on to local police because it was unclear McGrath’s attacks on the boys were pedophilic in nature, rather than simply physical. “We ought not to assume that ‘assault’ would have been interpreted at the time by… [MI5] as being of a sexual type,” an internal document presented to the Inquiry declared.
Responding to a separate MI5 document from November 1973 noting McGrath was implicated in “assaulting small boys,” the HIA noted British intelligence was legally obligated to report such an “arrestable offence” to the police, and that by not doing so, it could be argued “the MI5 officers who had this information were in breach of that duty.” But the Inquiry concluded that “to take that view would be unjustified for several reasons,” primarily that “an unidentified member of Tara” was the source of this “unsubstantiated allegation.”
Similar mental gymnastics were employed to downplay the contents of an October 1989 MI6 file detailing “various allegations surrounding the Kincora Boys’ Home,” which revealed the spy agency “certainly ran at least one agent who was aware of sexual malpractice at the home and who may have mentioned this” to his handler. Judge Hart stultifyingly concluded, “it is quite possible the [MI6] officer misinterpreted what was discussed at the meeting.”
The HIA also insisted MI5 was unaware McGrath worked at Kincora until 1977. But that claim was effectively contradicted by the Inquiry itself, which unveiled MI5 documents from January 1976 clearly stating, “McGrath was reported in March 1975 to be warden of Kincora Boys’ Hostel.” A police memo from November 1973 dispatched to MI5’s director similarly noted McGrath was a “social worker” at Kincora.
Whitewash inquiry implicates MI6 chief in Kincora
As part of its probe, the HIA ordered “searches of documents and records” held by MI5, MI6, GCHQ, and the Metropolitan Police on allegations of child sex abuse by public figures and servants. In response, MI5 released files listing 10 powerful individuals, including diplomats, government ministers, and lawmakers, who Britain’s domestic spying agency had evidence to suggest may have been involved in pedophilic abuse.
Chief among them was veteran spy and dark arts specialist Maurice Oldfield, who oversaw MI6 operations in occupied Ireland throughout the 1970s, first as its deputy then chief. Shortly before his April 1981 death, Oldfield was outed as gay, which precluded him from serving with the agency under contemporary recruitment rules. Resultantly, “MI5 conducted a lengthy investigation to determine whether” Oldfield’s sexual proclivities “posed a risk to national security by making him vulnerable to blackmail or other pressure.”
Over the course of “many interviews,” he “provided information about homosexual encounters with male domestic staff, referred to as ‘houseboys’, whilst serving in the Middle East in the 1940s and hotel stewards in Asia in the 1950s.” Media reporting prior to Oldfield’s death suggested he was “a compulsive” user of “rent boys and young down-and-outs,” which was well-known to his security detail. However, the HIA repeatedly exonerated Oldfield of any wrongdoing, despite receiving bombshell evidence implicating him in the horrendous pedophilic acts perpetrated at Kincora.
Unbelievably, its report concluded “there is insufficient information in the records to deduce whether the term ‘houseboys’” was “used simply to describe domestic staff or to denote youth, leaving ambiguity over the ages of the other parties.” This is despite an anonymous MI6 officer telling the Inquiry the agency possessed four separate “ring binders” documenting Oldfield’s “relationship” with Kincora, his “friendship” with its chief Joe Mains, and potential personal connection to “alleged crimes at the boys’ home.”
Heavily redacted files published by the HIA also indicate MI5 was “aware of allegations” that occupied Ireland’s police knew Oldfield was intimately embroiled in the scandal. An internal agency telegram noted well-grounded suspicions the MI6 chief “was involved in the Kincora boys home affair in the course of occasional visits to Northern Ireland (associated with his job) between 1974 and 1979.” Still, the Inquiry dismissed this as proof of MI5/6 involvement in the child abuse conspiracy, on the grounds these excerpts referred purely to “allegations.”
The Kincora coverup continues today. In April 2021, the BBC announced “a new season of landmark documentaries… set to shine a new light on remarkable stories from Northern Ireland’s recent history.” Among the scheduled films was Lost Boys, which told the hideous tale of how numerous children inexplicably vanished in Belfast during the Troubles. It concluded the cases were all linked to pedophilic abuses at Kincora. Interviewees included several former police officers, who believed their inquiries into the disappearances had been systematically sabotaged by British intelligence.
On the eve of transmission, Lost Boys was pulled from broadcast. BBC managers were reportedly “shocked by its content, particularly evidence of MI5’s involvement in covering up the Kincora saga.” Moore, who consulted on the film, told The Grayzone there are strong insinuations British intelligence took a keen interest in the documentary’s producers, AlleyCats. “The home of one staffer involved in editing Lost Boys was burgled,” he says. “Another Alleycats member suspected a break-in, but could not be entirely certain.”
Having investigated Kincora since it first came to public attention, Moore concludes “MI5 and its cohorts in the police believe they can do what they want with little or no regard for the truth, the law or democracy,” noting British intelligence “somehow persuaded the government to bury Kincora files until 2065 and 2085.” The veteran muckraker also recently learned his private communications with journalists investigating other cases of criminal activity by MI5/6-sponsored loyalist paramilitaries – including murder – have been heavily surveilled.
“The British state has illegally spied on people trying to expose the truth in Northern Ireland for many years, in what they call a ‘defensive operation’. Senior local police chiefs have admitted surveillance tactics were deployed against 320 journalists and 500 lawyers over a decade, including me,” Moore concluded. “My telephone was monitored due to probing government-funded loyalist killers. Like many police officers who’ve looked into these matters, I’m all too aware of how authorities frustrate criminal investigations.”
February 10, 2026
Posted by aletho |
Book Review, Corruption, Deception, Full Spectrum Dominance, Timeless or most popular | GCHQ, Human rights, Ireland, MI5, MI6, UK |
Leave a comment
From the truth about who really killed Diana to the depraved world of government officials sexually abusing children and the subsequent cover-up, it is now clear that nearly all major stories are either blocked from publication or rewritten by Soviet-style propaganda agents working for the British deep state.
Virtually nothing you read in British newspapers about security, defense, and wars is honest journalism. Instead, it is propaganda crafted by a new secret UK military department tasked with rewriting journalists’ copy or, in some cases, simply ensuring their articles never see the light of day.
That is the shocking conclusion of a new investigation by The Grayzone, which obtained secret documents exchanged between the UK and Australian governments over Canberra’s plans to adopt Britain’s “off-the-shelf” operation and incorporate it into its own government practice for handling journalists.
The impressive reporting by Kit Klarenberg and William Evans reveals, in short, that the UK military has created its own censorship department. It either blocks journalists from exposing major stories of public interest or, more commonly, redrafts the thrust of journalists’ pieces to present a different version to the gullible public.
A trove of secret communications reveals how the secretive Defence and Security Media Advisory (DSMA) Committee censors the output of British journalists while categorizing independent media as “extremist” for publishing “embarrassing” stories. What sounds like an account of secret police operations in Eastern Europe during the Soviet era, the documents show that this army intelligence department regularly blocks journalists from continuing to investigate a subject through a formal system called “D Notices” – which, remarkably, journalists almost always respect.
“The DSMA imposes what are known as D-Notices, gag-orders systematically suppressing information available to the public,” The Grayzone report states.
The files provide the clearest view to date of this underground committee’s inner workings, exposing which news items the state has sought to shape or keep from public view over the years. These include “the 2010 death of a GCHQ codebreaker, MI6 and British special forces activity in the Middle East and Africa, the sexual abuse of children by government officials, and the death of Princess Diana,” the report reveals.
British media, it seems, is in a crisis it never anticipated. Its journalists are, in reality, no longer working as journalists but as propaganda agents of the state. Under this system, which nearly all journalists sign up to, when a reporter wants to pursue a story, they must consult this department, which then effectively controls both the journalist and the story from that point forward. The absurd practice of ‘copy approval’ – where journalists send their final draft before submitting for publication – is routinely enforced.
This practice, a milestone in the death of British journalism, comes as no surprise to me. For decades, I have sent questions to the UK’s Foreign Office and Ministry of Defence, only to become a victim of the comical, if not pathetic, game that follows. A spokesperson asks for your deadline and then, mysteriously, 30 minutes before that time, you receive a “response” meant to serve as a quote from a senior official. It not only looks computer-generated but is often irrelevant to the subject. This is Britain – a country once seen by the whole world as a beacon of freedom and democracy, now operating like a cheap West African dictatorship, pumping out lies and manufacturing consent on an industrial scale.
That such a secret censorship department exists and flourishes should shock no one. In 2023, my own investigation discovered that UK and US weapons were being resold on the dark web. It wasn’t exactly a great scoop, but the hard work lay in substantiating the story with expert opinions and forensic analysis of photos and website postings. I was amazed as weeks passed while I badgered the Daily Mail’s absurdly young Defense Editor to run the story. He played every trick in the book to avoid it until finally he and others agreed to publish – but watered it down so much, removing all the top quotes from hardcore military and political experts that supported the story’s thrust. Clearly, he and others were under the control of these DSMA censor agents, who could not allow a piece alleging that shoulder-mounted rocket systems used by both the US and UK armies were being openly sold on the black market.
A second, much more detailed investigation – which supported the belief that barely a third of all UK military kit was actually reaching frontline Ukrainian soldiers – I didn’t bother sending to the Daily Mail but published on Patreon. One of its chief findings was that a senior Conservative MP admitted to me in a WhatsApp exchange that the UK had, in fact, installed tracking devices in some of the more expensive equipment, like Armoured Personnel Carriers (APCs), but at a certain point these devices were simply switched off and disappeared from the screens. It also revealed the bombastic stupidity of the then–UK Defence Minister, Ben Wallace, who conveniently chose to ignore a UN report identifying the influx of cheap Western-made assault rifles into the Libyan arms bazaar as a main reason for the spike in terrorism in the Sahel region – while insulting the Nigerian president who had made the claims, saying he “probably watches RT television.” When I suggested to Mr. Wallace that a simple way to verify these claims would be to send agents to Libya to conduct their own surveillance, his reply was, “Why don’t you do that?” before blocking me.
Wallace’s extraordinary rudeness shocked me at the time. But it was clear he was used to a much more servile, sycophantic manner from UK journalists who didn’t ask difficult questions – and that I was obviously breaking from tradition. Clearly, the DSMA department controls all those Westminster-based hacks, their stories, and even their story ideas, so it’s understandable that his rage boiled over.
The Grayzone’s findings make for depressing reading for anyone old enough to remember when British journalism was the finest in the world. But they also raise other questions, chiefly: Who is actually behind British titles? Or more specifically, who is funding them? Most UK newspapers don’t make any money, so it’s understandable that a new relationship with the deep state might help them remain relevant – especially now that the news is being baked for them, ready to be served. This has changed the role of the British journalist: no longer the baker, but relegated to the delivery boy on the moped.
Yet where the big titles get their revenue to stay in business remains a mystery. Is part of the same deal on censorship and copy control that the state funds them through surreptitious, murky channels – perhaps via companies with close links to the heart of power? Follow the money.
February 2, 2026
Posted by aletho |
Deception, Full Spectrum Dominance, Mainstream Media, Warmongering | GCHQ, MI6, UK |
Leave a comment
Jeremy Fleming, the head of GCHQ (Government Communications Headquarters), one of three leading spy agencies in the UK, has publicly discussed the agency’s wish to promote ‘pre-bunking’ – feeding the public with information designed to undermine narratives before they even appear on social media. In other words, spy agencies originally tasked with monitoring events are now engaged in spreading propaganda about things that haven’t actually happened, and probably have been doing so for a long time.
Fleming described pre-bunking as a process of issuing ‘public warnings’. This is, you will appreciate, a misuse of the term since the ‘public’ are not aware that they are hearing ‘warnings’. They are being fed information or denied access to information without being told who is ultimately controlling the narrative. This is happening all over the world, as revealed by Elon Musk’s revelations about the role of the FBI in closely censoring Twitter content.
The pandemic has multiplied information actors with shady sources of funding and likely ties to government and Big Pharma, who are tasked with spreading pre-bunking narratives. Among these are a host of ‘fact-checkers’. Full Fact UK presents itself as an independent fact-checker located not a million miles away from Westminster and GCHQ with a host of funding sources including Facebook, the National Endowment for Democracy, the International Fact Checking Network, and many others.
Part of Full Fact’s funding is specifically tied to vaccines. In an article entitled No evidence rise in deaths due to unknown causes in Canada is linked to Covid-19 vaccine, Full Fact reveals its pre-bunking role. It is concerned about the following sentence publicised on YouTube and shared on FB: ‘In Alberta, Canada, unknown causes of death are causing even more deaths than heart disease, strokes and diabetes combined.’
Full Fact doesn’t dispute that this is true, it merely wants you to feel assured that there is no evidence these deaths were caused by Covid-19 vaccines – something that the creators of the YouTube source video do not assert. In other words, Full Fact wants to pre-empt any suggestion that the undisputed huge rise in unexplained deaths in Alberta, Canada (and presumably the many other highly vaccinated nations suffering in the same way) is anything to worry about. That is a manipulation of which GCHQ would no doubt be very proud. These are deaths in need of explanation, not inconsequential data sets that can be swept under the carpet.
So should we be concerned about statistically significant rising excess all-cause deaths in highly vaccinated countries around the world and incidentally low birth rates in the same countries (see here and here)? Effects which are not being seen in nations with low vaccination rates, for example in Uganda as reported in this video. Yes, we should be concerned, because the trend could be catastrophic for Western civilisation (if such a thing exists).
Let us examine a hypothetical country with a stable population of 5million. Each year 35,000 people die and 35,000 babies are born. If annual deaths rise by 15 per cent, as they are in New Zealand, and births fall by 13 per cent, as they are in Sweden, what would happen? In one year, 5,250 extra people would die and 4,550 fewer babies would be born, a net loss of 9,800 persons in the population.
That is a net loss of 0.2 per cent of the population size. So not too much to worry about – or is it? Medsafe reports indicate serious health outcomes could be as much as 1,000 times the number of deaths proximate to mRNA vaccination. We could speculate maybe 100 times the number of excess deaths over a longer period. Scale that up to the whole world’s population and you would arrive at 8.4million deaths along with an incalculable impact on global health, possibly 20 per cent of the world’s mRNA-vaccinated population, many in the West, affected with a significant health deficit – more than one billion people.
Why are they falling ill and dying? As a result of a new technology – mRNA biotechnology – which governments, Big Pharma and the medical establishment are bidding to mandate widely for hundreds of conditions stretching into the future. A February 2022 article in Nature lists 90 mRNA lead developers in the global vaccine landscape with 137 mRNA vaccines in the pipeline and you can bet your bottom dollar that number has grown substantially since.
In 2023 we are about to be engulfed by a tsunami of biotechnology involving an army of biotechnologists, their investors and supporters who are hoping against hope, like Full Fact UK, that we don’t notice how many people are dying suddenly for no recorded reason. They are busy along with thousands of other funded ‘experts’ pushing out the message that there is nothing to see here. They are hoping that regulatory agencies are going to approve their products at lightning speed with a minimum of scrutiny and fuss, as happened during the pandemic. In fact, the FDA has already flagged a speeded-up process for mRNA lookalikes.
The alternatives for wannabe mRNA billionaires are unthinkable. If biotechnology is fingered as the cause of the current wholly unprecedented rise in deaths and injury, their finances, reputation, and future will fall apart. Therefore they, like GCHQ, are busy pre-bunking to save their pet biotech projects from cancellation due to the risk of death and injury. They don’t care if you die as long as no one works out what you died of. Canada, New Zealand, Australia, the EU, USA, and the whole Western world are playing along by pretending, with the help of their spy agencies, that no one knows why so many people are falling down dead. They are busy hiding data, delaying investigation, and looking the other way.
If we don’t debunk and stop them very soon, they along with the police, the courts, and our employers will be breaking down our doors in 2023 and coming for us with deadly needles for every ill we don’t even have. Given the disastrous and deadly failure of Covid vaccines and lockdowns, this could only be described as a futuristic frenzy of psychopathic dysmorphia—a distortion of real appearances. It would make 2022 look like a cakewalk.
So our task in 2023 is to get this one message across: not just Covid mRNA vaccines, but biotechnology and gene editing in general is inherently dangerous. It bids to redesign, and therefore undermines, the stable basis of physiology, DNA, built up over millions of years of evolution.
This is a task that can be achieved only if our efforts are global, if MPs, business leaders, senior civil servants, medical decision makers, and people of influence and common sense all over the world are approached, challenged, and re-educated. For this reason, in 2022 we founded a dedicated website, GLOBE: Campaign for Global Legislation Outlawing Biotechnology Experimentation.
You can visit now for more information and register for regular updates by email.
Biotechnology is a serial killer. A killer that has been identified by irrefutable evidence and now needs to be convicted and sentenced in the courts of ancient common law, public opinion, and fair leadership. We cannot leave this task to unnamed others or the vagaries of chance. It is up to us to get this done.
January 4, 2023
Posted by aletho |
Deception, Fake News, Timeless or most popular, War Crimes | COVID-19 Vaccine, GCHQ, UK |
Leave a comment

The Maughan Library Gate at Kings College London, UK. David JC | Alamy
LONDON — In a previous investigation, MintPress News explored how one university department, the Department of War Studies at King’s College London, functions as a school for spooks. Its teaching posts are filled with current or former NATO officials, army officers and intelligence operatives to churn out the next generation of spies and intelligence officers. However, we can now reveal an even more troubling product the department produces: journalists. An inordinate number of the world’s most influential reporters, producers and presenters, representing many of the most well-known and respected outlets — including The New York Times, CNN and the BBC — learned their craft in the classrooms of this London department, raising serious questions about the links between the fourth estate and the national security state.
National security school
Increasingly, it appears, intelligence agencies the world over are beginning to appreciate agents with a strong academic background. A 2009 study published by the CIA described how beneficial it is to “use universities as a means of intelligence training,” writing that, “exposure to an academic environment, such as the Department of War Studies at King’s College London, can add several elements that may be harder to provide within the government system.”
The paper, written by two King’s College staffers, boasted that the department’s faculty has “extensive and well-rounded intelligence experience.” This was no exaggeration. Current Department of War Studies educators include the former Secretary General of NATO, former U.K. Minister of Defense, and military officers from the U.K, U.S. and other NATO countries. “I deeply appreciate the work that you do to train and to educate our future national security leaders, many of whom are in this audience,” said then-U.S. Secretary of Defense (and former CIA Director) Leon Panetta in a speech at the department in 2013.
King’s College London also admits to having a number of ongoing contracts with the British state, including with the Ministry of Defence (MoD), but refuses to divulge the details of those agreements.
American connections
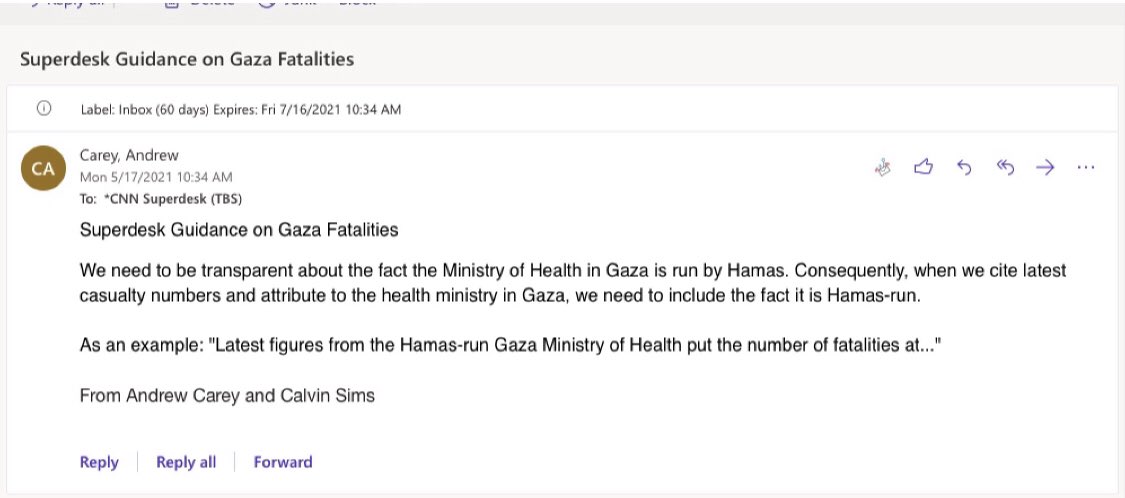
Although a British university, King’s College markets itself heavily to American students. There are currently 1,265 Americans enrolled, making up about 4% of the student body. Many graduates of the Department of War Studies go on to attain powerful positions in major American media outlets. Andrew Carey, CNN’s Bureau Chief in Jerusalem, for example, completed a master’s there in 2012. Carey’s coverage of the latest Israeli attack on Gaza has presented the apartheid state as “responding” to Hamas rocket attacks, rather than being the instigator of violence. A leaked internal memo Carey sent to his staff last month at the height of the bombardment instructed them to always include the fact that the Gazan Ministry of Health is overseen by Hamas, lest readers begin to believe the well-documented Palestinian casualty figures brought on by days of bombing. “We need to be transparent about the fact that the Ministry of Health in Gaza is run by Hamas. Consequently, when we cite latest casualty numbers and attribute to the health ministry in Gaza, we need to include the fact that it is Hamas run,” read his instructions.
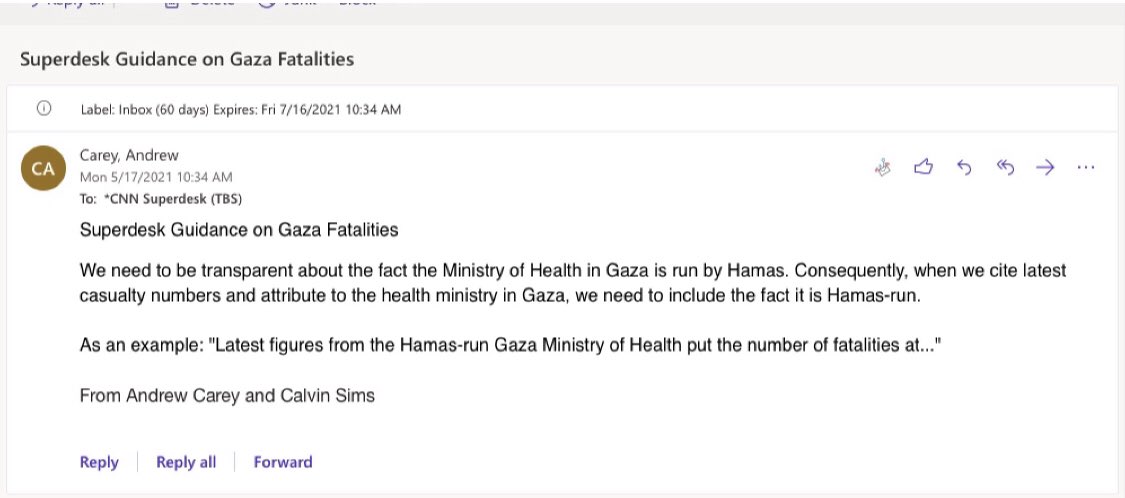
King’s College alumnus turned CNN Jerusalem bureau chief Andrew Carey instructed reporters on how to cover Israel’s latest assault on Gaza
Once publicized, his comments elicited considerable pushback. “This is a page straight out of Israel’s playbook. It serves to justify the attack on civilians and medical facilities,” commented Al-Jazeera Senior Presenter and Producer Dena Takruri.
The New York Times, the United States’ most influential newspaper, has also employed Department of War Studies alumni. Christiaan Triebert (M.A., 2016), for example, is a journalist on their visual investigations team. He even won a Pulitzer Prize for “Revelations about Russia and Vladimir Putin’s aggressive actions in countries including Syria and Europe.” Hiring students from the school for spooks to bash Russia appears to be a common Times tactic, as it also employed Lincoln Pigman between 2016 and 2018 at its Moscow bureau.
Josh Smith, senior correspondent for influential news agency Reuters and formerly its correspondent in Afghanistan, also graduated from the department in question, as did The Wall Street Journal’s Daniel Ford.
Arguably the most influential media figure from the university, however, is Ruaridh Arrow. Arrow was a producer at many of the U.K.’s largest news channels, including Channel 4, Sky News and the BBC, where he was world duty editor and senior producer on Newsnight, the network’s flagship political show. In 2019, Arrow left the BBC to become an executive producer at NBC News.
The British invasion
Unsurprisingly for a university based in London, the primary journalistic destination for Department of War Studies graduates is the United Kingdom. Indeed, the BBC, the country’s powerful state broadcaster, is full of War Studies alumni. Arif Ansari, head of news at the BBC Asian Network, completed a masters analyzing the Syrian Civil War in 2017 and was soon selected for a leadership development scheme, placing him in charge of a team of 25 journalists who curate news primarily geared toward the substantial Middle Eastern and South Asian communities in Great Britain.
Many BBC employees begin studying at King’s years after their careers have already taken off, and balance their professional lives with pursuing new qualifications. Ahmed Zaki, Senior Broadcast Journalist at BBC Global News, began his master’s six years after he started at the BBC. Meanwhile, Ian MacWilliam — who spent ten years at BBC World Service, the country’s official news broadcast worldwide, specializing in sensitive regions like Russia, Afghanistan and Central Asia — decided to study at King’s more than 30 years after completing his first degree.
Another influential War Studies alumnus at the World Service is Aliaume Leroy, producer for its Africa Eye program. Well-known BBC News presenter Sophie Long also graduated from the department, working for Reuters and ITN before joining the state broadcaster.
“It’s an open secret that King’s College London Department of War Studies operates as the finishing school for Anglo-American securocrats. So it’s maybe not a surprise that graduates of its various military and intelligence courses also enter into a world of corporate journalism that exists to launder the messaging of these same ‘security’ agencies,” Matt Kennard — an investigative journalist for Declassified U.K. who has previously exposed the university’s connections to the British state — told MintPress. “It is, however, a real and present danger to democracy. The university imprimatur gives the department’s research the patina of independence while it works, in reality, as the unofficial research arm of the U.K. Ministry of Defence,” he added.
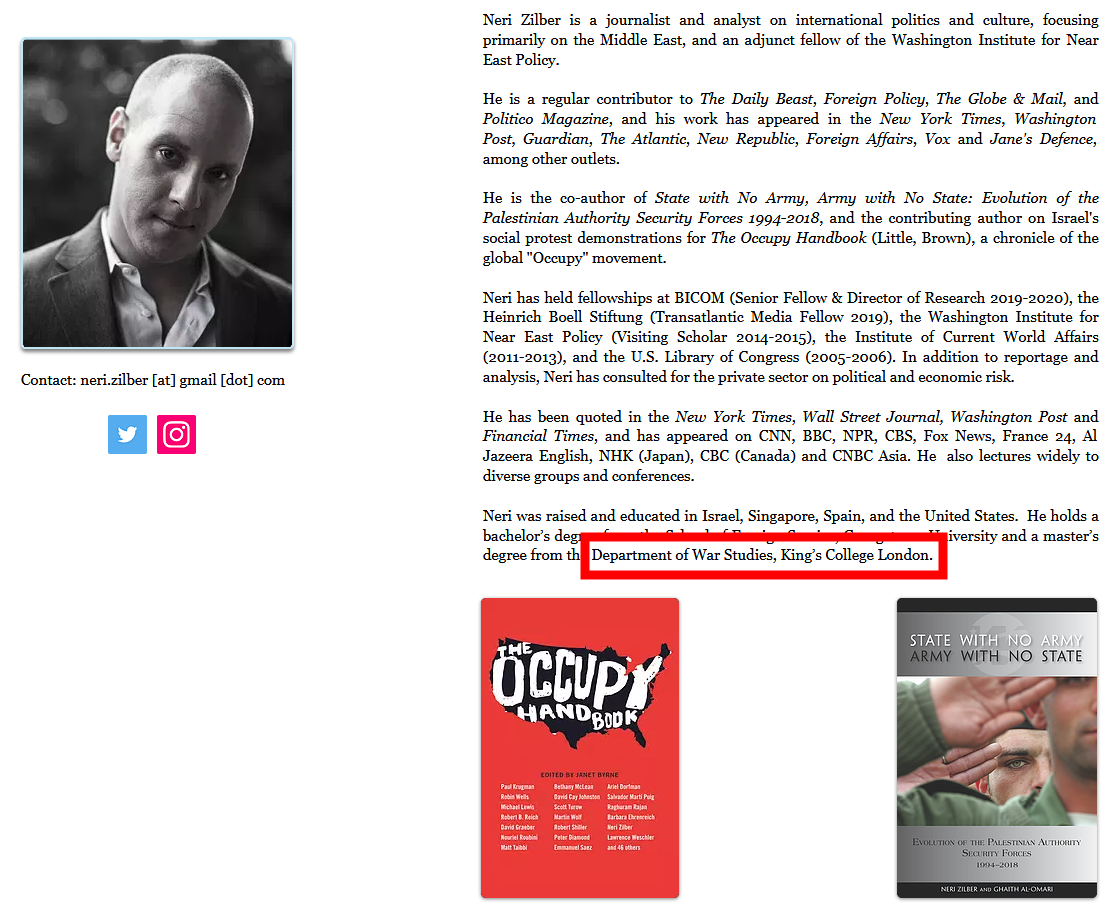
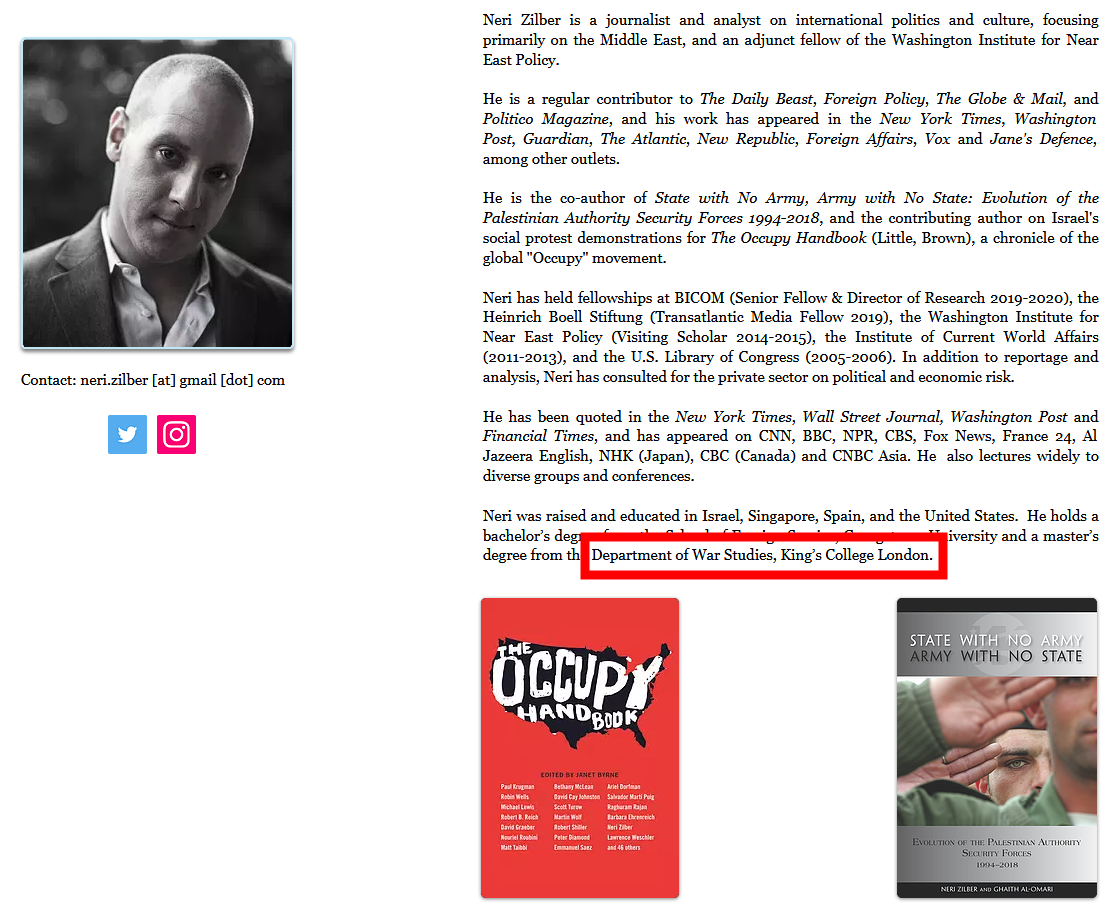
Israeli writer and King’s College alumnus Neri Zilber has bylines in many of the media’s most important outlets
The Department of War Studies also trains many international journalists and commentators, including Nicholas Stuart of the Canberra Times (Australia); Pakistani writer Ayesha Siddiqa, whose work can be found in The New York Times, Al-Jazeera, The Hindu and many other outlets; and Israeli writer Neri Zilber, a contributor to The Daily Beast, The Guardian, Foreign Policy and Politico.
What’s it all about?
Why are so many influential figures in our media being hothoused in a department well known for its connections to state power, for its faculty being active or former military or government officials, and for producing spies and operatives for various three-letter agencies? The point of this is not to allege that these journalists are all secretly card-carrying spooks: they are not. Rather, it is to highlight the alarmingly close links between the national security state and the fourth estate we rely on to be a check on their power and to hold them accountable.
Journalists trained in this sort of environment are far more likely to see the world in the same manner as their professors do. And perhaps they would be less likely to challenge state power when the officials they are scrutinizing were their classmates or teachers.
These sorts of questions abound when such a phenomenon exists: Why are so many journalists choosing to study at this particular department, and why do so many go on to be so influential? Are they being vetted by security agencies, with or without their knowledge? How independent are they? Will they just repeat British and American state talking points, as the Department of War Studies’ publications do?
On the question of vetting, the BBC admitted that, at least until the 1990s, it conspired with domestic spying agency MI5 to make sure that people with left-wing and/or anti-war leanings, or views critical of British foreign policy and empire were secretly blocked from being hired. When pressed on whether this policy is still ongoing, the broadcaster refused to comment, citing “security issues” — a response that is unlikely to reassure skeptics.
“While it strikes me as very interesting that a single academic institution could play such a major role in the recruitment of pro-establishment activist intellectuals and delivery of the same to the media, it is not so surprising,” Oliver Boyd-Barrett, Professor Emeritus at Bowling Green State’s School of Media and Communication and an expert in collusion between government and media, told MintPress, adding:
Elite institutions in the past and doubtless still today have been major playgrounds for intelligence services. The history of the modern nation-state generally, not just the USA, seems to suggest that national unity — and therefore elite safety — is regarded by elites as achievable only through careful management and often suppression or diversion of dissent. Far more resources are typically committed to this than many citizens, drilled in the propaganda of democracy, realize or care to concede.
The Bellingcat Boys
While the journalists cataloged above are not spooks, some other Department of War Studies figures working in journalism could possibly be described as such, particularly those around the influential and increasingly notorious investigative website Bellingcat.
Cameron Colquhoun, for instance, spent almost a decade at GCHQ, Britain’s version of the NSA, where he was a senior analyst running cyber and counter-terrorism operations. He holds qualifications from both King’s College London and the State Department. This background is not disclosed in his Bellingcat profile, which merely describes him as the managing director of a private intelligence company that “conduct[s] ethical investigations” for clients around the world.
Bellingcat’s senior investigator Nick Waters spent four years as an officer in the British Army, including a tour in Afghanistan, where he furthered the British state’s objectives in the region. After that, he joined the Department of War Studies and Bellingcat.
For the longest time, Bellingcat’s founder Eliot Higgings dismissed charges that his organization was funded by the U.S. government’s National Endowment for Democracy (NED) — a CIA cutout organization — as a ridiculous “conspiracy.” Yet by 2017, he was admitting that it was true. A year later, Higgins joined the Department of War Studies as a visiting research associate. Between 2016 and 2019 he was also a senior fellow at the Atlantic Council, the brains behind the North Atlantic Treaty Organization (NATO).
https://twitter.com/adamjohnsonNYC/status/828554021405339648?ref_src=twsrc%5Etfw%7Ctwcamp%5Etweetembed%7Ctwterm%5E828554441485869056%7Ctwgr%5E%7Ctwcon%5Es2_&ref_url=https%3A%2F%2Fwww.mintpressnews.com%2Fspy-school-kings-college-london-churning-out-journalists%2F277582%2F
Higgins appears to have used the university department as a recruiting ground, commissioning other War Studies graduates, such as Jacob Beeders and the aforementioned Christiaan Triebert and Aliaume Leroy, to write for his site.
Bellingcat is held in very high regard by the CIA. “I don’t want to be too dramatic, but we love [Bellingcat],” said Marc Polymeropoulos, the agency’s former deputy chief of operations for Europe and Eurasia. Other officers explained that Bellingcat could be used to outsource and legitimize anti-Russia talking points. “The greatest value of Bellingcat is that we can then go to the Russians and say ‘there you go’ [when they ask for evidence],” added former CIA Chief of Station Daniel Hoffman.
Bellingcaught
A recent MintPress investigation explored how Bellingcat acts to launder national security state talking points into the mainstream under the guise of being neutral investigative journalists themselves.
Newly leaked documents show how Bellingcat, Reuters and the BBC were covertly cooperating with the U.K.’s Foreign and Commonwealth Office (FCO) to undermine the Kremlin and promote regime change in Moscow. This included training journalists and promoting explicitly anti-Russian media across Eastern Europe. Unfortunately, the FCO noted, Bellingcat had been “somewhat discredited,” as it constantly spread disinformation and was willing to produce reports for anyone with money.
Nevertheless, a new European Parliament proposal published last month recommends hiring Bellingcat to assist in producing reports that would lay the groundwork for sanctioning Russia, for throwing it out of international bodies, and to “assist Russia’s transformation into a democracy.” In other words, to overthrow the government of Vladimir Putin.
An academic journalistic nexus
The Department of War Studies is also part of this pro-NATO, anti-Russia group. Quite apart from being staffed by soldiers, spooks and government officials, it puts out influential reports advising Western governments on foreign and defense policy. For instance, a study entitled “The future strategic direction of NATO” advises that member states must increase their military budgets and allow American nuclear weapons to be stored in their countries, thereby “shar[ing] the burden.” It also recommended that NATO must redouble its commitment to opposing Russia while warning that it needed urgently to form a “coherent policy” on the Chinese threat.
Other War Studies reports claim that Russia is carrying out “information-psychological warfare” through its state channels RT and Sputnik, and counsel that the West must use its technical means to prevent its citizens from consuming this foreign propaganda.
King’s College London academics have also proven crucial in keeping dissident publisher Julian Assange imprisoned. A psychiatrist who has worked with the War Studies department testified in court that the Australian was suffering only “moderate” depression and that his suicide risk was “manageable,” concluding that extraditing him to the United States “would not be unjust.” As Matt Kennard’s investigation found, the U.K. Ministry of Defence had provided £2.2 million ($3.1 million) in funding to the institute where he worked (although the psychiatrist in question claimed his work was not directly funded by the MoD).
King’s College London markets the War Studies department to both graduates and undergraduates as a stepping stone towards a career in journalism. In its “career prospects” section for its master’s course in war studies, it tells interested students that “graduates go on to work for NGOs, the FCO, the MoD, the Home Office, NATO, the UN or pursue careers in journalism, finance, academia, the diplomatic services, the armed forces and more.”
Likewise, undergraduates are told that:
You will gain an in-depth and sophisticated understanding of war and international relations, both as subjects worthy of study and as intellectual preparation for the widest possible range of career choices, including in government, journalism, research, and humanitarian and international organisations.
Courses such as “New Wars, New Media, New Journalism” fuse together journalism and intelligence and are overseen by War Studies academics.
It is perhaps unsurprising that the department has taught many influential politicians, including foreign heads of state and members of the British parliament. But at least there is considerable overlap between the fields of defense policy and politics. The fact that the very department that trains high state officials and agents of secretive three letter agencies is also the place that produces many of the journalists we rely on to stand up to those officials and keep them in check is seriously problematic.
An unhealthy respect for authority
Unfortunately, rather than challenging power, many modern media outlets amplify its message uncritically. State officials and intelligence officers are among the least trustworthy sources, journalistically speaking. Yet many of the biggest stories in recent years have been based on nothing except the hearsay of officials who would not even put their names to their claims.
The level of credulity modern journalists have for the powerful was summed up by former CNN White House Correspondent Michelle Kosinski, who last month stated that:
As an American journalist, you never expect:
- Your own govt to lie to you, repeatedly
- Your own govt to hide information the public has a right to know
- Your own govt to spy on your communications
Unfortunately, credulity stretches into outright collaboration with intelligence in some cases. Leaked emails show that the Los Angeles Times’ national security reporter Ken Dilanian sent his articles directly to the CIA to be edited before they were published. Far from hurting his career, however, Dilanian is now a correspondent covering national security issues for NBC News.
Boyd-Barrett said that governments are dependent on “the assistance of a penetrated, colluding and docile mainstream media which of late — and in the context of massive confusion over Internet disinformation campaigns, real and alleged — appear ever more problematic guardians of the public right to know.”
In recent years, the national security state has increased its influence over social media giants as well. In 2018, Facebook and the Atlantic Council entered a partnership whereby the Silicon Valley giant partially outsourced curation of its 2.8 billion users’ news feeds to the Council’s Digital Forensics Lab, supposedly to help stop the spread of fake news online. The result, however, has been the promotion of “trustworthy” corporate media outlets like Fox News and CNN and the penalization of independent and alternative sources, which have seen their traffic decrease precipitously. Earlier this year, Facebook also hired former NATO press officer and current Senior Fellow at the Atlantic Council Ben Nimmo to be its chief of intelligence. Reddit’s Director of Policy is also a former Atlantic Council official.
Meanwhile, in 2019, a senior Twitter executive for the Middle East region was unmasked as an active duty officer in the British Army’s 77th Brigade, its unit dedicated to psychological operations and online warfare. The most notable thing about this event was the almost complete lack of attention it received from the mainstream press. Coming at a time when foreign interference online was perhaps the number one story dominating the news cycle, only one major outlet, Newsweek, even mentioned it. Furthermore, the reporter who covered the story left his job just weeks later, citing stifling top-down censorship and a culture of deference to national security interests.
The purpose of this article is not to accuse any of those mentioned of being intelligence agency plants (although at least one person did actually work as an intel officer). The point is rather to highlight that we now have a media landscape where many of the West’s most influential journalists are being trained by exactly the same people in the same department as the next generation of national security operatives.
It is hardly a good look for a healthy, open democracy that so many spies, government officials, and journalists trusted to hold them accountable on our behalf are all being shot out of the very same cannon. Learning side by side has helped to create a situation where the fourth estate has become overwhelmingly deferential to the so-called deep state, where anonymous official’s words are taken as gospel. The Department of War Studies is just one part of this wider phenomenon.T
Alan MacLeod is Senior Staff Writer for MintPress News. After completing his PhD in 2017 he published two books: Bad News From Venezuela: Twenty Years of Fake News and Misreporting and Propaganda in the Information Age: Still Manufacturing Consent, as well as a number of academic articles.
June 5, 2021
Posted by aletho |
Deception, Mainstream Media, Warmongering, Timeless or most popular | BBC, Bellingcat, CIA, GCHQ, Los Angeles Times, NED, Reuters, Twitter, UK, United States |
Leave a comment
A major cyber attack that has hit US government agencies is also believed to have affected a small number of British organizations.
According to Sky News, British officials are “investigating” as to whether government departments have been affected by the big breach.
Hitherto, it is believed only private British companies have been affected.
Paul Chichester, the director of operations at the National Cyber Security Centre (NCSC), which is an extension of the GCHQ signals intelligence organization, has urged British companies to take “immediate steps” to protect their networks.
“This is a complex, global cyber incident, and we are working with international partners to fully understand its scale and any UK impact”, Chichester told Sky News.
“The NCSC is working to mitigate any potential risk, and actionable guidance has been published on our website”, he added.
Meanwhile, one of the directors of a leading British cyber security company has claimed the attacks could be the most “impactful national security [cyber] breach” that has ever been seen.
John Hultquist, who is senior director of analysis at Mandiant Solutions (which is part of the cyber security company FireEye), told Sky News that: “They [the hackers] managed clearly to gain access to a lot of secure areas. They are going to be very hard to get out”.
FireEye reportedly was the first cyber security company to discover the trans-Atlantic breach.
Yet another major figure in the British cyber security world echoed Hultquist’s assessment by describing the latest breach is “one of the most significant cyber attacks, really that’s ever been seen”.
Ciaran Martin, who is the founder and former head of the NCSC, told Sky News the attack was motivated by “traditional espionage”.
However, Martin, who is currently an academic at the Blavatnik School of Government at Oxford University, cautioned that “it remains to be seen, what the final picture [about the hacking] tells us”.
US media, in addition to British security sources, have reflexively blamed the hacking on Russia’s foreign intelligence service (SVR) without furnishing any evidence.
December 19, 2020
Posted by aletho |
Deception, False Flag Terrorism, Mainstream Media, Warmongering | GCHQ, UK |
Leave a comment
In just the past week, the national-security states of the United States and United Kingdom have discreetly let it be known that the cyber tools and online tactics previously designed for use in the post-9/11 “war on terror” are now being repurposed for use against information sources promoting “vaccine hesitancy” and information related to Covid-19 that runs counter to their state narratives.
A new cyber offensive was launched on Monday by the UK’s signal intelligence agency, Government Communications Headquarters (GCHQ), which seeks to target websites that publish content deemed to be “propaganda” that raises concerns regarding state-sponsored Covid-19 vaccine development and the multi-national pharmaceutical corporations involved.
Similar efforts are underway in the United States, with the US military recently funding a CIA-backed firm—stuffed with former counterterrorism officials who were behind the occupation of Iraq and the rise of the so-called Islamic State—to develop an AI algorithm aimed specifically at new websites promoting “suspected” disinformation related to the Covid-19 crisis and the US military–led Covid-19 vaccination effort known as Operation Warp Speed.
Both countries are preparing to silence independent journalists who raise legitimate concerns over pharmaceutical industry corruption or the extreme secrecy surrounding state-sponsored Covid-19 vaccination efforts, now that Pfizer’s vaccine candidate is slated to be approved by the US Food and Drug Administration (FDA) by month’s end.
Pfizer’s history of being fined billions for illegal marketing and for bribing government officials to help them cover up an illegal drug trial that killed eleven children (among other crimes) has gone unmentioned by most mass media outlets, which instead have celebrated the apparently imminent approval of the company’s Covid-19 vaccine without questioning the company’s history or that the mRNA technology used in the vaccine has sped through normal safety trial protocols and has never been approved for human use. Also unmentioned is that the head of the FDA’s Center for Drug Evaluation and Research, Patrizia Cavazzoni, is the former Pfizer vice president for product safety who covered up the connection of one of its products to birth defects.
Essentially, the power of the state is being wielded like never before to police online speech and to deplatform news websites to protect the interests of powerful corporations like Pfizer and other scandal-ridden pharmaceutical giants as well as the interests of the US and UK national-security states, which themselves are intimately involved in the Covid-19 vaccination endeavor.
UK Intelligence’s New Cyberwar Targeting “Anti-Vaccine Propaganda”
On Monday, the UK newspaper The Times reported that the UK’s GCHQ “has begun an offensive cyber-operation to disrupt anti-vaccine propaganda being spread by hostile states” and “is using a toolkit developed to tackle disinformation and recruitment material peddled by Islamic State” to do so. In addition, the UK government has ordered the British military’s 77th Brigade, which specializes in “information warfare,” to launch an online campaign to counter “deceptive narratives” about Covid-19 vaccine candidates.
The newly announced GCHQ “cyber war” will not only take down “anti-vaccine propaganda” but will also seek to “disrupt the operations of the cyberactors responsible for it, including encrypting their data so they cannot access it and blocking their communications with each other.” The effort will also involve GCHQ reaching out to other countries in the “Five Eyes” alliance (US, Australia, New Zealand and Canada) to alert their partner agencies in those countries to target such “propaganda” sites hosted within their borders.
The Times stated that “the government regards tackling false information about inoculation as a rising priority as the prospect of a reliable vaccine against the coronavirus draws closer,” suggesting that efforts will continue to ramp up as a vaccine candidate gets closer to approval.
It seems that, from the perspective of the UK national-security state, those who question corruption in the pharmaceutical industry and its possible impact on the leading experimental Covid-19 vaccine candidates (all of which use experimental vaccine technologies that have never before been approved for human use) should be targeted with tools originally designed to combat terrorist propaganda.
While The Times asserted that the effort would target content “that originated only from state adversaries” and would not target the sites of “ordinary citizens,” the newspaper suggested that the effort would rely on the US government for determining whether or not a site is part of a “foreign disinformation” operation.
This is highly troubling given that the US recently seized the domains of many sites, including the American Herald Tribune, which it erroneously labeled as “Iranian propaganda,” despite its editor in chief, Anthony Hall, being based in Canada. The US government made this claim about the American Herald Tribune after the cybersecurity firm FireEye, a US government contractor, stated that it had “moderate confidence” that the site had been “founded in Iran.”
In addition, the fact that GCHQ has alleged that most of the sites it plans to target are “linked to Moscow” gives further cause for concern given that the UK government was caught funding the Institute for Statecraft’s Integrity Initiative, which falsely labeled critics of the UK government’s actions as well as its narratives with respect to the Syria conflict as being related to “Russian disinformation” campaigns.
Given this precedent, it is certainly plausible that GCHQ could take the word of either an allied government, a government contractor, or perhaps even an allied media organization such as Bellingcat or the Atlantic Council’s DFRLab that a given site is “foreign propaganda” in order to launch a cyber offensive against it. Such concerns are only amplified when one of the main government sources for The Times article bluntly stated that “GCHQ has been told to take out antivaxers [sic] online and on social media. There are ways they have used to monitor and disrupt terrorist propaganda,” which suggests that the targets of GCHQ’s new cyber war will, in fact, be determined by the content itself rather than their suspected “foreign” origin. The “foreign” aspect instead appears to be a means of evading the prohibition in GCHQ’s operational mandate on targeting the speech or websites of ordinary citizens.
This larger pivot toward treating alleged “anti-vaxxers” as “national security threats” has been ongoing for much of this year, spearheaded in part by Imran Ahmed, the CEO of the UK-based Center for Countering Digital Hate, a member of the UK government’s Steering Committee on Countering Extremism Pilot Task Force, which is part of the UK government’s Commission for Countering Extremism.
Ahmed told the UK newspaper The Independent in July that “I would go beyond calling anti-vaxxers conspiracy theorists to say they are an extremist group that pose a national security risk.” He then stated that “once someone has been exposed to one type of conspiracy it’s easy to lead them down a path where they embrace more radical world views that can lead to violent extremism,” thereby implying that “anti-vaxxers” might engage in acts of violent extremism. Among the websites cited by Ahmed’s organization as promoting such “extremism” that poses a “national security risk” were Children’s Health Defense, the National Vaccine Information Center, Informed Consent Action Network, and Mercola.com, among others.
Similarly, a think tank tied to US intelligence—whose GCHQ equivalent, the National Security Agency, will take part in the newly announced “cyber war”—argued in a research paper published just months before the onset of the Covid-19 crisis that “the US ‘anti-vaxxer’ movement would pose a threat to national security in the event of a ‘pandemic with a novel organism.’”
InfraGard, “a partnership between the Federal Bureau of Investigation (FBI) and members of the private sector,” warned in the paper published last June that “the US anti-vaccine movement would also be connected with ‘social media misinformation and propaganda campaigns’ orchestrated by the Russian government,” as cited by The Guardian. The InfraGard paper further claimed that prominent “anti-vaxxers” are aligned “with other conspiracy movements including the far right . . . and social media misinformation and propaganda campaigns by many foreign and domestic actors. Included among these actors is the Internet Research Agency, the Russian government–aligned organization.”
An article published just last month by the Washington Post argued that “vaccine hesitancy is mixing with coronavirus denial and merging with far-right American conspiracy theories, including Qanon,” which the FBI named a potential domestic terror threat last year. The article quoted Peter Hotez, dean of the School of Tropical Medicine at Baylor College of Medicine in Houston, as saying “The US anti-vaccination movement is globalizing and it’s going toward more-extremist tendencies.”

Simone Warstat attends a rally against a legislative bill to make it more difficult for parents to opt out for non-medical reasons to immunize their children, June 7, 2020, in Denver Colorado.
It is worth pointing out that many so-called “anti-vaxxers” are actually critics of the pharmaceutical industry and are not necessarily opposed to vaccines in and of themselves, making the labels “anti-vaxxer” and “anti-vaccine” misleading. Given that many pharmaceutical giants involved in making Covid-19 vaccines donate heavily to politicians in both countries and have been involved in numerous safety scandals, using state intelligence agencies to wage cyber war against sites that investigate such concerns is not only troubling for the future of journalism but it suggests that the UK is taking a dangerous leap toward becoming a country that uses its state powers to treat the enemies of corporations as enemies of the state.
The CIA-Backed Firm “Weaponizing Truth” with AI
In early October, the US Air Force and US Special Operations Command announced that they had awarded a multimillion-dollar contract to the US-based “machine intelligence” company Primer. Per the press release, “Primer will develop the first-ever machine learning platform to automatically identify and assess suspected disinformation [emphasis added]. Primer will also enhance its natural language processing platform to automatically analyze tactical events to provide commanders with unprecedented insight as events unfold in near real-time.”
According to Primer, the company “builds software machines that read and write in English, Russian, and Chinese to automatically unearth trends and patterns across large volumes of data,” and their work “supports the mission of the intelligence community and broader DOD by automating reading and research tasks to enhance the speed and quality of decision-making.” In other words, Primer is developing an algorithm that would allow the national-security state to outsource many military and intelligence analyst positions to AI. In fact, the company openly admits this, stating that their current effort “will automate the work typically done by dozens of analysts in a security operations center to ingest all of the data relevant to an event as it happens and funnel it into a unified user interface.”
Primer’s ultimate goal is to use their AI to entirely automate the shaping of public perceptions and become the arbiter of “truth,” as defined by the state. Primer’s founder, Sean Gourley, who previously created AI programs for the military to track “insurgency” in post-invasion Iraq, asserted in an April blog post that “computational warfare and disinformation campaigns will, in 2020, become a more serious threat than physical war, and we will have to rethink the weapons we deploy to fight them.”
In that same post, Gourley argued for the creation of a “Manhattan Project for truth” that would create a publicly available Wikipedia-style database built off of “knowledge bases [that] already exist inside many countries’ intelligence agencies for national security purposes.” Gourley then wrote that “this effort would be ultimately about building and enhancing our collective intelligence and establishing a baseline for what’s true or not” as established by intelligence agencies. He concludes his blog post by stating that “in 2020, we will begin to weaponize truth.”
Notably, on November 9, the same day that GCHQ announced its plans to target “anti-vaccine propaganda,” the US website NextGov reported that Primer’s Pentagon-funded effort had turned its attention specifically to “Covid-19 related disinformation.” According to Primer’s director of science, John Bohannon, “Primer will be integrating bot detection, synthetic text detection and unstructured textual claims analysis capabilities into our existing artificial intelligence platform currently in use with DOD. . . . This will create the first unified mission-ready platform to effectively counter Covid-19-related disinformation in near-real time.”
Bohannon, who previously worked as a mainstream journalist embedded with NATO forces in Afghanistan, also told NextGov that Primer’s new Covid-19–focused effort “automatically classifies documents into one of 10 categories to enable the detection of the impact of COVID” on areas such as “business, science and technology, employment, the global economy, and elections.” The final product is expected to be delivered to the Pentagon in the second quarter of next year.
Though a so-called private company, Primer is deeply linked to the national-security state it is designed to protect by “weaponizing truth.” Primer proudly promotes itself as having more than 15 percent of its staff hailing from the US intelligence community or military. The director of the company’s National Security Group is Brian Raymond, a former CIA intelligence officer who served as the Director for Iraq on the US National Security Council after leaving the agency.
The company also recently added several prominent national-security officials to its board including:
- Gen. Raymond Thomas (ret.), who led the command of all US and NATO Special Operations Forces in Afghanistan and is the former commander of both US Special Operations Command and Joint Special Operations Command (JSOC).
- Lt. Gen. VeraLinn Jamieson (ret.), the former deputy chief of staff for Air Force Intelligence, Surveillance and Reconnaissance who led the Air Force’s intelligence and cyber forces. She also personally developed “strategic partnerships” between the Air Force and Microsoft, Amazon, Google, and IBM in order “to accelerate the Air Force’s digital transformation.”
- Brett McGurk, one of the “chief architects” of the Iraq War “surge,” alongside the notorious Kagan family, as NSC Director for Iraq, and then as special assistant to the president and senior Director for Iraq and Afghanistan during the Bush administration. Under Obama and during part of the Trump administration, McGurk was the special presidential envoy for the Global Coalition to Defeat ISIS at the State Department, helping to manage the “dirty war” waged by the US, the UK, and other allies against Syria.
In addition to those recent board hires, Primer brought on Sue Gordon, the former principal deputy director of National Intelligence, as a strategic adviser. Gordon previously “drove partnerships within the US Intelligence Community and provided advice to the National Security Council in her role as deputy director of national intelligence” and had a twenty-seven-year career at the CIA. The deep links are unsurprising, given that Primer is financially backed by the CIA’s venture-capital arm In-Q-Tel and the venture-capital arm of billionaire Mike Bloomberg, Bloomberg Beta.
Operation Warp Speed’s Disinformation Blitzkrieg
The rapid increase in interest by the US and UK national-security states toward Covid-19 “disinformation,” particularly as it relates to upcoming Covid-19 vaccination campaigns, is intimately related to the media-engagement strategy of the US government’s Operation Warp Speed.
Officially a “public-private partnership,” Operation Warp Speed, which has the goal of vaccinating 300 million Americans by next January, is dominated by the US military and also involves several US intelligence agencies, including the National Security Agency (NSA) and the Department of Homeland Security (DHS), as well as intelligence-linked tech giants Google, Oracle, and Palantir. Several reports published in The Last American Vagabond by this author and journalist Derrick Broze have revealed the extreme secrecy of the operation, its numerous conflicts of interest, and its deep ties to Silicon Valley and Orwellian technocratic initiatives.
Warp Speed’s official guidance discusses at length its phased plan for engaging the public and addressing issues of “vaccine hesitancy.” According to the Warp Speed document entitled “From the Factory to the Frontlines,” “strategic communications and public messaging are critical to ensure maximum acceptance of vaccines, requiring a saturation of messaging across the national media.” It also states that “working with established partners—especially those that are trusted sources for target audiences—is critical to advancing public understanding of, access to, and acceptance of eventual vaccines” and that “identifying the right messages to promote vaccine confidence, countering misinformation, and targeting outreach to vulnerable and at-risk populations will be necessary to achieve high coverage.”
The document also notes that Warp Speed will employ the CDC’s three-pronged strategic framework for its communications effort. The third pillar of that strategy is entitled “Stop Myths” and has as a main focus “establish[ing] partnerships to contain the spread of misinformation” as well as “work[ing] with local partners and trusted messengers to improve confidence in vaccines.”
Though that particular Warp Speed document is short on specifics, the CDC’s Covid-19 Vaccination Program Interim Playbook contains additional information. It states that Operation Warp Speed will “engage and use a wide range of partners, collaborations, and communication and news media channels to achieve communication goals, understanding that channel preferences and credible sources vary among audiences and people at higher risk for severe illness and critical populations, and channels vary in their capacity to achieve different communication objectives.” It states that it will focus its efforts in this regard on “traditional media channels” (print, radio, and TV) as well as “digital media” (internet, social media, and text messaging).
The CDC document further reveals that the “public messaging” campaign to “promote vaccine uptake” and address “vaccine hesitancy” is divided into four phases and adds that the overall communication strategy of Warp Speed “should be timely and applicable for the current phase of the Covid-19 Vaccination program.”
Those phases are:
- Before a vaccine is available
- The vaccine is available in limited supply for certain populations of early focus
- The vaccine is increasingly available for other critical populations and the general public
- The vaccine is widely available
Given that the Covid-19 vaccine candidate produced by Pfizer is expected to be approved by the end of November, it appears that the US national-security state, which is essentially running Operation Warp Speed, along with “trusted messengers” in mass media, is preparing to enter the second phase of its communications strategy, one in which news organizations and journalists who raise legitimate concerns about Warp Speed will be de-platformed to make way for the “required” saturation of pro-vaccine messaging across the English-speaking media landscape.
November 12, 2020
Posted by aletho |
Civil Liberties, Corruption, Full Spectrum Dominance, Science and Pseudo-Science, Timeless or most popular | CIA, Covid-19, COVID-19 Vaccine, DHS, GCHQ, Human rights, NSA, Operation Warp Speed, UK, United States |
Leave a comment
The sensational headlines screaming on the front pages of British newspapers this week showed that the parliamentary Russia Report was a triumph of bombast.
The Daily Mail led with “Damning Russia Dossier” while The Times heralded “MI5 to get more powers” and “Tough new laws will combat threat of Russian spies”. The Times also splashed its front page with a large photograph of Russian President Vladimir Putin seemingly lurking behind a curtain, which just goes to show how much British journalism has descended into cartoonish trivia.
There is sound reason why the British government delayed until this week publication of the so-called Russia Report by a cross-party parliamentary committee. That’s plainly because there is nothing in it that could in any way substantiate lurid claims of alleged Russian interference in British politics.
The 55-page document was neither “damning” nor “devastating” as The Daily Mail asserted. The groundless hype suggests that the headline writers simply were looking for something to sell to readers regardless of facts.
Boris Johnson, the prime minister, received a copy of the report 10 months ago, but decided to postpone its publication until after the general election that was held in December. That delay led to claims that his Conservative government was hiding something sinister. There were procedural hiccups from the Intelligence and Security Committee (ISC) being replaced with new members. However, now that the report is published any rational reader can see that the real cause of the delay is down to the report being a dud, despite all the breathless speculation. It is an empty vessel, with no evidence or substantive detail. It consists of entirely prejudiced assertions that Russia is “a hostile state” and the UK “is clearly a target for Russia disinformation campaigns and political influence”.
The nine lawmakers on the committee and their nine predecessors acknowledge among their sources for the report the following individuals: Anne Applebaum, William Browder and Christopher Steele. All of them are zealously anti-Russia and are prodigious purveyors of “Russian interference” narratives to anyone who will listen to them. Steele is the notorious former MI6 spy who cooked up the ludicrous “Russia Dossier” for the Democrats to smear Trump with in the 2016 elections. That dossier fueled the bogus “Russiagate” scandal.
Of course, the main sources for the parliamentary committee are British intelligence agencies, MI6, MI5 and GCHQ. Candid admission of all those sources should underscore with redlines that the so-called report is nothing but a propaganda screed. Yet the British media treat it with deference and respect as if it is a credible, objective assessment.
What is rather laughable is the unrestrained prejudice of the authors who are, in reality, propagandists more suited to being frozen in Cold War mentality than offering any kind of “expertise”. They claim Russian politics is “paranoid” and “nihilistic” driven by “zero-sum calculation”. All those attributed defects are merely self-projection by the authors of this report and their sources.
It is rather telling that in place of anything resembling substance of alleged Russian interference, the parliamentarians refer to “open sources” of media influence by Russian state-owned RT and Sputnik. They accuse these media of “direct support of a pro-Russian narrative in relation to particular events”. Oh, how shocking! And the British state-owned BBC does not also do the same?
Again referring to “open sources” – meaning public media reports – the parliamentarians claim that the Kremlin interfered in the Scottish referendum on independence back in 2014. So just because Russian news media featured that subject in its coverage is supposed to be “evidence” of Kremlin interference. The absurd accusation is also a convenient way to smear Scottish pro-independence.
Oddly enough, the report says there was no manifest Russian interference in the 2016 Brexit referendum. Well that’s handy. The Tory government wouldn’t want to smear its ambitions of reviving the British empire, that’s for sure.
The ISC publication is a self-serving dud that is “not worth a penny”, as Russian lawmaker Aleksy Chepa put it.
It is loaded with complacent British self-regard and knee-jerk Russophobia.
The parliamentarians repeatedly rebuke the British government and state intelligence for not taking the “threat” of alleged Russian meddling seriously enough.
A more plausible explanation is because there is negligible Russian meddling in British politics, as Moscow has consistently stated. If the British government and its spooks fail to get excited – in private – about allegations of Russian malfeasance it’s because there is actually nothing to the allegations. Still, the parliamentarian anti-Russia ideologues assume to know better. They are convinced that Britain is a target for Kremlin hostility and they lambast the government and intelligence services for “not making it a priority issue”.
The Orwellian plot thickens when the authors of the boilerplate Russian Report then conclude by urging MI5 to be given more secretive powers to collaborate with social media networks in order to control information in the name of combating a “hostile state threat”. This is a sinister, anti-democratic call worthy of a dictatorship for censoring and blackballing any dissenting views under the guise of “defending democracy”.
One area where the ISC document begins to deal with reality – but only superficially and misleadingly – is on the subject of super-rich Russian expatriates living in London, which is dubbed “Londongrad”. Many of these oligarchs are beneficiaries of looting Russian state assets during the privatization-robbery frenzy under former President Boris Yeltsin. They are not “friends of Putin” as the British lawmakers make out. These shady oligarchs are often big donors to the Conservative party, not because they want to inject pro-Russian influence, but rather because they are typically opposed to the current Russian government and are seeking to destabilize it. If there is any Russian “influence” in British politics it is that which promotes illegal regime-change policies in opposition to the Russian state.
In every aspect the much-vaunted Russia Report is a worthless pile of propaganda. Even a glimmer resembling something real – the Russian oligarchs in Londongrad – turns out to be an inversion of reality. And yet, pathetically, the British media amplify the nonsense with reverence and gravitas.
July 24, 2020
Posted by aletho |
Deception, Fake News, Mainstream Media, Warmongering, Russophobia | GCHQ, MI5, MI6, UK |
Leave a comment
Britain’s national press is acting largely as a platform for the views of the UK military and intelligence establishment, new statistical research by Declassified UK shows.
The UK press, from The Times to The Guardian, is also routinely helping to demonise states identified by the British government as enemies, while tending to whitewash those seen as allies.
The research, which analyses the UK national print media, suggests that the public is being bombarded by views and selective information supporting the priorities of policy-makers. The media is found to be routinely misinforming the public and acting far from independently.
This is the second part of a two-part analysis of UK national press coverage of British foreign policy.
Elite platform
Numerous stories or points of information on Britain’s intelligence agencies, such as MI6 and GCHQ, are being fed to journalists by anonymous “security sources” – often military or intelligence officials who do not want to be named.
The term “security sources” has been mentioned in 1,020 press articles in the past three years alone, close to one a day. While not all of these relate to UK sources, it indicates the common use of this method by British journalists.
Declassified’s recent research found that officials in the UK military and intelligence establishment had been sources for at least 34 major national media stories that cast Labour leader Jeremy Corbyn as a danger to British security. The research also found 440 articles in the UK press from September 2015 until December 2019 specifically mentioning Corbyn as a “threat to national security”.
Anonymous sources easily push out messages supportive of government policy and often include misleading or unverifiable information with no come-back from journalists. The Ministry of Defence (MOD) says it has 89 “media relations and communications” officers.
Many journalists regularly present the views of the MOD or security services to the public with few or no filters or challenges, merely amplifying what their sources tell them. In “exclusive” interviews with MI6 or MI5, for example, journalists invariably allow the security services to promote their views without serious, or any, scepticism for their claims or relevant context.
That the UK intelligence services are regularly presented as politically neutral actors and the bearers of objective information is exemplified in headlines such as “MI6 lays bare the growing Russian threat” (in the Times) and “Russia and Assad regime ‘creating a new generation of terrorists who will be threat to us all’, MI6 warns” (in the Independent).
Press coverage of the RAF’s 100th “birthday” in 2018 produced no critical articles that could be found, with most being stories from the MOD presented as news. This is despite episodes in the RAF’s history such as the bombing of civilians in colonial campaigns in the Middle East in the 1920s, 1930s and 1950s and its prominent current role in supporting Saudi airstrikes in Yemen, which has helped create the world’s biggest humanitarian disaster.
Similarly, for GCHQ’s 100th anniversary in 2019, the press appeared to simply write up information provided by the organisation. Only the occasional article mentioned GCHQ’s role in operating programmes of mass surveillance while its covert online action programmes and secret spy bases in at least one repressive Middle East regime were ignored by every paper at the time, as far as could be found.
The national press are generally strong supporters of the security services and the military. A number of outlets, from the Times and Telegraph to the Mirror, are strongly opposed to government cuts in parts of the military budget, for example.
The British army’s main special forces unit, the SAS, which is currently involved in seven covert wars, is invariably seen positively in the national press. A search reveals 384 mentions of the term “SAS hero” in the UK national press in the past five years – mainly in the Sun, but also in the Times, Express, Mail, Telegraph and others.
Critical articles on the special forces are rare, and the journalists writing them can face a backlash from other reporters.
In some press articles, MOD media releases are largely copied and pasted. For example, recent MOD material on RAF Typhoons in Eastern Europe scrambling to intercept Russian aircraft has often been repeated word for word across the media.

A press release from the UK’s Royal Air Force, and how it was covered by two British newspapers, The Sun and The Independent.
Such “embedded journalism” poses a significant threat to the public interest. Richard Norton-Taylor, formerly the Guardian’s security correspondent for over 40 years, told Declassified : “Embedded journalists — those invited to join British military units in conflict zones — are at the mercy of their MOD handlers at the best of times. Journalists covering defence, security and intelligence are far too deferential and indulge far too much in self-censorship”.
Some papers are more extreme than others in their willingness to act as platforms for the military and intelligence establishment. The Express may well be the most supportive: its coverage of MOD stories and vilification of official enemies, notably Russia, is remarkable and consistent.
The Guardian, however, has also been shown to play a similar role. Declassified’s recent analysis, drawing on newly released documents and evidence from former and current Guardian journalists, found that the paper has been successfully targeted by security agencies to neutralise its adversarial reporting of the “security state”.
Censorship by omission
Articles critical of the Ministry of Defence or security services are occasionally published in the press. However, these tend to be either on relatively minor issues or are reported on briefly and then forgotten. Rarely do seriously critical stories receive sustained coverage or are widely picked up across the rest of the media.
Often, reporters will cover a topic and elide the most important information for no clear reason. For example, there is considerable coverage of possible MI5 failures to prevent the May 2017 Manchester terrorist bombing — failings which may be understandable given the large number of terrorist suspects being monitored at any one time.
However, the government admitted in parliament in March 2018 that it “likely” had contacts with two militant groups in the 2011 war in Libya for which the Manchester bomber and his father reportedly fought at the time, one of which groups the UK had covertly supported in the past. This significant admission in parliament has not been reported in any press article, as far as can be found.

People lay flowers in St Annes Square on the first anniversary of the Manchester Arena bombing in Manchester, Britain, 22 May 2018. (Photo: EPA-EFE / Nigel Roddis)
Last September, veteran investigative journalist Ian Cobain broke a story on the alternative news site Middle East Eye revealing that the senior Twitter executive with editorial responsibility for the Middle East is also a part-time officer in the British army’s psychological warfare unit, the so-called 77th Brigade.
This story was picked up by a few media outlets at the time (including the Financial Times, the Times and the Independent ) but our research finds that it then went unmentioned in the hundreds of press articles subsequently covering Twitter.
Similarly, in November 2018, a story broke on a secretive UK government-financed programme called the Integrity Initiative, which is ostensibly a “counter disinformation” programme to challenge Russian information operations but was also revealed to be tweeting messages attacking Labour leader Jeremy Corbyn.
Our research finds that in the 14 months until December 2019, the Integrity Initiative was mentioned less than 20 times in the UK-wide national press, mainly in the Times (it was also mentioned 15 times in the Scottish paper, the Sunday Mail ).
By contrast, when stories break that are useful to the British establishment, they tend to receive sustained media coverage.
Establishment think tanks
The British press routinely chooses to rely on sources in think tanks that largely share the same pro-military and pro-intervention agenda as the state.
The two most widely-cited military-related think tanks in the UK are the London-based Royal United Services Institute (RUSI) and the International Institute for Strategic Studies (IISS) which are usually quoted as independent voices or experts. In the last five years, RUSI has appeared in 534 press articles and IISS in 120.
However, both are funded by governments and corporations. RUSI, which is located next door to the Ministry of Defence in Whitehall, has funders such as BAE Systems, the Qatar government, the Foreign Office and the US State Department. IISS’s chief financial backers include BAE Systems, Raytheon, Lockheed Martin and Airbus.
This funding is mentioned in only two press reports that could be found – the Guardian reported that IISS received money from the regime in Bahrain while the Times once noted, “RUSI, while funded in part by the MoD, is an independent think tank”.
One Telegraph article refers to a “research fellow at RUSI who specialises in combat airpower”, without mentioning that its funder BAE Systems is a major producer of warplanes.
Although many senior figures in these organisations previously worked in government, press readers are rarely informed of this. RUSI’s chair is former foreign secretary William Hague, its vice-chair is former MI6 director Sir John Scarlett and its senior vice-president is David Petraeus, former CIA director.
The IISS’s deputy secretary-general is a former senior official at the US State Department while its Middle East director is a former Lieutenant-General in the British army who served as defence senior adviser to the Middle East. One of IISS’ senior advisers is Nigel Inkster, a former senior MI6 officer.
Media and intelligence
Richard Keeble, professor of journalism at the University of Lincoln, has noted that the influence of the intelligence services on the media may be “enormous” and the British secret service may even control large parts of the press. “Most tabloid newspapers – or even newspapers in general – are playthings of MI5”, says Roy Greenslade, a former editor of the Daily Mirror who has also worked as media specialist for both the Telegraph and the Guardian.
David Leigh, former investigations editor of the Guardian, has written that reporters are routinely approached and manipulated by intelligence agents, who operate in three ways: they attempt to recruit journalists to spy on other people or go themselves under journalistic “cover”, they pose as journalists in order to write tendentious articles under false names, and they plant stories on willing journalists, who disguise their origin from their readers — known as black propaganda.
MI6 managed a psychological warfare operation in the run-up to the Iraq war of 2003 that was revealed by former UN arms inspector Scott Ritter. Known as Operation Mass Appeal, this operation “served as a focal point for passing MI6 intelligence on Iraq to the media, both in the UK and around the world. The goal was to help shape public opinion about Iraq and the threat posed by WMD [weapons of mass destruction]”.
Various fabricated reports were written up in the media in the run-up to the Iraq war, based on intelligence sources. These included cargo ships said to be carrying Iraqi weapons of mass destruction (covered in the Independent and Guardian ) and claims that Saddam Hussein killed his missile chief to thwart a UN team (Sunday Telegraph ).
More recent examples of apparently fabricated stories in the establishment media include Guardian articles on the subject of Julian Assange. The paper claimed in a front page splash written by Luke Harding and Dan Collyns in November 2018 that former Trump campaign manager Paul Manafort secretly met Assange in the Ecuadorian embassy three times.
The Guardian also falsely reported on a “Russia escape plot” to enable Assange to leave the embassy for which the paper later gave a partial apology. Both stories appeared to be part of a months-long campaign by the Guardian against Assange.

The exterior view of Thames House, MI5 Headquarters, in Millbank, on the bank of the River Thames, London, Britain. (Photo: EPA-EFE/ Horacio Villalobos)
Demonising enemies
The media plays a consistent role in following the state’s demonisation of official enemies. The term “Russian threat” is mentioned in 401 articles in the past five years, across the national press. The Express may be the largest press amplifier of the government’s demonisation of Russia — the paper carries a steady stream of stories critical of Russia and Putin.
The British establishment has invoked Russia as an enemy in recent years due mainly to the poisonings in the town of Salisbury and policy in eastern Europe. Whatever malign policies Russia is promoting, which can be real, false or exaggerated, it is noteworthy that this has been elevated by the press to a general “threat” to the UK. As during the cold war, this is useful to the British military and security services arguing for larger budgets and for offensive military postures in Eastern Europe and the Middle East.
Russia’s alleged interference in British politics has received huge coverage compared to alleged Israeli influence. A simple comparison of search terms using “Russia/Israel and UK and interference” in press articles in the past five years yields seven times more mentions of Russia than Israel, despite considerable evidence of Israeli interference.
UK press reporting on Iran is also noticeably supportive of government policy. A search for “Iran and nuclear weapons programme” reveals 325 articles in the past five years. While this large coverage is driven by president Trump’s withdrawal from the Iran nuclear deal, it is also driven by Iran being a designated enemy of the US and UK, which have deemed it unacceptable that Tehran should ever acquire nuclear weapons.
By contrast, “Israel’s nuclear weapons” (and variants of this search term) are mentioned in under 30 press articles in the past five years. Natanz, Iran’s main nuclear arms facility, has been mentioned in around four times more press articles than Dimona, the Israeli nuclear site, in the past five years.
The contrast in reporting on Iran and Israel is striking since Iran does not possess nuclear weapons, and it is not certain that it seeks to, whereas Western ally Israel already has such weapons, estimated at around 80 warheads.

An aerial view of Israel’s nuclear site at Dimona. (Google Maps)
Labelling goodies and baddies
The national press strongly follows the government in labelling states as enemies or allies.
States favoured by the UK are mainly described in the press using the neutral term “government” rather the more critical term “regime”. In the past three years, for example, the term “Saudi government” has been used in 790 articles while “Saudi regime” is mentioned in 388. However, with Iran the number of instances is reversed: “Iranian government” is used in 419 articles whereas “Iranian regime” is mentioned in 456.
The same holds for other allies. The “Egyptian regime” receives 24 mentions while “Egyptian government” has 222, in the past three years. The “Bahraini regime” is mentioned in 10 articles while “Bahraini government” is mentioned in 60.
The precise term “Iranian-backed Houthi rebels”, referring to the war in Yemen, is mentioned in 198 articles in the last five years. However, the equivalent term for the UK backing the Saudis in Yemen (using search terms such as “UK-backed Saudis” or “British-backed Saudis”) appears in just three articles.
The pattern is also that the crimes of official enemies are covered extensively in the national press but those of the UK and its allies much less so, if at all.
Articles mentioning “war crimes and Syria” number 1,527 in the past five years compared to 495 covering “war crimes and Yemen”. While the press often reports that the Syrian government has carried out war crimes, most articles simply suggest or allege war crimes by the Saudis in Yemen.
Indeed, the UK press has been much more interested in covering the Syrian war—chiefly prosecuted by the UK’s opponents—than the Yemen war, where Britain has played a sustained widespread role. As a basic indicator, the specific term “war in Syria” is mentioned in well over double the number of articles as “war in Yemen” in the past five years.
Furthermore, government enemies are regularly described in the press as supporters of terrorism, which rarely applies to allies.
In the past three years 185 articles mention the term “sponsor of terrorism”, most referring to Iran, followed by Sudan and North Korea with the occasional mention of Libya and Pakistan. None specifically label UK allies Turkey or Saudi “sponsors of terrorism”, despite evidence of this in Syria and elsewhere, and none describe Britain or the US as such.
Some 102 articles in the past five years specifically mention Russia’s “occupation of Crimea”. However, despite some critical articles on UK policy towards the Chagos Islands in the Indian ocean—which were depopulated by the UK in the 1970s and which the US now uses as a military base—only two articles specifically mention the UK’s “occupation of Chagos” (or variants of this term).
Similar labelling prevails on opposition forces in foreign countries. Protesters in Hong Kong are routinely called “pro-democracy” by the press – the term has been mentioned in hundreds of articles in the past two years. However, protesters in UK allies Bahrain and Egypt have been referred to as “pro-democracy” in only a handful of cases, the research finds.
The special relationship
While demonising enemies, UK allies are regularly presented favourably in the press. This is especially true of the US, the UK’s key special relationship on which much of its global power rests. US foreign policy is routinely presented as promoting the same noble objectives as the UK and the press follows the US government line on many foreign policy issues.
The term “leader of the free world” to refer to the US has been used in over 1,500 articles in the past five years, invariably taken seriously across the media, without challenge or ridicule.
The view that the US promotes democracy is widely repeated across the press. A 2018 editorial in the Financial Times, written by its chief foreign affairs commentator Gideon Rachman, notes that, “Leading figures in both [US political] parties — from John Kennedy to Ronald Reagan through to the Bushes and Clintons — agreed that it was in US interests to promote free-trade and democracy around the world”. In 2017 Daniel McCarthy wrote in the Telegraph of “two decades of idealism in US foreign policy, of attempts to spread liberalism and democracy”.
It is equally common for the UK press to quote US figures on their supposed noble aims, without challenge. For example, the Sunday Times recently cited without comment the US state department saying “Promoting freedom, democracy and transparency and the protection of human rights are central to US foreign policy”.
The press often strongly criticises President Donald Trump, but often for betraying otherwise benign US values and policies that it assumes previous presidents have promoted. For example, Tom Leonard in the Daily Mail writes of “Mr Trump’s belief that US foreign policy should be guided by cold self-interest rather than protecting democracy and human rights”.
The Guardian is especially supportive of US foreign policy. A sub-heading to a recent article notes: “The US once led Western states’ support of democracy around the world, but under this president [Trump] that feels like a long time ago”. One of its main foreign affairs columnists, Simon Tisdall, recently wrote that the US fundamental “mission” was an “exemplary global vision of democracy, prosperity and freedom”, albeit one which has been distorted by the war on terror.
The Guardian regularly heaped praise on president Obama. An editorial in January 2017 commented that Obama was a “successful US leader” and that “internationally” his vision “could hardly be faulted for lack of ambition”. It also noted Obama’s “liberalism and ethics” and that: “Mr Obama has governed impeccably for eight years without any ethical scandal”.
Although the article noted US wars and civilian casualties in Yemen and Libya, the paper brushed these off, stating “But to ascribe the world’s tragedies to a single leader’s choices can be simplistic. The global superpower cannot control local dynamics”.
Research covered the period to the end of 2019 using the media search tool, Factiva. It analysed the “mainstream” UK-wide print media (dailies and Sundays) over different time scales, usually two or five years, as specified in the article. Media search engines cannot be guaranteed to work perfectly so additional research was sometimes undertaken.
Mark Curtis is the co-founder and editor of Declassified UK, an historian and author of five books on UK foreign policy. He tweets at: @markcurtis30.
March 11, 2020
Posted by aletho |
Deception, Fake News, Mainstream Media, Warmongering, Russophobia | GCHQ, MI5, MI6, The Guardian, UK |
Leave a comment
UK governments routinely claim to uphold national and international law. But the reality of British policies is quite different, especially when it comes to foreign policy and so-called ‘national security’. This explainer summarises 17 long-running government policies which violate UK domestic or international law.
British foreign secretary Dominic Raab recently described the “rule of international law” as one of the “guiding lights” of UK foreign policy. By contrast, the government regularly chides states it opposes, such as Russia or Iran, as violators of international law. These governments are often consequently termed “rogue states” in the mainstream media, the supposed antithesis of how “we” operate.
The following list of 17 policies may not be exhaustive, but it suggests that the term “rogue state” is not sensationalist or misplaced when it comes to describing Britain’s own foreign and “security” policies.
These serial violations suggest that parliamentary and public oversight over executive policy-making in the UK is not fit for purpose and that new mechanisms are needed to restrain the excesses of the British state.
The Royal Air Force’s drone war
Britain’s Royal Air Force (RAF) operates a drone programme in support of the US involving a fleet of British “Reaper” drones operating since 2007. They have been used by the UK to strike targets in Afghanistan, Iraq and Syria.
Four RAF bases in the UK support the US drone war. The joint UK and US spy base at Menwith Hill in Yorkshire, northern England, facilitates US drone strikes in Yemen, Pakistan and Somalia. US drone strikes, involving an assassination programme begun by president Barack Obama, are widely regarded as illegal under international law, breaching fundamental human rights. Up to 1,700 civilian adults and children have been killed in so-called “targeted killings”.
Amnesty International notes that British backing is “absolutely crucial to the US lethal drones programme, providing support for various US surveillance programmes, vital intelligence exchanges and in some cases direct involvement from UK personnel in identifying and tracking targets for US lethal operations, including drone strikes that may have been unlawful”.
Chagos Islands
Britain has violated international law in the case of the Chagos Islands in the Indian Ocean since it expelled the inhabitants in the 1960s to make way for a US military base on Diego Garcia, the largest island.
Harold Wilson’s Labour government separated the islands from then British colony Mauritius in 1965 in breach of a UN resolution banning the breakup of colonies before independence. London then formed a new colonial entity, the British Indian Ocean Territory, which is now an Overseas Territory.
In 2015, a UN Tribunal ruled that the UK’s proposed “marine protected area” around the islands — shown by Wikileaks publications to be a ruse to keep the islanders from returning — was unlawful since it undermined the rights of Mauritius.
Then in February 2019, the International Court of Justice (ICJ) ruled in an advisory opinion that Britain must end its administration of the Chagos islands “as rapidly as possible”. The UN General Assembly adopted a resolution in May 2019 welcoming the ICJ ruling and “demanding that the United Kingdom unconditionally withdraw its colonial administration from the area within six months”. The UK government has rejected the calls.
Defying the UN over the Falklands
The UN’s 24-country Special Committee on Decolonisation — its principal body addressing issues concerning decolonisation — has repeatedly called on the UK government to negotiate a resolution to the dispute over the status of the Falklands. In its latest call, in June 2019, the committee approved a draft resolution “reiterating that the only way to end the special and particular colonial situation of the Falkland Islands (Malvinas) is through a peaceful and negotiated settlement of the sovereignty dispute between Argentina and the United Kingdom”.
The British government consistently rejects these demands. Last year, it stated:
“The Decolonisation Committee no longer has a relevant role to play with respect to British Overseas Territories. They all have a large measure of self government, have chosen to retain their links with the UK, and therefore should have been delisted a long time ago.”
In 2016, the UN Commission on the Limits of the Continental Shelf issued a report finding that the Falkland Islands are located in Argentina’s territorial waters.
Israel and settlement goods
Although Britain regularly condemns Israeli settlements in the occupied territories as illegal, in line with international law, it permits trade in goods produced on those settlements. It also does not keep a record of imports that come from the settlements — which include wine, olive oil and dates — into the UK.
UN Security Council resolutions require all states to “distinguish, in their relevant dealings, between the territory of the State of Israel and the territories occupied since 1967”. The UK is failing to do this.
Israel’s blockade of Gaza
Israel’s blockade of Gaza, imposed in 2007 following the territory’s takeover by Hamas, is widely regarded as illegal. Senior UN officials, a UN independent panel of experts, and Amnesty International all agree that the infliction of “collective punishment” on the population of Gaza contravenes international human rights and humanitarian law.
Gaza has about 1.8 million inhabitants who remain “locked in” and denied free access to the remainder of putative Palestine (the West Bank) and the outside world. It has poverty and unemployment rates that reached nearly 75% in 2019.
Through its naval blockade, the Israeli navy restricts Palestinians’ fishing rights, fires on local fishermen and has intercepted ships delivering humanitarian aid. Britain, and all states, have an obligation “to ensure compliance by Israel with international humanitarian law” in Gaza.
However, instead of doing so, the UK regularly collaborates with the navy enforcing the blockade. In August 2019, Britain’s Royal Navy took part in the largest international naval exercise ever held by Israel, off the country’s Mediterranean shore. In November 2016 and December 2017, British warships conducted military exercises with their Israeli allies.
Exports of surveillance equipment
Declassified revealed that the UK recently exported telecommunications interception equipment or software to 13 countries, including authoritarian regimes in the United Arab Emirates (UAE), Saudi Arabia and Oman. Such technology can enable security forces to monitor the private activities of groups or individuals and crack down on political opponents.
The UAE has been involved in programmes monitoring domestic activists using spyware. In 2017 and 2018, British exporters were given four licences to export telecommunications interception equipment, components or software to the UAE.
UK arms export guidelines state that the government will “not grant a licence if there is a clear risk that the items might be used for internal repression”. Reports by Amnesty International document human rights abuses in the cases of UAE, Saudi Arabia and Oman, suggesting that British approval of such exports to these countries is prima facie unlawful.
Arms exports to Saudi Arabia
Saudi Arabia has been accused by the UN and others of violating international humanitarian law and committing war crimes in its war in Yemen, which began in March 2015. The UK has licensed nearly £5-billion worth of arms to the Saudi regime during this time. In addition, the RAF is helping to maintain Saudi warplanes at key operating bases and stores and issues bombs for use in Yemen.
Following legal action brought by the Campaign Against the Arms Trade, the UK Court of Appeal ruled in June 2019 that ministers had illegally signed off on arms exports without properly assessing the risk to civilians. The court ruled that the government must reconsider the export licences in accordance with the correct legal approach.
The ruling followed a report by a cross-party House of Lords committee, published earlier in 2019, which concluded that Britain is breaking international law by selling weapons to Saudi Arabia and should suspend some export licences immediately.
Julian Assange’s arbitrary detention and torture
In the case of WikiLeaks publisher Julian Assange — currently held in Belmarsh maximum-security prison in London — the UK is defying repeated opinions of the UN Working Group on Arbitrary Detention (WGAD) and the UN special rapporteur on torture.
The latter, Nils Melzer, has called on the UK government to release Assange on the grounds that officials are contributing to his psychological torture and ill treatment. Melzer has also called for UK officials to be investigated for possible “criminal conduct” as government policy “severely undermines the credibility of [its] commitment to the prohibition of torture… as well as to the rule of law more generally”.
The WGAD — the supreme international body scrutinising this issue — has repeatedly demanded that the UK government end Assange’s “arbitrary detention”. Although the UN states that WGAD determinations are legally binding, its calls have been consistently rejected by the UK government.
Covert wars
Covert military operations to subvert foreign governments, such as Britain’s years-long operation in Syria to overthrow the Assad regime, are unlawful. As a House of Commons briefing notes, “forcible assistance to opposition forces is illegal”.
A precedent was set in the Nicaragua case in the 1980s, when US-backed covert forces (the “Contras”) sought to overthrow the Sandinista government. The International Court of Justice held that a third state may not forcibly help the opposition to overthrow a government since it breached the principles of non-intervention and prohibition on the use of force.
As Declassified has shown, the UK is currently engaged in seven covert wars, including in Syria, with minimal parliamentary oversight. Government policy is “not to comment” on the activities of its special forces “because of the security implications”. The public’s ability to scrutinise policy is also restricted since the UK’s Freedom of Information Act applies an “absolute exemption” to special forces. This is not the case for allied powers such as the US and Canada.
Torture and the refusal to hold an inquiry
In 2018 a report by parliament’s Intelligence and Security Committee found that the UK had been complicit in cases of torture and other ill treatment of detainees in the so-called “war on terror”. The inquiry examined the participation of MI6 (the secret intelligence service), MI5 (the domestic security service) and Ministry of Defence (MOD) personnel in interrogating detainees held primarily by the US in Afghanistan, Iraq and Guantanamo Bay during 2001-10.
The report found that there were 232 cases where UK personnel supplied questions or intelligence to foreign intelligence agents after they knew or suspected that a detainee was being mistreated. It also found 198 cases where UK personnel received intelligence from foreign agents obtained from detainees whom they knew or suspected to have been mistreated.
In one case, MI6 “sought and obtained authorisation from the foreign secretary” (then Jack Straw, in Tony Blair’s government) for the costs of funding a plane which was involved in rendering a suspect.
After the report was published, the government announced it was refusing to hold a judge-led, independent inquiry into the UK’s role in rendition and torture as it had previously promised to do. In 2019, human rights group Reprieve, together with Conservative and Labour MPs, instigated a legal challenge to the government over this refusal–which the High Court has agreed to hear.
The UN special rapporteur on torture, Nils Melzer, has formally warned the UK that its refusal to launch a judicial inquiry into torture and rendition breaches international law, specifically the UN Convention Against Torture. He has written a private “intervention” letter to the UK foreign secretary stating that the government has “a legal obligation to investigate and to prosecute”.
Melzer accuses the government of engaging in a “conscious policy” of co-operating with torture since 9/11, saying it is “impossible” the practice was not approved or at least tolerated by top officials.
UK’s secret torture policy
The MOD was revealed in 2019 to be operating a secret policy allowing ministers to approve actions which could lead to the torture of detainees. The policy, contained in an internal MOD document dated November 2018, allows ministers to approve passing information to allies even if there is a risk of torture, if “the potential benefits justify accepting the risk and legal consequences”.
This policy also provides for ministers to approve lists of individuals about whom information may be shared despite a serious risk they could face mistreatment. One leading lawyer has said that domestic and international legislation on the prohibition of torture is clear and that the MOD policy supports breaking of the law by ministers.
Amnesty for crimes committed by soldiers
There is a long history of British soldiers committing crimes during wars. In 2019 the government outlined plans to grant immunity for offences by soldiers in Iraq, Afghanistan and Northern Ireland that were committed more than 10 years before.
These plans have been condemned by the UN Committee Against Torture, which has called on the government to “refrain from enacting legislation that would grant amnesty or pardon where torture is concerned. It should also ensure that all victims of such torture and ill-treatment obtain redress”.
The committee has specifically urged the UK to “establish responsibility and ensure accountability for any torture and ill-treatment committed by UK personnel in Iraq from 2003 to 2009, specifically by establishing a single, independent, public inquiry to investigate allegations of such conduct.”
The government’s proposals are also likely to breach UK obligations under the European Convention on Human Rights, which obliges states to investigate breaches of the right to life or the prohibition on torture.
GCHQ’s mass surveillance
Files revealed by US whistleblower Edward Snowden in 2013 show that the UK intelligence agency GCHQ had been secretly intercepting, processing and storing data concerning millions of people’s private communications, including people of no intelligence interest — in a programme named Tempora. Snowden also revealed that the British government was accessing personal communications and data collected by the US National Security Agency and other countries’ intelligence agencies.
All of this was taking place without public consent or awareness, with no basis in law and with no proper safeguards. Since these revelations, there has been a long-running legal battle over the UK’s unlawful use of these previously secret surveillance powers.
In September 2018, the European Court of Human Rights ruled that UK laws enabling mass surveillance were unlawful, violating rights to privacy and freedom of expression. The court observed that the UK’s regime for authorising bulk interception was incapable of keeping “interference” to what is “necessary in a democratic society”.
The UK’s Investigatory Powers Tribunal, the body which considers complaints against the security services, also found that UK intelligence agencies had unlawfully spied on the communications of Amnesty International and the Legal Resources Centre in South Africa.
In 2014, revelations also confirmed that GCHQ had been granted authority to secretly eavesdrop on legally privileged lawyer-client communications, and that MI5 and MI6 adopted similar policies. The guidelines appeared to permit surveillance of journalists and others deemed to work in “sensitive professions” handling confidential information.
MI5 personal data
In 2019, MI5 was found to have for years unlawfully retained innocent British people’s online location data, calls, messages and web browsing history without proper protections, according to the Investigatory Powers Commissioner’s Office which upholds British privacy protections. MI5 had also failed to give senior judges accurate information about repeated breaches of its duty to delete bulk surveillance data, and was criticised for mishandling sensitive legally privileged material.
The commissioner concluded that the way MI5 was holding and handling people’s data was “undoubtedly unlawful”. Warrants for MI5’s bulk surveillance were issued by senior judges on the understanding that the agency’s legal data handling obligations were being met — when they were not.
“MI5 have been holding on to people’s data—ordinary people’s data, your data, my data — illegally for many years,” said Megan Goulding, a lawyer for rights organisation Liberty, which brought the case. “Not only that, they’ve been trying to keep their really serious errors secret — secret from the security services watchdog, who’s supposed to know about them, secret from the Home Office, secret from the prime minister and secret from the public.”
Intelligence agencies committing criminal offences
MI5 has been operating under a secret policy that allows its agents to commit serious crimes during counter-terrorism operations in the UK, according to lawyers for human rights organisations brin
ging a case to the Investigatory Powers Tribunal.
The policy, referred to as the “third direction”, allows MI5 officers to permit the people they have recruited as agents to commit crimes in order to secure access to information that could be used to prevent other offences being committed. The crimes potentially include murder, kidnap and torture and have operated for decades. MI5 officers are, meanwhile, immune from prosecution.
A lawyer for the human rights organisations argues that the issues raised by the case are “not hypothetical”, submitting that “in the past, authorisation of agent participation in criminality appears to have led to grave breaches of fundamental rights”. He points to the 1989 murder of Belfast solicitor Pat Finucane, an attack carried out by loyalist paramilitaries, including some agents working for the British state.
The ‘James Bond clause’
British intelligence officers can be authorised to commit crimes outside the UK. Section 7 of the 1994 Intelligence Services Act vacates UK criminal and civil law as long as a senior government minister has signed a written authorisation that committing a criminal act overseas is permissible. This is sometimes known as the “James Bond clause”.
British spies were reportedly given authority to break the law overseas on 13 occasions in 2014 under this clause. GCHQ was given five authorisations “removing liability for activities including those associated with certain types of intelligence gathering and interference with computers, mobile phones and other types of electronic equipment”. MI6, meanwhile, was given eight such authorisations in 2014.
Underage soldiers
Britain is the only country in Europe and Nato to allow direct enlistment into the army at the age of 16. One in four UK army recruits is now under the age of 18. According to the editors of the British Medical Journal, “there is no justification for this state policy, which is harmful to teen health and should be stopped”. Child recruits are more likely than adult recruits to end up in frontline combat, they add.
It was revealed in 2019 that the UK continued to send child soldiers to fight in Iraq and Afghanistan despite pledging to end the practice. The UK says it does not send under-18s to warzones, as required by the UN Optional Protocol on the Involvement of Children in Armed Conflict, known as the “child soldiers treaty”.
The UK, however, deployed five 17-year-olds to Iraq or Afghanistan between 2007 and 2010: it claims to have done so mistakenly. Previous to this, a minister admitted that teenagers had also erroneously been sent into battle between 2003 and 2005, insisting it would not happen again.
The UN Committee on the Rights of the Child expressed concern at the UK’s recruitment policy in 2008 and 2016, and recommended that the government “raise the minimum age for recruitment into the armed forces to 18 years in order to promote the protection of children through an overall higher legal standard”. Parliament’s Joint Committee on Human Rights, the children’s commissioners for the four jurisdictions of the UK, along with children’s rights organisations, all support this call. DM
Mark Curtis is editor of Declassified UK and tweets at @markcurtis30
February 9, 2020
Posted by aletho |
Civil Liberties, Ethnic Cleansing, Racism, Zionism, Subjugation - Torture, Timeless or most popular, War Crimes | GCHQ, Israel, MI6, Middle East, Pakistan, Palestine, RAF, Somalia, UK, Yemen |
Leave a comment

Graphic by Claudio Cabrera for MintPress News
Election Day 2020: 32 Americans dead, over 200 injured, martial law declared and the election itself is canceled. While this horrific scenario seems more like the plot of a Hollywood film, such was the end result of a recent simulation examining the preparedness of U.S. officials from the Federal Bureau of Investigation (FBI), the Department of Homeland Security (DHS) and the U.S. Secret Service against “bad actors” seeking to undermine the upcoming presidential election.
Yet, this simulation was not a government-organized exercise but was instead orchestrated by a private company with deep ties to foreign and domestic intelligence services, a company that is also funded by investors with clear connections to individuals who would stand to benefit if such a catastrophic election outcome were to become reality.
Much of the rhetoric since the last presidential election in 2016 has focused on the issue of foreign meddling by U.S. rival states like Russia, while China has emerged as the new “meddler” of choice in American corporate media as the 2020 election approaches. Though time has revealed that many of the post-2016 election meddling claims were not as significant as initially claimed, the constant media discussion of foreign threats to U.S. democracy and electoral processes – whether real or imagined – has undeniably created a climate of fear.
Those fears have since been preyed upon by neoconservative groups and the U.S. military-industrial complex, both of which are hardly known for their love of democratic processes, to offer a series of ready-made solutions to these threats that actually undermine key pillars of American democracy, including independent reporting and voting machine software.
However, many of the very same media outlets and groups that frequently fretted about Russia, China or another rival state meddling in U.S. democracy have largely ignored the role of other nation states, such as Israel, in efforts to sway the last U.S. election in 2016 and meddle in numerous elections in Africa, Latin America and Asia in the years since.
As a consequence of this climate of fear, it should be hardly surprising that the corporate media lauded the recent 2020 election simulation that ended in an abysmal failure for U.S. officials, the cancellation of the U.S. election and the imposition of martial law. Yet, none of those reports on the exercise noted that the company that hosted the simulation, called Cybereason, is led by ex-members of Israel’s military intelligence unit 8200, advised by former top and current officials in both Israeli military intelligence and the CIA. In addition, it is funded by and partnered with top U.S. weapons manufacturer and government contractor Lockheed Martin and financial institutions with clear and direct ties to Saudi Crown Prince Mohammed bin Salman and White House adviser and the president’s son-in-law Jared Kushner. Also left unmentioned in media reports on Cybereason’s election simulations is the fact that Cybereason’s CEO, Lior Div, has openly admitted that he views his work at Cybereason as a “continuation” of his service to Israel’s intelligence apparatus.
With Cybereason planning to host more simulations in cooperation with federal agencies as the U.S. election inches closer, a deeper exploration of this company, its ties to intelligence and military contractors in the U.S. and Israel and its financial ties to key Trump allies both domestically and abroad warrants further investigation.
In this two part series, MintPress will not only explore these aspects but also how many of the technologies wielded by the “bad actors” in the Cybereason election simulation have been pioneered and perfected, not by U.S. rival states, but by Israeli companies and start-ups with clear ties to that country’s intelligence apparatus.
Also notable is the fact that Cybereason itself has covertly become a major software provider to the U.S. government and military through its direct partnership with Lockheed Martin, which followed the defense company’s decision to open an office at the Israeli military’s new cyber operations hub in the Negev desert. In examining all of these interlocking pieces, a picture emerges of a potentially sinister motive for Cybereason’s simulations aimed at gauging how U.S. federal officials respond to crisis situations on Election Day.
Understanding “Operation Blackout”
In early November, a team of “hackers” working for the private U.S.-based, Israeli-founded company Cybereason conducted a 2020 election simulation with members of various U.S. agencies, namely the DHS, FBI and the U.S. Secret Service. The simulation was organized by Cybereason and the law firm Venable and the U.S. agencies in attendance were invited and appear to not have been charged to participate.
The simulation, titled “Operation Blackout,” was set in a fictional swing state called “Adversaria” and pitted “ethical hackers” from Cybereason against a team of federal and local law enforcement officials. The opposing teams were supervised by a “white team” composed of members of Cybereason’s staff and Ari Schwartz — a former member of the White House’s National Security Council and the National Institute of Standards and Technology (NIST) — who set the rules of the simulation and would ultimately decide its outcome. Schwartz also used to work for the Center for Democracy and Technology (CDT), a major backer of Microsoft’s ElectionGuard software.
Operation Blackout did not involve hackers targeting election software or voting machines, instead, it focused on civilian infrastructure and psychological operations against the American citizens in the fictitious “Adversaria” on election day. The hacker team was led by Cybereason co-founder Yonathan Striem-Amit, a former contractor for Israeli government agencies and a former operative for the elite Israeli military intelligence Unit 8200, best known for its cyber offensives against other governments.
“In a country as fragmented as the US, the number of people needed to influence an election is surprisingly small,” Striem-Amit told Quartz of the exercise. “We attempted to create havoc and show law enforcement that protecting the electoral process is much more than the machine.”
Streim-Amit’s team completely devastated the U.S. law enforcement team in Operation Blackout by not only causing chaos but murdering numerous civilians. Hackers took control of city buses, ramming them into civilians waiting in line at polling stations, killing 32 and injuring over 200. They also took control of city traffic lights in order to cause traffic accidents, used so-called “deepfakes” to conduct psychological operations on the populace and created fake bomb threats posing as the terror group ISIS, which incidentally has its own ties to Israeli intelligence. Telecom networks and news outlets within the fictitious states were also hacked and flooded with deepfakes aimed at spreading disinformation and panic among U.S. citizens.

A map of targets in Adverseria is shown during Operation Blackout in Boston’s John Hancock Tower. Mark Albert | Twitter
The supervising team, composed of Cybereason employees and former NSC member Ari Schwartz, decided that the outcome of the face-off between the hacker and law enforcement teams was the outright cancellation of the 2020 election, the declaration of martial law by authorities, the growth of public fear regarding terrorism and allegations of U.S. government collusion with a foreign actor. Cybereason has stated that they will soon conduct another 2020 election simulation with federal authorities as the election draws closer.
Given how the simulation played out, it is quite clear that it is a far cry from the actual scope of alleged foreign meddling during the 2016 election, meddling which was allegedly the motivation behind Operation Blackout. Indeed, the extent of Russian interference in the 2016 election amounted to $100,000 worth of Facebook ads over three years, 25 percent of which were never seen by the public, and claims that Russian state actors were responsible for leaking emails from the then-Democratic presidential nominee Hillary Clinton and the Democratic National Committee (DNC). In contrast, Operation Blackout went well beyond any observed or even imagined “foreign meddling” related to the 2016 election and appears more like a terror attack targeting elections than a covert means of manipulating their outcomes.
Several mainstream publications have covered Operation Blackout but have failed to note that the company behind them has deep ties to foreign intelligence outfits and governments with a documented history of manipulating elections around the world, including the 2016 U.S. election.
Quartz framed the exercise as important for “preparing for any and all possibilities in 2020,” which “has become an urgent task for US regulators and law enforcement.” Similarly, CyberScoop treated the simulation as a “sophisticated exercise to help secure the vote.” Other articles took the same stance.
A series of simulations
In the weeks after the Washington area election simulation, Cybereason repeated the same exercise in London, this time with members of the U.K. Intelligence agency GCHQ, the U.K. Foreign Office and the Metropolitan Police. The law enforcement team in the exercise, which included the U.K. officials, was headed by a Cybereason employee — Alessandro Telami, who formerly worked for the NATO Communications and Information Agency (NCI). Like the prior simulation conducted in the U.S., Cybereason did not appear to charge U.K. government agencies for their participation in the exercise.
Cybereason has — with little fanfare — been promoting extreme election day scenarios since before the 2016 election. Cybereason’s first mention of these tactics appears in a September 2016 blog post written by the company’s CEO and former Israeli government contractor Lior Div — a former leader of offensive cyberattacks for the IDF’s elite Unit 8200 and a former development group leader at the controversial Israeli-American corporation Amdocs.
Div wrote that hackers may target U.S. elections by “breaking into the computers that operate traffic lighting systems and interfering with the ones around polling stations to create massive traffic jams, “hacking polling companies,” and “targeting live election coverage on cable or network television stations.” A follow-up post by Div from October 2016 added further meddling tactics such as “cut power to polling stations” and “mess with a voter’s mind.”
Two years later, Cybereason held its first election meddling simulation, touting many of these same tactics, in Boston. The simulation focused on local and state responses to such attacks and saw Boston-based Cybereason invite Massachusetts state and local officials as well as Boston police officers and a former police commissioner to participate. “Twitter accounts spreading fake news,” “turning off a city’s closed-circuit cameras,” “hacking self-driving cars and navigation apps,” and “targeting a city’s 911 call center with a DDoS attack” were all used in the simulation, which saw Cybereason’s “ethical hackers” attempt to disrupt election day. Media coverage of the simulation at the time framed it as a necessary preparation for countering “Russian” threats to U.S. democracy. Like the more recent simulations, the mock election was canceled and voter confidence in the electoral process was devastated.
This past July, Cybereason conducted a similar simulation with officials from the FBI, DHS and the Secret Service for the first time. That simulation, which also took place in Boston, was remarkably similar to that which occurred in November. One intelligence officer from DHS who participated in the July exercise called the simulation “very realistic.” Another claimed that the simulation was a way of applying “lessons learned from 9/11” by preventing the government’s “failure of imagination” that officials have long alleged was the reason for the government’s inability to thwart the September 11 attacks. Notably, The U.S. military simulated a scenario in which terrorists flew airplanes into the Pentagon less than a year before the September 11 attacks.

In this undated photo from Cybereason’s website, a faux ballot box is shown in the company’s Boston office.
Participating government officials, Cybereason staff and the media have consistently touted the importance of these simulations in securing elections against extreme threats, threats which — to date — have never materialized due to the efforts of foreign or domestic actors on election day. After all, these exercises are only simulations of possibilities and, even if those possibilities seem implausible or unlikely, it is important to be prepared for any eventuality.
But what if the very figures behind these simulations and the investors that fund them had a history of election meddling themselves? Cybereason’s deep ties to Israeli intelligence, which has a documented history of aggressive espionage and election meddling in the United States and in several nations worldwide, warrant a deeper look into the firms’ possible motives and the myriad conflicts of interest that arise in giving it such unprecedented access to the heart of America’s democracy.
What Does Cybereason Do?
Cybereason’s interest in terror events during elections seems out of place given that the company itself is focused on selling technological cybersecurity solutions like antivirus and ransomware protection software, software products that would be minimally effective against the type of threat encountered in the company’s election day simulations.
Cybereason is often described as offering a comprehensive technological defense platform to companies and governments that combines a next-generation antivirus with endpoint detection and response (EDR), which enables the company to respond to typical viruses and malware as well as sophisticated, complex attacks. The platform makes heavy use of artificial intelligence (AI) and cloud computing and specifically uses Amazon Web Services (AWS), which is used by a litany of private companies as well as U.S. intelligence agencies.
While many cybersecurity platforms combine antivirus and antimalware with EDR and AI, Cybereason claims that their military background is what sets them apart. They have marketed themselves as offering “a combination of military-acquired skills and cloud-powered machine learning to endpoint detection and response” and actively cite the fact that most of their employees are former members of Unit 8200 as proof that they are “applying the military’s perspective on cybersecurity to enterprise security.”
In 2018, Cybereason’s former senior director for intelligence, Ross Rustici, described the platform to CBR as follows:
Our founders are ex-Israeli intelligence who worked on the offensive side. They basically wanted to build a tool that would catch themselves. We follow the kill chain model started by Lockheed Martin [now a major investor in Cybereason] and try to interrupt every stage once an intruder’s inside a target network.”
Lior Div, Cybereason’s CEO described the difference between his company’s platform and that of past market leaders in this way to Forbes :
The old guard of antivirus companies like Symantec and McAfee would install something to block endpoints and you needed to do a lot [of monitoring] to make sure you weren’t under attack. We came with a different approach to see the whole enterprise and leverage AI to be able to fully autonomously identify where attackers are and what they’re doing.”
Thus, in looking at Cybereason’s product and its marketing objectively, it seems that the only innovative component of the company’s system is the large number of ex-military intelligence officers it employs and its tweaking of a previously developed and automated model for threat engagement, elimination and prevention.
Instead, Cybereason’s success seems to owe to its prominent connections to the private and public sectors, especially in Israel, and its investors who have funneled millions into the company’s operations, allowing them to expand rapidly and quickly claim a dominant position in emerging technology markets, such as the Internet of Things (IoT) and advanced healthcare systems.

A screenshot from a live stream of a 2019 Cybereason cyber-attack simulation
Their considerable funding from the likes of Lockheed Martin and Softbank, among others, has also helped them to expand their international presence from the U.S., Europe and Israel into Asia and Latin America, among other places. Notably, while Cybereason is open about their investors and how much funding they receive from each, they are extremely secretive about their financial performance as a company and decline to disclose their annual revenue, among other indicators. The significance of Cybereason’s main investors in the context of the company’s election simulations and its ties to Israeli and U.S. intelligence (the focus of this article) will be discussed in Part 2.
Cybereason also includes a security research arm called Nocturnus, currently headed by a former Unit 8200 officer. Nocturnus will be explored further in Part 2 of this series, as it essentially functions as a private intelligence company in the tech sector and has been behind several recent claims that have attributed alleged hacks to state actors, namely China and North Korea. For now, it is important to keep in mind that Nocturnus utilizes Cybereason’s “global network of millions of endpoints” for its intelligence gathering and research, meaning the endpoints of every device to which Cybereason’s software has access.
Given what Cybereason provides as a company, their interest in offering election simulations to government officials free of charge seems odd. Indeed, in the simulations hosted by Cybereason for U.S. officials, there is little opportunity for the company to market their software products given that the simulation did not involve electronic voting infrastructure at all and, instead, the malevolent actors used deep fakes, disinformation and terror attacks to accomplish their goals. Why then would this company be so interested in gauging the response of U.S. law enforcement to such crises on election day if there is no sales pitch to be made? While some may argue that these simulations are an altruistic effort by the company, an investigation into the company’s founders and the company’s ties to intelligence agencies suggests that this is unlikely to be the case.
The People Behind Cybereason
Cybereason was created in 2012 by three Israelis, all of whom served together as officers in the Israel Defense Force’s elite technological and signals intelligence unit, which is most often referred to as Unit 8200. Unit 8200 has been the subject of several MintPress investigative reports over the past year focusing on its ties to the tech industry.
Unit 8200 is an elite unit of the Israeli Intelligence corps that is part of the IDF’s Directorate of Military Intelligence and is involved mainly in signal intelligence, surveillance, cyberwarfare and code decryption. It is also well-known for its surveillance of Palestinian civilians and for using intercepted communications as blackmail in order to procure informants among Palestinians living under occupation in the West Bank.
The unit is frequently described as the Israeli equivalent of the NSA and Peter Roberts, a senior research fellow at Britain’s Royal United Services Institute, characterized the unit in an interview with the Financial Times as “probably the foremost technical intelligence agency in the world and stand[ing] on a par with the NSA in everything except scale.” Notably, the NSA and Unit 8200 have collaborated on numerous projects, most infamously on the Stuxnet virus as well as the Duqu malware.
Given the secrecy of the work conducted by Unit 8200, it is hard to know exactly what Cybereason’s co-founders did while serving in the controversial unit, however, a brief biography of the company’s current CEO and co-founder Lior Div states that “Div served as a commander [in Unit 8200] and carried out some of the world’s largest cyber offensive campaigns against nations and cybercrime groups. For his achievements, he received the Medal of Honor, the highest honor bestowed upon Unit 8200 members (emphasis added).”

Lior Div speaks during the Cyber Week conference in Tel Aviv, Israel, June 25, 2019. Corinna Kern | Reuters
After having served in leadership positions within Unit 8200, all three Cybereason co-founders went on to work for private Israel-based tech or telecom companies with a history of aggressive espionage against the U.S. government.
Cybereason co-founders Yonathan Striem Amit (Cybereason’s Chief Technology Officer) and Yossi Naar (Cybereason Chief Visionary Officer) both worked for Gita Technologies shortly before founding Cybereason with fellow Unit 8200 alumnus Lior Div. Gita, according to public records, is a subsidiary of Verint Systems, formerly known as Comverse Infosys.
Verint/Comverse was initially funded by the Israeli government and was founded by Jacob “Kobi” Alexander, a former Israeli intelligence officer who was wanted by the FBI on nearly three dozen charges of fraud, theft, lying, bribery, money laundering and other crimes for over a decade until he was finally extradited to the United States and pled guilty to some of those charges in 2016.
Despite its history of corruption and foreign intelligence connections, Verint/Comverse was hired by the National Security Agency (NSA) to create backdoors into all the major U.S. telecommunications systems and major tech companies, including Facebook, Microsoft and Google. An article on Verint’s access to U.S. tech infrastructure in Wired noted the following about Verint:
In a rare and candid admission to Forbes, Retired Brig. Gen. Hanan Gefen, a former commander of the highly secret Unit 8200, Israel’s NSA, noted his former organization’s influence on Comverse, which owns Verint, as well as other Israeli companies that dominate the U.S. eavesdropping and surveillance market. ‘Take NICE, Comverse and Check Point for example, three of the largest high-tech companies, which were all directly influenced by 8200 technology,’ said Gefen.”
Federal agents have reported systemic breaches at the Department of Justice, FBI, DEA, the State Department, and the White House going all the way back to the 1990s, breaches they claimed could all be traced back to two companies: Comverse/Verint and Amdocs. Cybereason’s other co-founder and current CEO, Lior Div, used to work for Amdocs as the company’s development group leader.
After leaving Amdocs, Div founded a company called Alfatech. Alfatech publicly claims to specialize in “professional Head Hunting and Quality Recruiting services,” yet it has no functional website. Despite its publicly stated mission statement, Israeli media reports that mention Alfatech describe it as “a cybersecurity services company for Israeli government agencies.” No reason for the obvious disconnect between the company’s own claims and those made by the media has been given.
Div left Alfatech in 2012 to found Cybereason alongside Striem-Amit and Naar. According to an interview that Div gave to TechCrunch earlier this year, he stated that his work at Cybereason is “the continuation of the six years of training and service he spent working with the Israeli army’s 8200 Unit (emphasis added).” Div was a high-level commander in Unit 8200 and “carried out some of the world’s largest cyber offensive campaigns against nations and cybercrime groups” during his time there. TechCrunch noted that “After his time in the military, Div worked for the Israeli government as a private contractor reverse-engineering hacking operations,” an apparent reference to his work at Alfatech.
Even deeper ties to intelligence
Not only do Cybereason’s own co-founders have considerable links to the Israeli government, Israeli intelligence and intelligence-connected private companies, but it also appears that the work of Cybereason itself is directly involved with Israeli intelligence.
The company periodically publishes reports by a secretive faction of the company called the Cybereason Intelligence Group or CIG. The only description of CIG’s composition available on Cybereason’s website is as follows:
The Cybereason Intelligence Group was formed with the unique mission of providing context to the most sophisticated threat actors. The group’s members include experts in cyber security and international security from various government agencies, including the Israel Defense Forces’ Unit 8200, which is dedicated to conducting offensive cyber operations. Their primary purpose is to examine and explain the Who and the Why behind cyber attacks, so that companies and individuals can better protect themselves (emphasis added).”
It is unclear how many members comprise CIG and if its members are employees of only Israeli government agencies, or if it includes officials from the U.S. government/Intelligence or other governments. However, what is clear is that it is composed entirely of government officials, which include active members of Unit 8200, and that the purpose of the group is to issue reports that place blame for cyberattacks on state and non-state actors. Perhaps unsurprisingly, the vast majority of CIG’s reports published by Cybereason focus exclusively on Russia and China. When discussing nation-state cyber threats in general, Cybereason’s website only mentions China, North Korea, Iran and Russia by name, all of which are incidentally rival states of the U.S. government. Notably, Israel’s government — listed as a “leading espionage threat” to U.S. financial institutions and federal agencies by the U.S.’ NSA — is absent from Cybereason’s discussions of state actors.
In addition to CIG, Cybereason’s cybersecurity research arm, Nocturnus, includes several Unit 8200 alumni and former Israeli military intelligence and government contractors and has assigned blame to state actors for several recent hacks. It also has claimed to have discovered more such hacks but has declined to publicly disclose them due to the “sensitive” nature of the hacks and companies affected.
Other hints at Cybereason’s connections to state intelligence can be seen in its advisory board. Robert Bigman, the former Chief Information Security Officer (CISO) for the Central Intelligence Agency (CIA) who oversaw the spy agency’s “commercial partner engagement” program (i.e. alliances with the private tech sector), is a key figure on the company’s advisory board. According to his biography, Bigman “ contributed to almost every Intelligence Community information security policy/technical standard and has provided numerous briefings to the National Security Council, Congress and presidential commissions. In recognition of his expertise and contributions, Bigman has received numerous CIA and Director of National Intelligence Awards.”

Cybereason’s leadership team features a who’s who of Israeli and US intel officials
Unmentioned in his biography published on his own website, or on Cybereason’s website, is that Bigman is also an advisor to another Israeli tech company, Sepio Systems. The chairman of Sepio, Tamir Pardo, is a self-described “leader” in the cybersecurity industry and former director of Israel’s Mossad. Sepio is funded by a venture capital firm founded by the creators of the controversial Israeli spy tech company NSO Group, which has received a slew of negative press coverage after its software was sold to several governments who used it to spy on dissidents and human rights activists.
In addition to Bigman, Cybereason’s advisory board includes Pinchas Buchris, the former head of Unit 8200 and former managing director of the IDF. Not unlike Bigman, Buchris’ bio fails to mention that he sits on the board of directors of Carbyne911, alongside former Israeli Prime Minister Ehud Barak and Nicole Junkerman, both well-known associates of intelligence-linked sex trafficker Jeffery Epstein. Epstein himself poured at least $1 million into Carbyne, an Israeli company that seeks to run all 911 call centers in the U.S. at the national level and has close ties to the Trump administration. More information on Carbyne and its ties to Israeli and U.S. intelligence as well as its connection to coming pre-crime policies to be enacted in 2020 by the U.S. Department of Justice can be found in this MintPress report from earlier this year. Given that Cybereason’s election day simulations involve the simulated collapse of 911 call center functionality, Buchris’ ties to both Cybereason and Carbyne911 are notable.
Another notable Cybereason advisor is the former commissioner of the Boston Police Department, Edward Davis. Davis heavily promoted Cybereason’s disturbing election day simulations and even participated directly in one of them. He was also police commissioner of the Boston PD at the time of the Boston Marathon bombing and oversaw the near-martial law conditions imposed on the city during the manhunt for the alleged perpetrators of that bombing (who themselves had a rather odd relationship with the FBI). This is notable given that Cybereason’s election day simulations ended with martial law being imposed on the fictional city used in the exercise
Cybereason also has several advisors who hold top positions at powerful U.S. companies that are also — incidentally — U.S. government contractors. These include the Vice President Security and Privacy Engineering at Google, Deputy Chief Information Security Officer (CISO) of Lockheed Martin and CISO at Motorola. Both Motorola and Lockheed Martin use Cybereason’s software and the latter is also a major investor in the company. Furthermore, as will be explained in Part 2 of this article, Lockheed Martin has used its privileged position as the top private contractor to the U.S. government to promote the widespread use of Cybereason’s software among U.S. government agencies, including the Pentagon.
Much more than a cybersecurity company
Given Cybereason’s deep and enduring ties to Israeli intelligence and its growing connections to the U.S. military and U.S. intelligence through its hiring of top CIA officials and partnership with Lockheed Martin, it’s worth asking if these disturbing election simulations could serve an ulterior purpose and, if so, who would benefit. While some aspects regarding clear conflicts of interest in relation to the 2020 election and Cybereason will be discussed in Part 2, this article will conclude by examining the possibility that Cybereason is acting as a front company for Israeli intelligence based on that country’s history of targeting the U.S. through private tech companies and on Cybereason’s own questionable characteristics.
First, Cybereason as a company presents several oddities. Its co-founder and CEO openly states that he views Cybereason’s work as a continuation of his service for Israeli military intelligence. In addition, he and the company’s other founders — after they left Unit 8200 — went to work for Israeli tech companies that have been known to spy on U.S. federal agencies for the Israeli government.
In addition, as previously mentioned, Cybereason has sought out former intelligence officers from the CIA and Unit 8200 for its management team and board of advisors. The company itself also functions as a private intelligence firm through CIG and Nocturnus, both of which employ former and current intelligence officials, and have made significant claims regarding the attribution of specific cybercrimes to state actors. It appears highly likely that these claims are influenced by those same intelligence agencies that boast close ties to Cybereason. Furthermore, Nocturnus’ access to Cybereason’s “global” network of endpoints makes it a private intelligence gathering company as it gathers and analyzes data from all devices that run Cybereason’s software.
Yet, even more telling is the fact that Israel’s government has an open policy of outsourcing intelligence-related activity to the private sector, specifically the country’s tech sector. As MintPress previously reported, this trend was first publicly acknowledged by Israel in 2012, the same year that Cybereason was founded by former Israeli military intelligence officers then-working for private contractors for Israel’s government (Alfatech) or private companies known to have ties to Israeli intelligence, including Verint/Comverse.
As noted in an article on the phenomenon from the Israeli media outlet The Calcalist:
Israel is siphoning cyber-related activities from its national defense apparatus to privately held companies. Since 2012, cyber-related and intelligence projects that were previously carried out in-house in the Israeli military and Israel’s main intelligence arms are transferred to companies that in some cases were built for this exact purpose.”
Mention of Israel’s policy of blurring the lines between the public and private sector when it comes to cybersecurity and intelligence gathering has even garnered the occasional mention in mainstream media, such as in a 2018 Foreign Policy article:
Israel, for one, has chosen to combat the problem on a statewide level by linking the public and private spheres, sometimes literally. The country’s cyberhub in the southern city of Beersheba is home not just to the Israeli military’s new technology campus but also to a high-tech corporate park, Ben-Gurion University of the Negev’s cyber-research center, and the Israel National Cyber Directorate, which reports directly to the prime minister’s office. “There’s a bridge between them—physically,” [Gabriel] Avner, the security consultant, said by way of emphasis.”
Notably, a year before Lockheed Martin invested in and partnered with Cybereason, the U.S.-based weapons company opened an office at the IDF’s public-private cyber hub in Beersheba. At the inauguration ceremony for Lockheed’s Beersheba office, company CEO Marilyn Hewson stated:
The consolidation of IDF Technical Units to new bases in the Negev Desert region is an important transformation of Israel’s information technology capability… By locating our new office in the capital of the Negev we are well positioned to work closely with our Israeli partners and stand ready to: accelerate project execution, reduce program risk and share our technical expertise by training and developing in-country talent.”

Lockheed Martin CEO Marillyn Hewson, inaugurates the Lockheed Martin Israel Demonstration Center in Tel Aviv.
Further evidence of this public-private merger can be seen in how two of Israel’s intelligence agencies, Shin Bet and Mossad, have both recently launched a private start-up accelerator and a hi-tech venture capital fund, respectively. The Shin Bet’s accelerator, called Xcelerator, usually makes its investments in private companies public, while Mossad’s Libertad Ventures refuses to disclose the tech companies and start-ups in which it invests. Former directors of both Mossad and Shin Bet have described these intelligence agencies themselves of being like start-ups, clearly showing how much the line between intelligence apparatus and private company has been blurred within the context of Israel’s tech industry and specifically its cybersecurity industry.
The advantages of outsourcing cyber intelligence operations to private companies have been noted by several analysts, including Sasha Romanosky, a former Cyber Policy Advisor at the Department of Defense and current analyst at RAND Corporation. Romanosky noted in 2017 that private intelligence and cybersecurity firms “do not necessarily face the same constraints or potential repercussions” as their public counterparts when it comes to designating blame for a cyberattack, for example. In addition, outsourcing intelligence objectives or missions to private companies provides a government with plausible deniability if that private company’s espionage-related activities or ties are made public.
Furthermore, Israeli intelligence has a long history of using private tech companies for the purposes of espionage, including against the United States. While Amdocs and Verint/Comverse were already mentioned as having been used by the state of Israel in this way, other private companies have also been used to market software backdoored by Israeli intelligence to countries around the world, both within the U.S. and elsewhere. The most well-known example of this is arguably the mass sale and distribution of the bugged PROMIS software, which was discussed at length in several recent MintPress News reports.
Given Cybereason’s ties to intelligence and Israeli intelligence’s history of placing backdoors in its software, it is worth pointing out that Cybereason’s main product, its antivirus and network defense platform, offers a major espionage opportunity. Blake Darché, a former N.S.A. operator, told the New York Times in 2017 that antivirus programs, which Cybereason’s defense platform includes, is “the ultimate backdoor,” adding that it “provides consistent, reliable and remote access that can be used for any purpose, from launching a destructive attack to conducting espionage on thousands or even millions of users.” Whether a company like Cybereason would use its software for such ends is unknown, though the company does acknowledge that its cybersecurity arm does gather intelligence from all systems that use the company’s software and currently employs and works with active duty Unit 8200 officials through CIG. This is notable because Unit 8200’s main task for Israeli military intelligence is signals intelligence, i.e. surveillance.
More of a mystery, however, is why a company like Cybereason is so interested in U.S. election security, particularly when Israeli intelligence and Israeli intelligence-connected private companies have been caught in recent years meddling in elections around the world, including the United States.
Whitney Webb is a MintPress News journalist based in Chile. She has contributed to several independent media outlets including Global Research, EcoWatch, the Ron Paul Institute and 21st Century Wire, among others. She has made several radio and television appearances and is the 2019 winner of the Serena Shim Award for Uncompromised Integrity in Journalism.
January 4, 2020
Posted by aletho |
Civil Liberties, Deception, False Flag Terrorism | Amdocs, CIA, Comverse Infosys, Cybereason, GCHQ, Israel, Lockheed Martin, NSO Group, UK, Unit 8200, United States, Verint Systems |
Leave a comment
The release of Justice Department Inspector General Michael Horowitz’s report, which shows that the Democrats, media, and FBI lied about not interfering in an election, will be a historian’s marker for how a decent nation fooled itself into self-harm. Forget about foreigners influencing our elections; it was us.
The Horowitz Report is being played by the media for its conclusion: that the FBI’s intel op run against the Trump campaign was not politically motivated and thus “legal.” That covers one page of the 476-page document, but because it fits with the Democratic/mainstream media narrative that Trump is a liar, the rest has been ignored. “The rest,” of course, is a detailed description of America’s domestic intelligence apparatus, aided by its overseas intelligence apparatus, and assisted by its Five Eyes allies’ intelligence apparatuses. And the conclusion is that they unleashed a full-spectrum spying campaign against a presidential candidate in order to influence an election, and when that failed, they tried to delegitimize a president.
We learn from the Horowitz Report that it was an Australian diplomat, Alexander Downer, a man with ties to his own nation’s intel services and the Clinton Foundation, who set up a meeting with Trump staffer George Papadopoulos, creating the necessary first bit of info to set the plan in motion. We find the FBI exaggerating, falsifying, and committing wicked sins of omission to buffalo the Foreign Intelligence Surveillance Act (FISA) courts into approving electronic surveillance on Team Trump to overtly or inadvertently monitor the communications of Paul Manafort, Michael Cohen, Jared Kushner, Michael Flynn, Jeff Sessions, Steve Bannon, Rick Gates, Trump transition staffers, and likely Trump himself. Trump officials were also monitored by British GCHQ, the information shared with their NSA partners, a piece of all this still not fully public.
We learn that the FBI greedily consumed the Steele Dossier, opposition “research” bought by the Clinton campaign to smear Trump with allegations of sex parties and pee tapes. Most notoriously, the dossier claims he was a Russian plant, a Manchurian Candidate, owned by Kremlin intelligence through a combination of treats (land deals in Moscow) and threats (kompromat over Trump’s evil sexual appetites). The Horowitz Report makes clear the FBI knew the Dossier was bunk, hid that conclusion from the FISA court, and purposefully lied to the FISA court in claiming that the Dossier was backed up by investigative news reports, which themselves were secretly based on the Dossier. The FBI knew Steele had created a classic intel officer’s information loop, secretly becoming his own corroborating source, and gleefully looked the other way because it supported his goals.
Horowitz contradicts media claims that the Dossier was a small part of the case presented to the FISA court. He finds that it was “central and essential.” And it was garbage: “factual assertions relied upon in the first [FISA] application targeting Carter Page were inaccurate, incomplete, or unsupported by appropriate documentation, based upon information the FBI had in its possession at the time the application was filed.” One of Steele’s primary sources, tracked down by FBI, said Steele had misreported several of the most troubling allegations of potential Trump blackmail and campaign collusion.
We find human dangles, what Lisa Page referred to as “our OCONUS lures” (OCONUS is spook-speak for Outside CONtinental US) in the form of a shady Maltese academic, Joseph Mifsud, who himself has deep ties to multiple U.S. intel agencies and the Pentagon, paying Trump staffers for nothing speeches to buy access to them. We find a female FBI undercover agent inserted into social situations with a Trump staffer (pillow talk is always a spy’s best friend). It becomes clear the FBI sought to manufacture a foreign counterintelligence threat as an excuse to unleash its surveillance tools against the Trump campaign. … continue reading
December 12, 2019
Posted by aletho |
Deception, Mainstream Media, Warmongering | FBI, GCHQ, United States |
Leave a comment
Two-time Oscar nominee Keira Knightley is known for being in “period pieces” such as “Pride and Prejudice,” so her playing the lead in the new film “Official Secrets,” scheduled to be released in the U.S. on Friday, may seem odd at first. That is until one considers that the time span being depicted — the early 2003 run-up to the invasion of Iraq — is one of the most dramatic and consequential periods of modern human history.
It is also one of the most poorly understood, in part because the story of Katharine Gun, played by Knightley, is so little known. Having followed this story from the start, I find this film to be, by Hollywood standards, a remarkably accurate account of what has happened to date–“to date” because the wider story still isn’t over.
Katharine Gun worked as an analyst for Government Communications Headquarters (GCHQ), the British equivalent of the secretive U.S. National Security Agency. She tried to stop the impending invasion of Iraq in early 2003 by exposing the deceit of George W. Bush and Tony Blair in their claims about that country. For doing that she was prosecuted under the Official Secrets Act — a juiced up version of the U.S. Espionage Act, which in recent years has been used repeatedly by the Obama administration against whistleblowers and now by the Trump administration against WikiLeaks publisher Julian Assange.
Gun was charged for exposing— around the time of Colin Powell’s infamous testimony to the UN about Iraq’s alleged WMDs – a top secret U.S. government memo showing it was mounting an illegal spying “surge” against other U.N. Security Council delegations in an effort to manipulate them into voting for an Iraq invasion resolution. The U.S. and Britain had successfully forced through a trumped up resolution, 1441 in November 2002. In early 2003, they were poised to threaten, bribe or blackmail their way to get formal United Nations authorization for the invasion. [See recent interview with Gun.]

Katherine Gun
The leaked memo, published by the British Observer, was big news in parts of the world, especially the targeted countries on the Security Council, and helped prevent Bush and Blair from getting the second UN Security Council resolution they said they wanted. Veto powers Russia, China and France were opposed as well as U.S. ally Germany.
Washington invaded anyway of course — without Security Council authorization — by telling the UN weapons inspectors to leave Iraq and issuing a unilateral demand that Saddam Hussein leave Iraq in 48 hours— and then saying the invasion would commence regardless.
‘Most Courageous Leak’
It was the executive director of the Institute for Public Accuracy, where I work (accuracy.org), Norman Solomon, as well as Pentagon Papers whistleblower Daniel Ellsberg who in the U.S. most immediately saw the importance of what Gun had done. Ellsberg would later comment: “No one else — including myself — has ever done what Katharine Gun did: Tell secret truths at personal risk, before an imminent war, in time, possibly, to avert it. Hers was the most important — and courageous — leak I’ve ever seen, more timely and potentially more effective than the Pentagon Papers.”
Of course, no one knew her name at the time. After the Observer broke the story on March 1, 2003, accuracy.org put out a series of news releases on it and organized a sadly, sparsely attended news conference with Ellsberg on March 11, 2003 at the National Press Club, focusing on Gun’s revelations. Ellsberg called for more such truth telling to stop the impending invasion, just nine days away.
Though I’ve followed this case for years, I didn’t realize until recently that accuray.org’s work helped compel Gun to expose the document. At a recent D.C. showing of “Official Secrets” that Gun attended, she revealed that she had read a book co-authored by Solomon, published in January 2003 that included material from accuracy.org as well as the media watch group FAIR debunking many of the falsehoods for war.
Gun said: “I went to the local bookshop, and I went into the political section. I found two books, which had apparently been rushed into publication, one was by Norman Solomon and Reese Erlich, and it was called Target Iraq. And the other one was by Milan Rai. It was called War Plan Iraq. And I bought both of them. And I read them cover to cover that weekend, and it basically convinced me that there was no real evidence for this war. So I think from that point onward, I was very critical and scrutinizing everything that was being said in the media.”
Thus, we see Gun in “Official Secrets” shouting at the TV to Tony Blair that he’s not entitled to make up facts. The film may be jarring to some consumers of major media who might think that Donald Trump invented lying in 2017.
Gun’s immediate action after reading critiques of U.S. policy and media coverage makes a strong case for trying to reach government workers by handing out fliers and books and putting up billboards outside government offices to encourage them to be more critically minded.
Solomon and Ellsberg had debunked Bush administration propaganda in real time. But Gun’s revelation showed that the U.S. and British governments were not only lying to invade Iraq, they were violating international law to blackmail whole nations to get in line.
Mainstream reviews of “Official Secrets” still seem to not fully grasp the importance of what they just saw. The trendy AV Club review leads: “Virtually everyone now agrees that the 2003 invasion of Iraq was a colossal mistake based on faulty (at best) or fabricated (at worst) intelligence.” “Mistake” is a serious understatement even with “colossal” attached to it when the movie details the diabolical, illegal lengths to which the U.S. and British governments went to get other governments to go along with it.
Gun’s revelations showed before the invasion that people on the inside, whose livelihood depends on following the party line, were willing to risk jail time to out the lies and threats.
Portrayal of The Observer
Other than Gun herself, the film focuses on a dramatization of what happened at her work; as well as her relationship with her husband, a Kurd from Turkey who the British government attempted to have deported to get at Gun. The film also portrays the work of her lawyers who helped get the Official Secrets charge against her dropped, as well as the drama at The Observer, which published the NSA document after much internal debate.
Observer reporter Martin Bright, whose strong work on the original Gun story was strangely followed by an ill-fated stint at the Tony Blair Faith Foundation, has recently noted that very little additional work has been done on Gun’s case. We know virtually nothing about the apparent author of the NSA document that she leaked — one “Frank Koza.” Other questions persist, such as how prevalent is this sort of U.S. blackmail of foreign governments to get UN votes or for other purposes? How is it leveraged? Does it fit in with allegations made by former NSA analyst Russ Tice about the NSA having massive files on political people?
Observer reporter Ed Vulliamy is energetically depicted getting tips from former CIA man Mel Goodman. There do seem to be subtle but potentially serious deviations from reality in the film. Vulliamy is depicted as actually speaking with “Frank Koza,” but that’s not what he originally reported:
“The NSA main switchboard put The Observer through to extension 6727 at the agency which was answered by an assistant, who confirmed it was Koza’s office. However, when The Observer asked to talk to Koza about the surveillance of diplomatic missions at the United Nations, it was then told ‘You have reached the wrong number’. On protesting that the assistant had just said this was Koza’s extension, the assistant repeated that it was an erroneous extension, and hung up.”
There must doubtlessly be many aspects of the film that have been simplified or altered regarding Gun’s personal experience. A compelling part of the film — apparently fictitious or exaggerated — is a GCHQ apparatchik questioning Gun to see if she was the source.
Little is known about the reaction inside the governments of Security Council members that the U.S. spied on. After the invasion, Mexican Ambassador Adolfo Aguilar Zinser spoke in blunt terms about U.S. bullying — saying it viewed Mexico as its patio trasero, or back yard — and Zinser was compelled to resign by President Vicente Fox. He then, in 2004, gave details about some aspects of U.S. surveillance sabotaging the efforts of the other members of the Security Council to hammer out a compromise to avert the invasion of Iraq, saying the U.S. was “violating the U.N. headquarters covenant.” In 2005, he tragically died in a car crash.
“Official Secrets” director Gavin Hood is perhaps more right than he realizes when he says that his depiction of the Gun case is like the “tip of an iceberg,” pointing to other deceits surrounding the Iraq war. His record with political films has been uneven until now. Peace activist David Swanson, for instance, derided his film on drones, “Eye in the Sky.” At a D.C. showing of “Official Secrets,” Hood depicted those who backed the Iraq war as being discredited. But that’s simply untrue.

Keira Knightley appears as Katherine Gun in Official Secrets (Courtesy of Sundance Institute.)
Leading presidential candidate Joe Biden — who not only voted for the Iraq invasion, but presided over rigged hearings on in 2002 – has recently falsified his record repeatedly on Iraq at presidential debates with hardly a murmur. Nor is he alone. Those refusing to be held accountable for their Iraq war lies include not just Bush and Cheney, but John Kerry and Nancy Pelosi.
Biden has actually faulted Bush for not doing enough to get United Nations approval for the Iraq invasion. But as the Gun case helps show, there was no legitimate case for invasion and the Bush administration had done virtually everything, both legal and illegal, to get UN authorization.
Many who supported the invasion try to distance themselves from it. But the repercussions of that illegal act are enormous: It led directly or indirectly to the rise of ISIS, the civil war in Iraq and the war in Syria. Journalists who pushed for the Iraq invasion are prosperous and atop major news organizations, such as Washington Post editorial page editor Fred Hiatt. The editor who argued most strongly against publication of the NSA document at The Observer, Kamal Ahmed, is now editorial director of BBC News.
The British government — unlike the U.S.– did ultimately produce a study ostensibly around the decision-making leading to the invasion of Iraq, the Chilcot Report of 2016. But that report — called “devastating” by the The New York Times – made no mention of the Gun case. [See accuracy.org release from 2016: “Chilcot Report Avoids Smoking Gun.”]
After Gun’s identity became known, the Institute for Public Accuracy brought on Jeff Cohen, the founder of FAIR, to work with Hollie Ainbinder to get prominent individuals to support Gun. The film — quite plausibly — depicts the charges being dropped against Gun for the simple reason that the British government feared that a high profile proceeding would effectively put the war on trial, which to them would be have been a nightmare.
Sam Husseini is an independent journalist, senior analyst at the Institute for Public Accuracy and founder of VotePact.org. Follow him on twitter: @samhusseini.
August 29, 2019
Posted by aletho |
Deception, Film Review, Mainstream Media, Warmongering, Timeless or most popular | CIA, GCHQ, UK |
Leave a comment