FEMA Allocated $2.6M for “War on Misinformation” Contract in 2023
By Didi Rankovic | Reclaim The Net | February 20, 2025
The Federal Emergency Management Agency (FEMA) – an incorporated agency of the Department of Homeland Security (DHS) – earmarked $2.6 million to fund a “war on misinformation” contract in 2023, according to data on the usaspending.gov website.
The blanket purchase agreement note lists “misinformation, disinformation, and malinformation analysis” as the subjects of the order, with $1.2 million spent, and as much currently listed as the obligated amount.

Screenshot of a USAspending.gov contract summary detailing a completed Blanket Purchase Agreement (BPA) Call awarded by the DHS to Guidehouse Inc., located in McLean, VA.
As noticed by Foundation For Freedom Online, the recipient is the consultancy firm Guildehouse, a government contractor owned by Bain Capital. A post on the company’s website that has since been deleted spoke about Guildehouse engaging with social media platforms to report misinformation (including flagging posts for removal).
Guildehouse also “maintained a proprietary internal database” to track content designated as “misinformation,” and a list of “higher risks” sites that might have published such content.
The case looks like another piece in the puzzle that has been the Big Government-Big Tech collusion to suppress speech in the US, unfolding over the last four years.
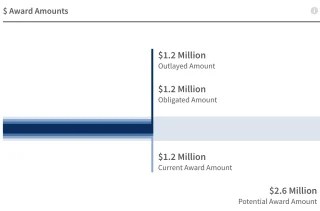
“$ Award Amounts” chart shows $1.2 million as the outlayed amount, $1.2 million as the obligated amount, and $1.2 million as the current award amount, with a potential award amount of $2.6 million.
This one features some recurring, and some new “characters” – but also, sheds more light on what appears to be the former authorities’ painstaking efforts to obfuscate the ties that bound those actors together.
For example, FEMA is not one of the usual entities brought up in Congressional investigations and lawsuits delving deep into that collusion; but it is a sub-agency of the DHS, notorious for things like the failed attempt to set up the Disinformation Governance Board, and even work, in roundabout ways, with the Election Integrity Partnership (EIP).
In 2023, the House Committee on Homeland Security referred to the practice of “delegating” what’s unconstitutional censorship of speech to third parties as, “censorship laundering.”
A group that does often crop up in these probes is the UK-based Center for Countering Digital Hate (CCDH), a pro-censorship group of the “Kill Musk’s Twitter” infamy, which in 2024 organized what reports say was an “exclusive, invite-only” gala.
One of those invited was Erica Mindel – a former member of the Israeli military, a contractor to the US State Department’s envoy monitoring and combating antisemitism – but also, one of Guildehouse’s senior consultants.
A New Year’s Resolution: Let’s Get the United States Out of the Censorship Business
By Jonathan Turley | December 31, 2024
On this New Year’s Eve, billions of people will gather with friends to ring in 2025 with the hope of a better year to come. For the first time in many years, free-speech advocates have a reason to celebrate.
With 2024, we will say goodbye to one of the most reviled offices in the Biden Administration: The Global Engagement Center. I discuss the Center in my recent book, The Indispensable Right: Free Speech in an Age of Rage as one of the most active components in the massive censorship system funded by the Biden Administration. The demise of the GEC is a good start. However, like weight loss resolutions, it will take much more of a commitment if we are going to restore free speech in the United States. It is time to make the ultimate resolution to rip out the censorship root and stem from our government.
This month, the Biden Administration fought to keep the GEC funded, but Republicans refused to include it in the continuing resolution for the budget. However, even with the closure of this one office, Biden will leave behind the most comprehensive censorship system in the history of the United States.
Over the last three years, many of us have detailed a comprehensive system of grants to academic and third party organizations to create blacklists or to pressure advertisers to withdraw support for targeted sites. The subjects for censorship ranged from election fraud to social justice to climate change.
I testified at the first hearing by the special committee investigating the censorship system funded or coordinated by the Biden Administration. It is an unprecedented alliance of corporate, government, and academic groups against free speech in the United States. The Biden Administration established the most anti-free speech record since the Adams Administration.
House investigations showed the critical role played by government officials in “switchboarding,” or channeling demands for removal or bans in social media. Officials evaded the limits of the First Amendment by using these groups as surrogates for censorship.
Even with the elimination of the GEC, other offices remain in various agencies, including the Cybersecurity and Infrastructure Security Agency (CISA) in the Department of Homeland Security, which emerged as one of the critical control centers in this system.
CISA head Jen Easterly declared that her agency’s mandate over critical infrastructure would be extended to include “our cognitive infrastructure.” That includes not just “disinformation” and “misinformation,” but combating “malinformation” – described as information “based on fact, but used out of context to mislead, harm, or manipulate.”
These groups form a censorship consortium where the suppression of speech attracts millions in federal dollars. Election Integrity Partnership (EIP) was created in association with Stanford University “at the request of DHS/CISA.”
EIP supplied a “centralized reporting system” to process what were known as “Jira tickets” targeting unacceptable views. It would include not only politicians but commentators and pundits as well as the satirical site The Babylon Bee.
Stanford’s Virality Project pushed to censor even true facts since “true stories … could fuel hesitancy” over taking the vaccine or other measures. Emails show government officials stressing that they could not be seen as “openly endors[ing]” censorship while other groups sought to minimize public scrutiny of their work.
For example, one article featured the work of Kate Starbird, director and co-founder of the University of Washington Center for an Informed Public. In one communication, Starbird cautioned against giving examples of disinformation to keep them from being used by critics, adding “since everything is politicized and disinformation inherently political, every example is bait.”
Likewise, University of Michigan’s James Park is shown pitching that school’s WiseDex First Pitch program, promising that “our misinformation service helps policy makers at platforms who want to . . . push responsibility for difficult judgments to someone outside the company . . . by externalizing the difficult responsibility of censorship.”
The system has layers of interconnected grants and systems. For example, the EIP worked with the Global Engagement Center that contracted with the Atlantic Council in censorship efforts.
The censorship system included scoring groups through a grant from the National Endowment for Democracy (NED) to the British-based Global Disinformation Index (GDI). The index targeted ten conservative and libertarian sites as the most dangerous sources of disinformation, including sites like Reason which publishes conservative legal analysis. Conversely, some of the most liberal sites were ranked as the most trustworthy for advertisers.
The system is still in place, but on December 23, 2024, the GEC closed its doors. That is something to celebrate but not something to take as great comfort. This is a redundant and overlapping system created precisely to allow for such attrition.
Years ago, some of us wrote about the creation of the infamous Disinformation Governance Board at Homeland Security under its so-called “Disinformation Nanny,” Nina Jankowicz. When the Biden administration caved to public outcry and disbanded the Board, many celebrated. However, as I previously testified, the Biden Administration never told the public about a far larger censorship effort in other agencies, including an estimated 80 FBI agents secretly targeting citizens and groups for disinformation.
The system has functioned like a multiheaded hydra where cutting off one head only allows two more to grow back. These censors will not simply walk away and become dentists or bartenders. They have a skill set for censorship and this is now a profitable industry supporting scores of people who now market themselves as “disinformation specialists.”
Shutting down the GEC will eliminate a $61 million budget and 120 employees. However, these employees will find ample opportunities not just in other agencies but in academia and state agencies. There are also pro-censorship sites like BlueSky, which are becoming safe spaces for liberals who do not want to be “triggered” by opposing views . (Notably, BlueSky hired a former Twitter employee who was fired after Musk cleaned out at what is now X).
They are not going anywhere unless the Trump Administration and the Congress makes free speech a priority in eliminating each of these funding sources.
As I wrote in the book, we need to get the United States out of the censorship business by passing a law barring any federal funds for the use of censorship, including grants to academic and NGO groups.
Rooting out this censorship system will require a comprehensive effort by the new Trump Administration. So here is a resolution that I hope many in the Trump Administration will share: let’s get the United States out of the censorship business in 2025.
“Shutting Down CISA” Senator Rand Paul’s Crusade Against Online Censorship
By Didi Rankovic | Reclaim The Net | November 19, 2024
Senator Paul Rand, who is about to take over as chair of the US Senate Committee on Homeland Security and Governmental Affairs, has spoken in favor of shutting down the Cybersecurity and Infrastructure Security Agency (CISA).
CISA, a part of the Department of Homeland Security (DHS), was established in 2018 to do just what its name says – but has in the meanwhile become weaponized to suppress free speech, opponents believe, citing a number of programs where CISA was involved in monitoring and flagging online posts for removal.
Senator Paul refers to the agency’s behavior – which he says included the ability to censor content and thus influence what information is available to people – as “intrusions into the First Amendment.”
“The First Amendment is important, that’s why we listed it as the First Amendment. I’d like to, at the very least, eliminate their ability to censor content online,” Paul said in a post on X.
The senator was referencing his previous statements made for Politico, when he revealed he is in favor of shuttering CISA completely, while at the same time conceding that this is “unlikely” to happen – but also promising there will be hearings, as the incoming committee starts probing this government entity “working” with social media.
According to Politico, Democrats in Congress would react “fiercely” against any attempt not only to dismantle but also to limit CISA’s powers.
CISA representatives, like senior adviser Ron Eckstein, continue to claim that the agency is merely doing its job, without ever overstepping the mandate and engaging in censorship. Quite the contrary, Eckstein told the press – according to him, CISA is in fact protecting Americans’ “freedom of speech, civil rights, civil liberties, and privacy.”
Taking into account what has come to light regarding CISA’s activities over the past four years in particular, that is an extraordinary claim, and one Senator Paul clearly disagrees with.
Even though established under President Trump’s first administration, CISA assumed an active role around the highly contentious 2020 election, allegedly to suppress those voicing their concerns online about the legitimacy of the vote.
CISA and legacy media supporting the policies the agency is executing – or has been until now – describe this as “countering domestic disinformation,” and suggest that CISA is these days more focused on fighting back adversaries from abroad.
Government and Private Groups Still Unite to Target Election “Misinformation”
By Didi Rankovic | Reclaim The Net | August 27, 2024
The Cybersecurity and Infrastructure Security Agency (CISA) – a part of the US Department of Homeland Security (DHS) – has been enlisting private entities to help achieve one of its goals.
According to CISA, it would be to combat election misinformation and secure “election infrastructure” – while according to critics, it is to continue with the mission of censoring lawful speech “disfavored” by the current authorities seeking to remain where they are after November – by hook or crook.
CISA doesn’t feel the need to hide this activity that has been taking place since 2018 through a program called the Election Infrastructure Subsector Coordinating Council (SCC). It is here that US government entities – federal, state, and local – meet private groups (“partners” as CISA calls them).
We obtained the latest document for you here.
What’s coordinated here, according to the agency, and as was reported by The Federalist, is the reduction of “cyber, physical, and operational security risks to election infrastructure.” The coordination is done to the point where government and private sector have adopted “a unified approach.”
Information sharing ahead of the presidential election is also happening as SCC works with the Government Coordinating Council (GCC).
According to CISA, this collaboration is now “unprecedented” while what is referred to as “private sector owners and operators” sit, as part of SCC, in meetings with the FBI and election officials.
But CISA has other partners – the Election Integrity Project (EIP), formed months before the 2020 election, which has been blasted by the House Judiciary Committee as a tool for the government to bypass the First Amendment and censor speech.
The CISA site has a document, “Mis-, Dis-, and Malinformation: Planning and Incident Response Guide for Election Officials,” put together by CISA/GCC Joint Mis/Disinformation Working Group.
In it, CISA “defines” what each of its targets is supposed to be, and ends up doing what all “misinformation warriors” do – offer subjective and broad descriptions susceptible to interpretation, instead of clear definitions.
For example, “malinformation” is said to be information “based on fact, but used out of context to mislead, harm, or manipulate.”
The document mentions “delegitimization of election results” as one form of mis, dis, and mal information.
It’s unclear if CISA has both 2016 and 2020 elections in mind – or only one – but this is how the activity is described: “Narratives or content that delegitimizes election results or sows distrust in the integrity of the process based on false or misleading claims.”
Former Biden Homeland Security Official Criticizes Free Speech, Cites “Disinformation” Impact on Election Security
By Didi Rankovic | Reclaim The Net | May 28, 2024
 A former Biden administration official has declared that disinformation around elections is “becoming the norm rather than the exception.”
A former Biden administration official has declared that disinformation around elections is “becoming the norm rather than the exception.”
Samantha Vinograd, until recently of the Department of Homeland Security (DHS), also asserted that these days, because of what she considers to be election disinformation, “there is an unprecedented level of physical threats” while the US information ecosystem is “incredibly vulnerable.”
Dramatic and alarmist statements like this may be necessary to justify the rest of Vinograd’s message, which in effect attacks free speech, as it is legally protected in the US.
Appearing on CBS, Vinograd – who was until last December Assistant Secretary of Homeland Security for Counterterrorism and Threat Prevention – warned that the First Amendment might protect free speech, but that engaging in free speech is apparently not “cost-free.”
The Face the Nation hosts framed the problem as, essentially, federal laws (the Constitution) protecting speech, but the damage being done at the state level – and then what states, who organize elections, can do to fix that “problem.”
Spreading lies about candidates, as they put it, was given as an example of legal, protected speech becoming an issue by having the ability to create “a threat at the state level” – and asked Vinograd who she thought was supposed to correct the situation.
Vinograd – who has been bouncing between various administrations (including those of Bush and Obama, and private companies like Goldman Sachs and Stripe before landing at Biden’s DHS) – seemed to suggest that Big Tech (i.e., social media companies) should be assisting the government.
The federal government said Vinograd, “should not be the omnipresent fact checker for the American people.”
And even though, according to her, the government is debunking information about elections that is deemed to be inaccurate, social media companies “should be thinking about what kinds of election disinformation violate their terms of service.”
It’s difficult not to take this as a not-so-veiled added pressure on social platforms to not only continue with censoring content but perhaps expand it in terms of what qualifies as election disinformation.
Either way, Vinograd is in favor of enlisting “every American” to help out as well (although it is not clear in what specific way), invoking even the concept of patriotic duty.
And Vinograd did not miss the opportunity to assert that election misinformation threats are now of such magnitude as to present a national security issue.
‘If We Get Away With It, It’s Legal’: Documents Reveal New Details on U.S. Government’s ‘Censorship-Industrial Complex’
By Michael Nevradakis, Ph.D. | The Defender | November 29, 2023
Government agencies, private-sector firms, academia and nonprofits were collaborating to combat alleged “misinformation” and “disinformation” as far back as 2017, according to new documents released Tuesday.
The “CTIL Files” — which refer to the Cyber Threat Intelligence League, or CTI League, a key player in the so-called “Censorship-Industrial Complex” — are based on documents received from an unnamed but “highly credible” whistleblower, according to investigative journalists Michael Shellenberger, Alex Gutentag and Matt Taibbi, who released the files.
The new documents rival or exceed the “Twitter Files” and “Facebook Files” in “scale and importance,” according to the journalists, two of whom — Shellenberger and Taibbi — were instrumental in releasing many of the “Twitter Files” that first called attention to the “Censorship-Industrial Complex.”
A comprehensive picture of the birth of the ‘anti-disinformation’ sector
The documents, which the journalists detailed on Substack, center around the activities of the CTI League, which “officially began as the volunteer project of data scientists and defense and intelligence veterans but whose tactics over time appear to have been absorbed into multiple official projects, including those of the Department of Homeland Security (DHS).”
According to the journalists, the CTI League documents “offer the missing link … to key questions not addressed in the Twitter Files and Facebook Files” and “offer a comprehensive picture of the birth of the ‘anti-disinformation’ sector.”
“The whistleblower’s documents describe everything from the genesis of modern digital censorship programs to the role of the military and intelligence agencies, partnerships with civil society organizations and commercial media, and the use of sock puppet accounts and other offensive techniques,” the journalists wrote.
Documents in the “CTIL Files” show members of the CTI League, DHS officials and key figures from social media companies “all working closely together in the censorship process.”
This “public-private model” laid the groundwork for “anti-misinformation” and “anti-disinformation” campaigns launched by the U.S. and U.K. governments in 2020 and 2021, the journalists wrote, including attempts to circumvent First Amendment protections against government censorship of speech in the U.S.
Such tactics included “masking censorship within cybersecurity institutions and counter-disinformation agendas; a heavy focus on stopping disfavored narratives, not just wrong facts; and pressuring social media platforms to take down information or take other actions to prevent content from going viral,” they added.
The CTI League went still further though, the journalists wrote, engaging “in offensive operations to influence public opinion, discussing ways to promote ‘counter-messaging,’ co-opt hashtags, dilute disfavored messaging, create sock puppet accounts, and infiltrate private invite-only groups.”
Such censorship lies at the heart of Missouri et al. v. Biden et al., a First Amendment censorship case where injunctions were issued against several federal agencies and government officials, barring them from communicating with social media companies regarding user content. The injunctions are now under review by the U.S. Supreme Court.
Former British intelligence analyst charged with creating counter-disinformation project
The journalists wrote that while previous releases of the “Twitter Files” and “Facebook Files” revealed “overwhelming evidence of government-sponsored censorship,” they had not revealed “where the idea for such mass censorship came from.”
The whistleblower alleged that a key figure in the CTI League, “a ‘former’ British intelligence analyst, was ‘in the room’ at the Obama White House in 2017 when she received the instructions to create a counter-disinformation project to stop a ‘repeat of 2016.’”
By 2019, this analyst, Sara-Jayne “SJ” Terp, had “developed the sweeping censorship framework,” leading a team of U.S. and U.K. “military and intelligence contractors” who “co-led CTIL.” Previously, in 2018, Terp attended a 10-day military exercise organized by the U.S. Army Special Operations Command, according to the journalists.
It was there that Terp met Pablo Breuer, a former U.S. Navy commander, who became a key figure in the CTI League. According to Wired, the two realized that misinformation “could be treated … as a cybersecurity problem.” This led to the development of CogSec, which soon housed the “MisinfoSec Working Group.”
“Terp’s plan, which she shared in presentations to information security and cybersecurity groups in 2019, was to create ‘Misinfosec communities’ that would include government,” the journalists wrote.
By spring 2020, it appears Terp achieved this plan, as the CTI League partnered with the Cybersecurity and Infrastructure Security Agency (CISA), which has been implicated in prior releases of the “Twitter Files” for its role in the “Censorship-Industrial Complex.”
The MisinfoSec Working Group included Renee DiResta, a former CIA operative who worked for the Election Integrity Partnership (EIP) — later renamed the Virality Project (VP). This group “created a censorship, influence, and anti-disinformation strategy called Adversarial Misinformation and Influence Tactics and Techniques (AMITT).”
According to the journalists, AMITT adapted “a cybersecurity framework developed by MITRE, a major defense and intelligence contractor that has an annual budget of $1 to $2 billion in government funding.” MITRE is a backer of the Vaccination Credential Initiative and the SMART Health Card — a digital “vaccine passport.”
Terp used AMITT to develop the DISARM framework, which the World Health Organization (WHO) applied in “countering anti-vaccination campaigns across Europe.”
The same framework “has been formally adopted by the European Union and the United States as part of a ‘common standard for exchanging structured threat information on Foreign Information Manipulation and Interference’” according to the journalists.
‘Can we get a troll on their bums?’
According to the journalists, MisinfoSec’s motivation for counter-misinformation was the “twin political earthquakes of 2016: Brexit and the election of Trump.”
“There’s something off kilter with our information landscape,” Terp and other CTI League members wrote, according to documents.
“The usual useful idiots and fifth columnists — now augmented by automated bots, cyborgs and human trolls — are busily engineering public opinion, stoking up outrage, sowing doubt and chipping away at trust in our institutions. And now it’s our brains that are being hacked,” they added.
In spring 2020, the CTI League set its sights on COVID-19-related narratives, targeting users who engaged in messaging that ran contrary to official policy.
“CTIL began tracking and reporting disfavored content on social media, such as anti-lockdown narratives like ‘all jobs are essential,’ ‘we won’t stay home,’ and ‘open America now,’” the journalists wrote.
“CTIL created a law enforcement channel for reporting content as part of these efforts. The organization also did research on individuals posting anti-lockdown hashtags … and kept a spreadsheet with details from their Twitter bios. The group also discussed requesting ‘takedowns’ and reporting website domains to registrars,” they added.
Regarding the “we won’t stay home” narrative, internal documents revealed by the whistleblower showed that CTI League members wrote, “Do we have enough to ask for the groups and/or accounts to be taken down or at a minimum reported and checked?” and “Can we get all troll on their bums if not?”
They also called posters circulating online promoting anti-lockdown posters “disinformation artifacts,” saying, “We should have seen this one coming” and asking “can we stop the spread, do we have enough evidence to stop superspreaders, and are there other things we can do (are there countermessagers we can ping etc).”
During CTI League brainstorming sessions to develop strategies for “counter-messaging for things like encouraging people to wear masks,” statements such as “Repetition is truth” were uttered by CTI League staff, the journalists noted.
The CTI League also sought to go “beyond simply urging Twitter to slap a warning label on Tweets, or to put individuals on blacklists.”
According to the journalists, “The AMITT framework calls for discrediting individuals as a necessary prerequisite of demanding censorship against them” and “trying to get banks to cut off financial services to individuals who organize rallies or events.”
As part of these efforts, even truthful information was targeted. In a 2019 podcast on “Disinformation, Cognitive Security, and Influence,” Terp admitted, “Most information is actually true … but set in the wrong context.”
“You’re not trying to get people to believe lies most of the time,” she said. “Most of the time, you’re trying to change their belief sets. And in fact, really deeper than that, you’re trying to change, to shift their internal narratives … the set of stories that are your baseline for your culture.”
Previous “Twitter Files” releases have revealed that true information was targeted for censorship by the U.S. government and social media platforms like Twitter if the information contradicted official policy regarding COVID-19 vaccines and restrictions.
‘Cognitive security’ a euphemism for censorship
In the same podcast, according to the journalists, Terp said, “Cognitive security is the thing you want to have. You want to protect that cognitive layer. It basically, it’s about pollution. Misinformation, disinformation is a form of pollution across the Internet.”
The journalists wrote, “A key component of Terp’s work through CTIL, MisinfoSec, and AMITT was to insert the concept of ‘cognitive security’ into the fields of cybersecurity and information security.”
Such “cognitive security” was seen as being threatened by the erosion of the mass media’s control on information and influence over public opinion.
Documents revealed by the whistleblower included a MisinfoSec report stating “For a long time, the ability to reach mass audiences belonged to the nation-state (e.g. in the USA via broadcast licensing through ABC, CBS and NBC).”
“Now, however, control of informational instruments has been allowed to devolve to large technology companies who have been blissfully complacent and complicit in facilitating access to the public for information operators at a fraction of what it would have cost them by other means,” the report said.
The same report also called for a form of “pre-bunking,” to “preemptively inoculate a vulnerable population against messaging,” suggesting that DHS-funded Information Sharing and Analysis Centers could be used to promote such pre-bunking.
‘If we get away with it, it’s legal’
Public-private partnerships were specifically sought out in an attempt to circumvent First Amendment free speech protections in the U.S., the documents revealed, even while Bloomberg, The Washington Post and Wired wrote glowing articles portraying the CTI League as a mere group of “volunteer” cybersecurity experts.
Yet, according to the journalists, “In just one month, from mid-March to mid-April [2020], the supposedly all-volunteer CTIL had grown to ‘1,400 vetted members in 76 countries’” and had “helped to take down 2,833 cybercriminal assets on the internet” including some which impersonated government organizations, the United Nations and WHO.
On the same 2019 podcast, according to the journalists, Breuer explained how the CTI League was getting around the First Amendment, by working to get “nontraditional partners into one room,” including “maybe somebody from one of the social media companies, maybe a few special forces operators, and some folks from Department of Homeland Security.”
Together, they would “talk in a non-attribution, open environment in an unclassified way so that we can collaborate better, more freely and really start to change the way that we address some of these issues,” Breuer said.
Breuer even likened these tactics to those employed by the Chinese government, saying “If you talk to the average Chinese citizen, they absolutely believe that the Great Firewall of China is not there for censorship. They believe that it’s there because the Chinese Communist Party wants to protect the citizenry and they absolutely believe that’s a good thing.”
“If the US government tried to sell that narrative, we would absolutely lose our minds and say, ‘No, no, this is a violation of our First Amendment rights.’ So, the in-group and out-group messaging have to be often different,” he said.
The whistleblower told the journalists that CTI League leaders did not discuss their potential violation of the First Amendment.
“The ethos was that if we get away with it, it’s legal, and there were no First Amendment concerns because we have a ‘public-private partnership’ — that’s the word they used to disguise those concerns. ‘Private people can do things public servants can’t do, and public servants can provide the leadership and coordination,’” the whistleblower said.
According to the journalists, the authors of the MisinfoSec report also “advocated for police, military, and intelligence involvement in censorship, across Five Eyes nations, and even suggested that Interpol should be involved.”
The CTI League documents also suggest that the organization was involved in a form of domestic spying, with one document noting that while censorship activities abroad are “typically” performed by “the CIA and NSA and the Department of Defense,” such efforts “against Americans” necessitate the use of private partners because the government lacks the “legal authority” to do so.
According to the whistleblower, CTI League members also went to great lengths to conceal their activities, with a CTI League handbook recommending the use of burner phones, online pseudonyms and the generation of fake AI faces. One document advised, “Lock your s**t down … your spy disguise.”
One suggested list of questions to be posed to prospective CTI League members proposed asking whether those individuals had ever “worked with influence operations (e.g. disinformation, hate speech, other digital harms etc) previously” and whether those efforts included “active measures” and “psyops” (psychological operations).
Indeed, according to the documents, several CTI League members had worked for the military or intelligence agencies, while according to the whistleblower, “roughly 12-20 active people involved in CTIL worked at the FBI or CISA” — even, for a time, displaying their agency seals alongside their names on the CTI League’s internal Slack channel.
Terp, for instance, previously designed machine learning algorithms and unmanned vehicle systems for the U.K.’s Ministry of Defence.
According to the whistleblower, the CTI League sought “to become part of the federal government.”
Shellenberger, Taibbi to testify before Congress this week
According to the journalists, the FBI declined to comment, while CISA, Terp and other CTI League figures did not respond to requests for comment.
However, one CTI League member, Bonnie Smalley, did respond to the journalists’ request. She wrote, verbatim, “all i can comment on is that i joined cti league which is unaffiliated with any govt orgs because i wanted to combat the inject bleach nonsense online during covid. … i can assure you that we had nothing to do with the govt though.”
“CTIL appears to have generated publicity about itself in the Spring and Fall of 2020 for the same reason EIP did: to claim later that its work was all out in the open and that anybody who suggested it was secretive was engaging in a conspiracy theory,” the journalists wrote.
“But as internal messages have revealed, much of what EIP did was secret, as well as partisan, and demanding of censorship by social media platforms, contrary to its claims,” they said, adding that “EIP and VP, ostensibly, ended, but CTIL is apparently still active, based on the LinkedIn pages of its members.”
The journalists said the documents will be presented to Congressional investigators and made public, while protecting the identity of the whistleblower.
Shellenberger and Taibbi will testify at Thursday’s hearing of the U.S. House of Representatives’ Select Subcommittee on the Weaponization of the Federal Government. They previously testified before the same committee in March.
On Tuesday, Taibbi appeared in a live YouTube webcast presenting some of the key revelations from the first release of the “CTIL Files.”
Michael Nevradakis, Ph.D., based in Athens, Greece, is a senior reporter for The Defender and part of the rotation of hosts for CHD.TV’s “Good Morning CHD.”
This article was originally published by The Defender — Children’s Health Defense’s News & Views Website under Creative Commons license CC BY-NC-ND 4.0. Please consider subscribing to The Defender or donating to Children’s Health Defense.
US House Panel Says Disinformation ‘Pseudo-Experts’ Targeted Political Speech Online
Sputnik – 07.11.2023
WASHINGTON – US government officials used a government-linked group of disinformation pseudo-experts to launder the censorship of political speech online, the US House Select Subcommittee on the Weaponization of the Federal Government said in an interim report.
The Election Integrity Partnership (EIP) – a group of purported disinformation academics led by the Stanford Internet Observatory – worked with US government officials to monitor and censor online speech ahead of the 2020 presidential election, the report, released Monday, said.
“This interim staff report details the federal government’s heavy-handed involvement in the creation and operation of the EIP, which facilitated the censorship of Americans’ political speech in the weeks and months leading up to the 2020 election,” the report said. “This pressure was largely directed in a way that benefited one side of the political aisle: true information posted by Republicans and conservatives was labeled as ‘misinformation’ while false information posted by Democrats and liberals was largely unreported and untouched by the censors.”
The House Weaponization Subcommittee released the report in conjunction with the House Judiciary Committee.
The EIP worked with the US Department of Homeland Security and other US government agencies to bypass First Amendment protections for speech through the consortium of disinformation “pseudo-experts,” the report said.
The EIP was created at the request of the US Cybersecurity and Infrastructure Security Agency, the report said. US government officials would submit misinformation reports to EIP analysts, who would then recommend censorship actions to tech companies, the report added.
An “untold number” of US citizens across the political spectrum were impacted by the censorship of true information, jokes and opinions, the report said.
The House committees’ investigations into the weaponization of the federal government and violations of civil liberties remain ongoing, the report said. There is “more to come,” Judiciary and Weaponization panel chair Jim Jordan also said in a statement via social media platform X.
The American people deserve to know whether they were targeted by the US government and affiliated disinformation pseudo-experts, Jordan added.
FBI = Following Biden’s Instructions?
By James Bovard | October 30, 2023
Does “FBI” now stand for “Following Biden’s Instructions”? The FBI is doing backflips to boost Joe Biden’s re-election campaign. Unfortunately, federal courts don’t recognize law enforcement shenanigans as a violation of the Voting Rights Act.
The FBI is categorizing Donald Trump’s supporters as terrorist suspects, according to a new report in Newsweek. The FBI created “a new category of extremists that it seeks to track and counter: Donald Trump’s army of MAGA followers,” Newsweek revealed. The FBI is relying on the same counterterrorism methods honed to fight al Qaeda to go after the incumbent president’s political opponents.
Naturally, the latest Washington crusade against extremism has more malarkey than a White House summit. Federal bureaucrats heaved together a bunch of letters to contrive an ominous new acronym for the latest peril to domestic tranquility. The result: AGAAVE—“anti-government, anti-authority violent extremism”—which looks like a typo for a sugar substitute.
Recently, the FBI vastly expanded the supposed AGAAVE peril by broadening suspicion from “furtherance of ideological agendas” to “furtherance of political and/or social agendas.” Anyone who has an agenda different from Team Biden’s could be AGAAVE’d for his own good. The great majority of the FBI’s “current ‘anti-government’ investigations are of Trump supporters,” William Arkin, a highly respected investigative journalist, reported in Newsweek.
The FBI crackdown is following some of the most overheated political rhetoric of our era. Biden has denounced Trump supporters for “semi-fascism.” Biden tweeted last November, “Donald Trump and MAGA Republicans are a threat to the very soul of this country.”
Biden’s Homeland Security Advisor Liz Sherwood-Randall declared, “The use of violence to pursue political ends is a profound threat to our public safety and national security… it is a threat to our national identity, our values, our norms, our rule of law—our democracy.” And since Team Biden says that Trump supporters could be violent, suppressing them is the only way to protect “the will of the people” or whatever honorific is used for rigged election results.
In June, the FBI and Department of Homeland Security issued a warning: “Sociopolitical developments—such as narratives of fraud in the recent general election, the emboldening impact of the violent breach of the U.S. Capitol, conditions related to the COVID-19 pandemic, and conspiracy theories promoting violence—will almost certainly spur some domestic terrorists to try to engage in violence.” In other words, alleging that there was election fraud in past elections can qualify a person as a terrorist suspect—and justify suppressing their political activity in subsequent elections.
Biden’s FBI views Trump supporters as a deadly threat to democracy, thereby justifying subverting or crippling Trump supporters’ ability to oppose Biden and other Democrats.
The FBI is required to have (or claim to have) solid information before launching a criminal investigation. But the bureau needs almost zero information to open an “assessment.” The FBI conducted more than 5,500 domestic-terrorism “assessments” in 2021, a 10-fold increase since 2017 and a 50-fold increase since 2013. “Assessments are the closest thing to domestic spying that exists in America and generally not talked about by the Bureau,” Arkin noted. The House Weaponization Subcommittee warned that “the FBI appears to be complicit in artificially supporting the Administration’s political narrative” that domestic violent extremism is “the ‘greatest threat’ facing the United States.”
Those assessments could prove perilous because the official demand for terrorists far exceeds the domestic supply. A top federal official told Newsweek last year, “We’ve become too prone to labeling anything we don’t like as extremism, and then any extremist as a terrorist.” “Trespassing plus thought crimes equals terrorism” is the Biden standard for prosecuting January 6 defendants.
FBI whistleblower Steve Friend complained of current FBI leadership, “There is this belief that half the country are domestic terrorists and we can’t have a conversation with them. There is a fundamental belief that unless you are voicing what we agree…you are the enemy.”
Did the Biden administration secretly want Newsweek to vindicate the fears of legions of Trump supporters? Perhaps those “assessments” are repeating a tactic used against Vietnam War protesters: FBI agents were encouraged to conduct frequent interviews with antiwar activists to “enhance the paranoia endemic in such circles” and “get the point across that there is an FBI agent behind every mailbox,” according to an FBI memo from that era.
The more abusive the FBI becomes, the more outraged that Trump supporters sound, thereby justifying further FBI repression. That also makes it easier for Team Biden to portray Trump supporters as public menaces.
Biden’s war on extremism could become a self-fulfilling prophecy that destroys American political legitimacy. An official in the Office of Director of National Intelligence lamented, “So we have the president increasing his own inflammatory rhetoric which leads Donald Trump and the Republicans to do the same”—and the media follow suit. Biden is exempt from official suspicion even when he denounced Republicans as fascists who want to destroy democracy. Yet if Republicans sound equally overheated, Biden’s FBI has pretexts to unleash the hounds.
Is there any limit to the federal entrapment operations designed to spur headlines that make politicians applaud? The latest FBI crackdown echoes a DHS campaign that was leaked to the press in 2021. Federal policymakers launched a “legal work-around” to spy on and potentially entrap Americans who are “perpetuating the ‘narratives’ of concern,” CNN reported. The DHS plan would “allow the department to circumvent [constitutional and legal] limits” on surveillance of private citizens and groups. Federal agencies are prohibited from targeting individuals solely for First Amendment-protected speech and activities. But federal hirelings would be under no such restraint.
Will the FBI’s interventions in the 2024 presidential election be even more brazen than its 2016 and 2020 stunts? Will the agency exploit its “assessments” to recruit knuckleheads to engage in another pre-election Keystone Kops plot to kidnap a governor, as it did in Michigan in 2020?
The FBI has a sordid history of intervening in presidential elections since 1948—if not before. A 1976 Senate report on FBI abuses warned, “The American people need to be assured that never again will an agency of the government be permitted to conduct a secret war against those citizens it considers threats to the established order.” Unfortunately, Americans may not learn the damning details of another FBI “secret war” until long after the next election.
Ironically, the Biden administration is vilifying anti-government opinions at the same time judges are exposing federal crimes. Federal court decisions in July and September condemned the Biden censorship regime—and those rulings were preceded by Supreme Court decisions striking down President Joe Biden’s student-loan-forgiveness scheme and vaccine mandates.
But Team Biden still presumes anyone who suspects the feds are violating the Constitution is up to no good. In the same way that Biden based his 2020 election campaign on vilifying Charlottesville 2017 protests, so the Biden re-election campaign will vilify anyone who distrusts the feds. Regardless of the outcome, the 2024 election will be another boomtime for cynics.
DHS still withholding information in its efforts to censor “misinformation, disinformation, and malinformation”
By Tom Parker | Reclaim The Net | September 22, 2023
The Department of Homeland Security (DHS) is continuing to hold back information about its efforts to police online speech in response to Freedom of Information Act (FOIA) requests.
The Americans For Prosperity (AFP) Foundation, a political advocacy group, has spent years attempting to get the DHS to hand over records on its efforts to censor “misinformation, disinformation, and malinformation.” However, the DHS has responded by heavily redacting any records it turns over to the group.
The DHS is citing FOIA Exemption 7(E), which protects “techniques and procedures for law enforcement investigations or prosecutions,” to justify the redactions.
Kevin Schmidt, the Director of Investigations at AFP, blasted the DHS for obfuscating the contents of the documents.
“If DHS believes it has the authority to police people’s online speech, it should be open with the public about what those authorities are,” he said.
He added that the DHS’s use of FOIA Exemption 7(E) “suggests the DHS is either overstating its authorities or it’s abusing FOIA exemptions to avoid transparency.”
Despite the heavy redactions, the documents do show the DHS arguing it has the authority to target “MDM” — its acronym for misinformation, disinformation, and malinformation.
Another document shows that the DHS’s Disinformation Governance Board had a “Ukraine MDM Playbook” before it was shut down.
The AFP Foundation isn’t the only entity that’s struggled to get the DHS to hand over information on its speech policing activities. It has previously stonewalled Congress’s attempts to get details on the DHS’s “anti-disinformation” practices.
Additionally, the DHS has been accused of attempting to avoid transparency by using channels such as Slack and personal cellphones to hold meetings about its misinformation efforts.
Republicans Move To Prevent Bodies Like a Disinformation Governance Board From Ever Being Created
By Dan Frieth | Reclaim The Net | September 18, 2023
Legislation that seeks to tie the hands of the Department of Homeland Security (DHS) from setting up another Disinformation Governance Board is being launched by House Republicans. Brought about by Representatives Marjorie Taylor Greene, Ronny Jackson, and August Pfluger, this move is viewed as the Party’s effort to block limitations on what it deems to be free speech by federal agencies.
The DHS had originally set up a Disinformation Governance Board with a view to counteract, as it claimed, misinformation, malformation and disinformation. Yet, the initiative was met with criticism from conservative groups, leading to the body’s disbandment in 2022. Concerns centered around allegations of stifled free speech and political bias, rather than a focus on national security issues.
Representative Pfluger, who is part of the Homeland Security Committee along with Greene, expressed his skepticism about the previous governance board to The Washington Examiner.
According to him, it was less about maintaining factual discourse and more about controlling public discourse. He described the administration’s attempt to oversee American’s speech as discouraging, adding that the DHS’ energy should rather be directed to improving national security.
“Partisan government officials running a ‘disinformation board’ sounds ridiculous to most people, but yet the Biden administration tried to control the speech of American citizens… DHS should be focused on securing the border and preventing terrorist attacks, not fact-checking social media and censoring Americans.”
Republicans are progressively striking back against attempts by the current administration to regulate alleged disinformation. They are backing funding bills that effectively cut the government’s opportunities to bankroll these programs. This resistance to censorship extends beyond domestic boundaries, with the GOP-led House Foreign Affairs Committee considering refusing authorization to the Global Engagement Center, a State Department-associated body.
It was revealed that this body had funneled $100,000 towards the British-based Global Disinformation Index which allegedly stealthily blacklisted conservative channels. Moreover, this isn’t the GOP’s debut attempt to disable the DHS from governing a disinformation board.
Billionaire Biden Donor Bankrolled 2020 Election Social Media Censorship Effort
BY LEE FANG | JUNE 8, 2023
The Department of Homeland Security’s controversial social media censorship effort during the 2020 election was propped up by a partisan billionaire.
Newly obtained documents, acquired through a public records request, confirm that Pierre Omidyar, the billionaire founder of eBay, financed a specialized portal maintained by the Center for Internet Security (CIS). This portal was used to facilitate the swift removal of predominantly conservative messages on Twitter and Facebook during the previous presidential election.
Omidyar, previously identified as one of the largest donors to campaign groups supporting Joe Biden’s presidential bid, donated $45 million to the “Sixteen Thirty Fund” in 2020. This dark money group mobilized Democratic voters and financed pro-Biden Super PACs. However, Omidyar’s direct involvement in the DHS partnership, which is now facing increased scrutiny, remained undisclosed until now.
The funding provided by Omidyar to CIS was used to establish a Misinformation Reporting Portal (MiRP). A team from CIS continuously monitored this portal 24/7 from September 28 to November 6, 2020, as revealed in a post-election report, “Election Infrastructure Misinformation Reporting.” The Democracy Fund, Omidyar’s foundation, supported the creation of the MiRP through a direct grant, according to the report.
The misinformation reporting portal served to rapidly identify and remove instances of alleged misinformation. CIS’s report acknowledged that the flagged content ranged from “intentional misinformation to honest mistakes.” Of the content reported by CIS, 61% “resulted in positive action,” which the group defined as content takedowns or labeling.
This MiRP system was used by a coalition of liberal-leaning research groups and overseen by the Cybersecurity and Infrastructure Agency (CISA), a sub-agency of the DHS that has led the government’s push to censor social media. Despite government backing for the project, the effort was partisan – the Democratic National Committee was part of the consortium, but not the Republican National Committee, indicating a partisan bias.
“In addition to sharing all reports with CISA, some reports were shared with the Federal Bureau of Investigation,” the CIS report noted. The effort focused on “election narratives” deemed conspiratorial or inaccurate.
Tax records appear to confirm the Omidyar funding. The Democracy Fund’s 990 disclosure shows that it donated $130,000 to CIS in 2020. The grant, however, is listed as support for “election security best practices,” a vague description that belied the true function of the MiRP portal.
CIS did not respond to a request for comment. The Omidyar Network discussed this inquiry with me but stopped responding before publication.
Evidence of this MiRP system first emerged in emails I obtained from a visit to Twitter’s San Francisco headquarters in December. In an email thread dated October 1, 2020, Twitter attorney Stacia Cardille mentioned receiving outreach from DHS, forwarding a censorship demand from CISA, CIS official Aaron Wilson, and a representative from the Election Integrity Partnership, a coalition monitoring misinformation.
The alleged misinformation mentioned in the October 1 thread revolved around conservative warnings regarding potential risks associated with mail-in voting—a concern voiced by partisans from both sides. Twitter, however, took action against conservative accounts but did not similarly act against Democrats who warned against mail-in ballots, as I’ve previously reported. For instance, former D.N.C. chairman Howard Dean tweeted during the election: “Do not vote by mail. Ok to vote now early and drop your ballot off in person at the proper office. Too late to trust trumps postmaster thug.”
The Dean tweet was noted by Twitter’s content moderation team but no action was taken, while similar messages warning against mail-in voting from conservative accounts were censored.
The CIS report provides a comprehensive explanation of the public-private apparatus employed to influence content on social media. In doing so, the report also debunks recent myths. In April, MSNBC host Mehdi Hasan made a false claim that journalist Matt Taibbi deliberately misrepresented his case under oath during his congressional testimony on CISA’s role in shaping social media decisions. Hasan suggested that Taibbi had willfully conflated CISA with CIS during his testimony. This claim led Representative Stacey Plaskett (D-V.I) to accuse Taibbi of perjury in a letter.
The CIS report I obtained contradicts Hasan and Plaskett, clarifying that “CIS and CISA worked together to ensure the reports were sent to the social media platform within an hour of their receipt.” CIS also played a pivotal role in triaging the material while maintaining the government partnership with disinformation research think tanks.
In essence, CIS and CISA worked in close collaboration to exert pressure on platforms like Twitter, aiming to remove conservative political expression deemed untrustworthy. The project was a public-private venture, overseen by government agencies, and supported by a system financed entirely by a Democratic donor.
The report makes recommendations for future elections. It notes that misinformation reporting may require dedicated government funding, with a “transition to the operational side of CIS” under the CISA umbrella, as well as better operational support from social media platforms.
The CIS report is part of a batch of documents recently received from Kate Starbird, an advisory board member of CISA at the University of Washington, via a records request. As I reported on Tuesday, the Justice Department intervened last year to impede the release of records from Starbird’s team. Starbird has also accused journalists seeking these records of “harassment,” likening it to a cyber attack.
Nevertheless, these inquiries are part of a broader public examination of government-backed censorship. As previously reported, Starbird’s advisory panel advocated for an expanded role for CISA, calling for an extension of its monitoring to include various platforms such as social media, mainstream media, cable news, hyper-partisan media, talk radio, and other online resources.
To support their argument for such a broad mandate, CISA advisors highlighted the detrimental effects of alleged misinformation on key democratic institutions like the courts, as well as other sectors such as the financial system and public health measures, suggesting that virtually any major public interest concern may be used as justification for broad censorship.
Biden Regime Unveils Historic Plan to Crush Criticism of Influential Jews

By Eric Striker | National Justice Party | May 25, 2023
Yesterday, President Joe Biden announced a plan to use virtually every branch of the federal government, big business and civil society to ruthlessly suppress First Amendment protected criticism of Jewish political power and Zionism in the homeland.
The 60-page document, titled the “US National Strategy To Combat Anti-Semitism,” was created in part by Doug Emhoff, the Jewish husband of Vice President Kamala Harris. The goal of the project is to consolidate every power at Washington’s fingertips to engage in a political campaign to quell the American people’s rising awareness of the radically disproportionate influence Jewish people wield over the country.
On the law enforcement front, Washington appears to be de-emphasizing the FBI, which has suffered several reputational blows that have discredited its campaign against “white supremacy,” while continuing to expand the power of the Department of Homeland Security (DHS) — originally founded after 9/11 to combat Al Qaeda — in its place.
The DHS is being directed to to produce research equating concern with how Jews use political and financial power with acts of violence, host more regular workshops for all branches of law enforcement on using the law to persecute those engaging in “anti-Semitism,” increase security resources earmarked for Jewish institutions, give Jewish organizations more say over how intelligence and police resources are directed, and instruct private social media and internet companies to find and eliminate “anti-Semitic” content from their platforms.
The document, without qualification, is marbled with an egregious lack of respect for fundamental civil liberties. In one instance, there is an executive command to the Department of Treasury to convene a forum of Money Services Businesses (MSB) institutions, along with those outside of the network, to prevent online crowdfunding for what it labels “hate groups.” What constitutes a hate group — a term that is alien under traditional American jurisprudence — is not specifically defined. The project promises to reach all nations in the trans-national American sphere of influence.
The White House is also ushering in a myriad of new programs seeking to indoctrinate students on the Holocaust story and the numerous ways one could be practicing “anti-Semitism,” largely but not exclusively through the Department of Education. The Biden administration plan also expands the footprint of the US Holocaust Memorial Museum (USHMM).
No agency will be immune to this politicization. The Department of Labor (DOL) will be pressuring labor unions to identify “anti-Semites” in their midst, while the US Department of Agriculture (USDA) will be expanding access to Jews engaging in the controversial practice of Kosher slaughter. USDA will also be approaching rural religious leaders and universities to impose Washington’s strategy in even the most remote small towns.
Under this plan, the National Endowment of the Arts (NEA) is given the deadline of September 2023 to create political propaganda projects that “incorporate themes of countering antisemitism and other forms of hate in their artistic practice.”
The Department of the Interior (DOI), The Small Business Administration (SBA), and even the Institute of Museum and Library Services (IMLS) will all be given special tasks to train small business owners, park rangers, and guides in identifying and fighting “anti-Semitism.” Special attention is being given to rural libraries, which Washington will be transforming into outlets for promoting pro-Jewish narratives.
So far, only Representative Lauren Boebert has publicly come out against this runaway weaponization of the federal government. Jewish groups backing Ron DeSantis and Donald Trump have also criticized the move, but their concern is that it does not go far enough in targeting critics of the state of Israel.
The implementation of this plan coincides with the beginning of Biden’s 2024 re-election campaign. A massively lopsided percentage of the president’s major donors are Jewish, and his administration is one of the most heavily Jewish in US history.
