Bari Weiss’ New CBS Hire List Is Full Of Zionists
Zionist Installed Editor of CBS News Has Hired A Long Line Of Hardline Contributors
The Dissident | January 27, 2026
CBS News, under the editorial control of hardline Zionist Bari Weiss, has added 19 new contributors to the network, many of whom- unsurprisingly-are hardline Zionists denying the Gaza genocide and pushing for war with Iran.
In this article, I will go over some of the most egregious new hires.
Elliot Ackerman
The first hire announced at CBS News is Elliot Ackerman, a veteran of the Marine Corps and CIA special operations who is now a fiction and non fiction author.
Like most of the new contributors, he is a hardline Zionist.
On X, he has gone after the New York Times of all outlets for not being subservient enough to the Israeli propaganda line on Iran.
In response to a New York Times article with a subhead that read, “Iran says Israel wants to trap it to a direct conflict by bombing Hezbollah, even as a new Iranian president tries outreach to the West”, Ackerman wrote, “Poor Iran … all it wants is peace.”
He also took issue with the fact that the New York Times wrote, “Iran has so far refused to be goaded by Israel into a larger regional war” responding by saying, “‘Goaded by Israel …’ this is insane.”
He is also an advocate of the U.S. backing Israel and fighting wars in the Middle East on its behalf.
In the Atlantic, he wrote , “ in the name of ‘ending America’s forever wars,’ our leaders have proved reluctant to call enemies ‘enemies’ and friends ‘friends.’ If America wishes to remain at peace, or at least not find itself in an active war, we must speak clearly in defense of our friends. This remains uniquely true in the case of Israel.”
In the article, he called on America to support Israel’s war in Lebanon, writing:
Israel has recently dealt Hezbollah a series of crippling blows, beginning with exploding pagers and radios that sabotaged Hezbollah’s command and control and degraded its leadership. This has culminated with the strike against Nasrallah. Hezbollah has been forced onto its back foot, as has the Iranian regime. This creates an opening, one that Israel will likely exploit and that the United States, Israel’s ally, must support, lest we squander a precious opportunity in this broader war.
The United States can’t afford to make the same mistake with Israel. Now is the time to stand decisively behind our ally and against Hamas, Hezbollah, Iran, Russia, China, and the axis of authoritarian nations that continue to menace the liberal world.
Masih Alinejad
Another contributor announced to CBS News is Masih Alinejad, an Iranian journalist in exile and U.S. government asset pushing for war with Iran.
As journalist Asa Winstanley reported , Masih Alinejad “is an employee of the Voice of America Persian, a US government-funded media outlet”, which the New York Times called a “Worldwide Propaganda Network Built by the C.I.A”.
Furthermore, as Winstanley noted, “Predictability, as an enemy of a government that has steadfastly supported Palestinian resistance since 1979, Alinejad is also rabidly pro-Israel. In June she gave a talk for an Israel lobby group in the US, calling for a future ‘democratic’ Iran to normalise relations with Israel.”
He added that, “Government documents show that Alinejad has been the recipient of more than $628,000 in US federal funding since 2015.”
A state department cable from 2009, when Masih Alinejad was still in Iran, indentified her as a U.S. intel asset.
As a U.S. asset, Masih Alinejad openly supports a U.S. regime change war in Iran, undoubtedly the reason behind her being hired as a contributor at CBS News.
Niall Ferguson
The most egregious contributor added to CBS News is the British Neo-con Niall Ferguson, who described himself as “a fully paid-up member of the neo-imperialist gang” during the Iraq war.
Ferguson denied the fact that Israel committed genocide in Gaza, quoting the Israeli propagandist John Spencer’s genocide denial, and claiming that he is an authority because he has “embedded with the IDF” and “interviewed the prime minister, the defence minister, the chief of staff, the Southern Command leadership”.
Niall Ferguson also supports a U.S. war on Iran for Israel, saying that “The U.S. Should Finish the Job in Iran”.
Ferguson is also a contributor to Bari Weiss’ “The Free Press”, where he once wrote an article alongside Yoav Gallant, the former Minister of Defence of Israel who is indicted by the ICC on war crimes charges where they pushed for a U.S. war on Iran, writing, “Israel has moved and continues to move with determination and dispatch. The support of allies, first and foremost the United States, has been crucial. Now, with a single exertion of its unmatched military strength, the United States can shorten the war, prevent wider escalation, and end the principal threat to Middle Eastern stability. It can also send a signal to those other authoritarian powers who have been Iran’s enablers that American deterrence is back. This is a rare moment when strategic alignment and operational momentum converge. It must not be missed.”
Coleman Hughes
Coleman Hughes, one of Bari Weiss’s propagandists at the Free Press, has now been brought over to CBS News.
On the payroll of Weiss, Coleman Hughes has written genocide denial columns, denying Israel’s well-documented atrocities in Gaza.
In an article for the Free Press, Hughes claimed that “when an IDF soldier goes berserk, he is subject to criminal punishment”, despite the fact that multiple IDF soldiers have said that “You can do almost whatever you want when it comes to Gazans, honestly, I think that is how Israeli society has been dehumanizing Palestinians for years” and “This thing called killing innocent people – it’s been normalized” and despite the fact that, “88% of Israeli Military Investigations Into Gaza War Crimes Stalled or Closed Without Findings”.
HR McMaster
Another contributor added to CBS News is HR McMaster, the U.S. General who served as the United States National Security Advisor from 2017 to 2018 and now serves as a senior fellow at the neo-con Hoover Institution.
McMaster is a hardline Zionist, saying in 2024 that “the U.S. needs to offer stronger backing to Israel and stop pushing for what he described as premature and foolhardy ceasefire agreements”.
HR McMaster is also a strong proponent of war with Iran for Israel, saying in 2018 when he was National Security Advisor, “What’s particularly concerning is that this network of proxies is becoming more and more capable, as Iran seeds more and more… destructive weapons into these networks, So the time is now, we think, to act against Iran”.
In a 2024 article for Bari Weiss’ propaganda blog, the Free Press, McMaster hoped that Trump would go to war with Iran during his new term, saying, “We have a sense of how Trump will respond to Iranian aggression. He frequently told me ‘everywhere I see problems [in the Middle East] there is Iran.’ He knows what the return address is for the violence not only against Israel but also in Syria, Iraq, and Yemen. He is certain to ramp up sanctions enforcement against Tehran to limit the resources available for Iran’s proxy militias and terrorist organizations.”
He cheered on the U.S/Israeli bombing of Iran in June of last year writing, “But even more importantly, the Israeli and U.S. military operations directly against the Islamic Republic and its warmaking apparatus reminded officials in Tehran that they cannot antagonize their adversaries in the region with impunity—and reminded officials in Washington that Iran’s theocratic dictatorship cannot be conciliated. “De-escalation” was never a path to peace—it was an approach that perpetuated war on the Iranians’ terms.”
Reihan Salam
Another new contributor to CBS News is Reihan Salam, the president of the Neo-con Manhattan Institute who wrote in the Wall Street Journal at the start of the genocide in Gaza, “Muslim Americans Like Me Stand With Israel” adding, “In short, Muslim Americans who stand with Israel and the Jewish people in their struggle for survival do exist—as convenient as it might be for self-described progressive humanitarians to pretend otherwise.”
Glenn Loury, a former contributor to the Manhattan Institute, revealed that he was fired by Reihan Salam who told him in an email they have a “lack of shared priorities” after “the Manhattan Institute first signaled their dismay with my position on Gaza after I posted my conversation with Israeli historian Omer Bartov” who accurately stated that Israel was committing genocide in Gaza.
Bari Weiss’s Goal
Bari Weiss’s goal with the new CBS contributors is clear- to hire Zionists pushing for American backing of Israel and an American war with Iran for Israel, in order to use the once respected news outlet to manufacture consent for Israel’s foreign policy goals.
How much is shoddy, pro-Israel journalism worth? Ask Bari Weiss.
As her Free Press is poised to seal a $200 million deal with the mainstream news giant CBS, let us reflect on why
By Branko Marcetic | Responsible Statecraft | July 29, 2025
A thought experiment: would anyone who referred to the killing of 50 Jewish people, many of them “entirely innocent non-combatants, including children,” as “one of the unavoidable burdens of political power, of Palestinian liberation’s dream turned into the reality of self-determination,” ever be hired by a major television news network?
Would their news outlet ever be potentially offered more than $200 million to merge with that major news network?
Of course not, and for good reason. Yet that’s exactly what’s happening, only with one small but major difference: the writer and her news outlet responsible for this statement, Bari Weiss and The Free Press, were not talking about Hamas’ murder of Israelis, but rather about Israel’s killing of 50 Palestinians — “Zionism’s dream turned into the reality of self-determination,” as Weiss described it in 2021.
Weiss is currently in talks to sell The Free Press to CBS News for between $200-$250 million, after reportedly winning over its new owner, David Ellison, “by taking a pro-Israel stance,” according to the Financial Times. Ellison “wants to position The Free Press alongside CBS News,” the paper reported, while another source told the New York Times that Ellison is weighing up giving Weiss “an influential role in shaping the editorial sensibilities of CBS News.”
If so, it would be a major new development in a pervasive double standard we’ve seen in the past nearly two years. Weiss and her outlet have engaged in rhetoric and professional behavior that would ordinarily never pass muster in a newsroom — but are considered acceptable because they are in support of Israel’s war against Palestinians.
For one, The Free Press has repeatedly spread misinformation. In May 2024, the outlet charged that the UN had “admit” the civilian death toll was 50 percent lower than what was being claimed, a quickly debunked and borderline willful misreading of a UN document, a misreading that the UN secretary-general’s office swiftly came forward to correct (a fact left out of The Free Press’ piece).
One year later, The Free Press declared the idea that Israel was engineering a man-made famine that was underway in Gaza a “myth,” even as Israel was in its third month of blocking all food, fuel, and medicine into the territory and at least 57 civilians had already starved to death, most of them children. As recently as this past Sunday, another Free Press article argued that “there isn’t mass starvation as claimed by pro-Hamas propaganda,” which flies in the face of not just basic reality, but testimony from doctors, major news organizations with journalists on the ground, and even the conclusion of President Donald Trump, a supporter of the war.
Just this past June, The Free Press charged simultaneously that there had both been no massacre of Palestinian aid seekers, and that, if there was, Hamas may have been responsible. Of course, since then, not only have Israeli soldiers admitted to shooting aid-seekers but U.S. contractors are coming forward to back up their gruesome stories. These accounts are becoming a near-daily occurrence, with over 1,000 Gazans killed at or close to aid distribution sites in the past two months.
In late May, The Free Press even published a puff piece on the group running these virtual slaughterhouses, the Gaza Humanitarian Foundation (GHF), painting it as an unsung success story, despite ample controversy at the time over its reliance on mercenaries and lack of independence. Two months of bloodshed later, condemnation and calls for GHF’s dismantling are widespread, with one former GHF staffer — a retired U.S. special forces officer — saying he had never witnessed such brutality and indiscriminate violence against “an unarmed, starving population” as at GHF’s distribution centers.
All of these pieces are still up, uncorrected on The Free Press website. And this is by no means an exhaustive list.
When it’s not spreading outright misinformation, The Free Press engages in more insidious propaganda. For instance, it has, depending on the public relations needs of the moment, shifted between ignoring, indignantly denying, and justifying Israel’s attacks on Gaza’s hospitals.
When a blast in the war’s first month that killed hundreds at al-Ahli Hospital ignited global outrage, The Free Press jumped on evidence that it may have been an errant Hamas rocket to charge again and again and again, even as recently as two days ago, that the media were rampantly defaming Israel through fake news of crimes it had never committed.
Since then, The Free Press has simply ignored the Israeli attacks on hospitals, often openly done and fully admitted to by the IDF, that have left 94 percent of hospitals in Gaza damaged or destroyed, including just this year attacking al-Ahli at least twice. In fact, both the outlet and Weiss personally pivoted quickly from denying Israel would do such a terrible thing to actively justifying its targeting of hospitals.
Of course, the vast majority of Israel’s war crimes in Gaza are simply never discussed by the outlet. The same goes for Palestinian suffering more generally and the massive and ever-mounting Palestinian death toll, which a group of experts last year concluded is likely undercounted by hundreds of thousands. Typically, the only time these topics are discussed by the outlet is to deny them and to lament their negative effect on Israel.
This is hardly surprising, considering new revelations that The Free Press has serially regurgitated content pushed by the Center for Peace Communications — an organization staffed by figures from pro-Israel think tanks and funded by money from pro-Israel donors.
Another largely absent topic: antisemitism, which is a charge The Free Press exclusively reserves for antiwar protesters, college campuses, teachers unions, Peter Beinart, Ireland, and anyone else who expresses pro-Palestinian sentiment, while it dutifully ignores accusations of antisemitism among Trump appointees and nominees and allies who also happen to be supporters of Israel’s war.
That brings us to the conduct of Weiss herself. She has a personal history of both playing fast and loose with the truth and what can only be described as a high degree of tolerance for anti-Arab and Islamophobic bigotry.
Weiss first rose to prominence due to her efforts to get Muslim and Arab professors at Columbia University fired by accusing them of racism, only for the resulting investigation to find “no evidence of any statements made by the faculty that could reasonably be construed as anti-Semitic.” She then later misleadingly claimed she had never tried to get them fired.
The supposedly rabid bigotry of ordinary Muslims is a favorite topic of Weiss, who has previously blamed rising antisemitism in Europe on the Muslim presence there, and warned that European Jews have “reason to worry” because of it. Soon after October 7, she approvingly shared a Free Press article whose central argument was that protests against Israel’s war — dishonestly characterized as hateful antisemitic rallies “celebrat[ing] mass murder in the streets” — were thanks to immigrants from Middle Eastern countries who could be either “80-year-old Armenian retirees or jihadi terrorists plotting another 9/11.” The Free Press later published an error-riddled article explicitly blaming a surge in Canadian antisemitism on Muslim immigration.
At the same time, Weiss has often promoted, often through The Free Press, her “friend” Ayaan Hirsi Ali. Hirsi Ali believes that “we are at war with Islam,” which she has called “a destructive, nihilistic cult of death,” that “there is no moderate Islam,” and that it must be “defeated” and “crush[ed],” including by closing all Muslim schools.
Ali has been a favorite of Islamphobic think tanks and neoconservative activists since the Global War on Terror. She has written that “every devout Muslim” at the very least “approved” of Al Qaeda’s 9/11 attacks and wrote a book that argued that Muslim immigration threatens the rights of Western women, partly because of Muslim men’s supposedly rapacious appetite for sexual violence.
Weiss eagerly promoted that book, spending an hour teeing Hirsi Ali up in a question and answer session to hold forth unchallenged about the dangers of ordinary Muslim men. Elsewhere, Weiss has waxed lyrical about her pride in associating with Hirsi Ali, and that she regards someone’s support for her as a “litmus test.”
If Weiss expressed or promoted any of these same views about Jewish immigrants and Judaism, she would likely be blacklisted in U.S. media, and for good reason. Instead, because they are aimed at Muslims, she is now being richly rewarded.
That a major network like CBS is seriously considering giving Weiss and The Free Press an even bigger platform and the imprimatur of mainstream legitimacy — given not just its promotion of anti-Muslim views, but its history of spreading outright, uncorrected falsehoods — is a sad reflection of the degradation of press standards.
And it seems to only be happening because a top media executive regards Weiss’ history of shoddy journalism less important than her support for Israel’s wars.
Sorry, CBS, NOAA’s “U.S. Climate Normals,” Report Misrepresents the Science
By H. Sterling Burnett | ClimateRealism | May 7, 2021
CBS News’ story covering of the Biden administration’s new U.S Climate Normals report says government data show the United States is warming at an unusually rapid rate due to human induced climate change, causing more frequent and severe extreme weather events. This story, as with the government report it is based upon, is long on alarm but short on facts. Data from the U.N. Intergovernmental Panel on Climate Change and the U.S. National Oceanic and Atmospheric Administration (NOAA) show temperatures in the United States aren’t rising at an unusually rapid rate. In addition, incidences of extreme weather events are neither more frequent nor more severe than in the past.
“Just a quick glance at the new U.S. Climate Normals maps published by the National Oceanic and Atmospheric Administration (NOAA) on Tuesday is enough for most climate scientists to say, ‘I told you so,’” writes CBS in an article, titled “NOAA’s “new normal” climate report is anything but normal.”
“While the new normals are just 10 years removed from the earlier set, the changes are still significant. In that time the nation has warmed an average of half a degree Fahrenheit,” CBS continues. “That may not sound like much, but small changes in the normals mean much larger changes in the extremes like extremes like heat waves, droughts, wildfires, floods and hurricanes.”
NOAA’s new report may claim temperatures are rising across the United States, and weather is getting more extreme, but its own data and data from the IPCC say otherwise.
As discussed in Climate at a Glance: Temperatures, contrary to NOAA’s claim that temperatures are rising rapidly, thermometer readings in the United States report current temperatures are similar to the temperatures recorded 80 years ago. Also, NOAA’s own U.S. Climate Reference Network, an extremely accurate network of temperature stations throughout the United States requiring no corrective adjustments, shows no significant warming has occurred in the United States since it was established in 2005.
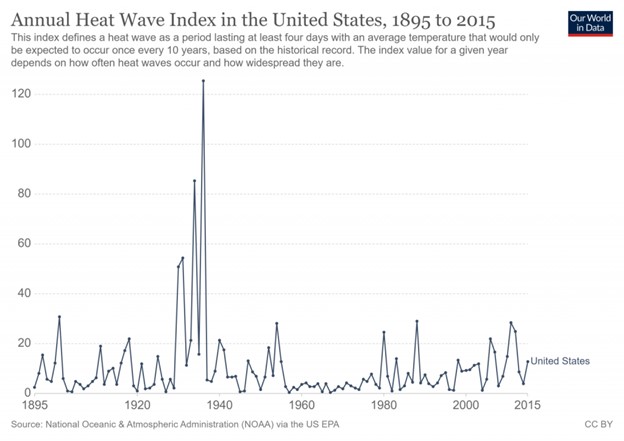
Data from the IPCC and NOAA also demonstrate there has been no measurable increase in the number or severity of droughts, hurricanes or floods, since the early part of the 19th century. Also, data from the IPCC and NOAA show the incidences of heatwaves [see the figure below] and wildfires in the United States and globally have actually declined during the recent period of modest warming.
Had CBS compared the publicly available data against the alarming soundbites contained in the Biden administration’s new U.S. Climate Normals report, it could have easily discovered the report misrepresents what data show. A news organization committed to pursuing the truth, wherever it leads, would have looked beneath the surface of the report at the underlying data. Such an investigation would have revealed temperatures aren’t rising unnaturally, and weather extremes aren’t increasing.
That’s the good news CBS should have reported.
H. Sterling Burnett, Ph.D. is managing editor of Environment & Climate News and a research fellow for environment and energy policy at The Heartland Institute. Burnett worked at the National Center for Policy Analysis for 18 years, most recently as a senior fellow in charge of NCPA’s environmental policy program. He has held various positions in professional and public policy organizations, including serving as a member of the Environment and Natural Resources Task Force in the Texas Comptroller’s e-Texas commission.
How the Department of Homeland Security Created a Deceptive Tale of Russia Hacking US Voter Sites
By Gareth Porter | Consortium News | August 28, 2018
The narrative of Russian intelligence attacking state and local election boards and threatening the integrity of U.S. elections has achieved near-universal acceptance by media and political elites. And now it has been accepted by the Trump administration’s intelligence chief, Dan Coats, as well.
But the real story behind that narrative, recounted here for the first time, reveals that the Department of Homeland Security (DHS) created and nurtured an account that was grossly and deliberately deceptive.
DHS compiled an intelligence report suggesting hackers linked to the Russian government could have targeted voter-related websites in many states and then leaked a sensational story of Russian attacks on those sites without the qualifications that would have revealed a different story. When state election officials began asking questions, they discovered that the DHS claims were false and, in at least one case, laughable.
The National Security Agency and special counsel Robert Mueller’s investigating team have also claimed evidence that Russian military intelligence was behind election infrastructure hacking, but on closer examination, those claims turn out to be speculative and misleading as well. Mueller’s indictment of 12 GRU military intelligence officers does not cite any violations of U.S. election laws though it claims Russia interfered with the 2016 election.
A Sensational Story
On Sept. 29, 2016, a few weeks after the hacking of election-related websites in Illinois and Arizona, ABC News carried a sensational headline: “Russian Hackers Targeted Nearly Half of States’ Voter Registration Systems, Successfully Infiltrated 4.” The story itself reported that “more than 20 state election systems” had been hacked, and four states had been “breached” by hackers suspected of working for the Russian government. The story cited only sources “knowledgeable” about the matter, indicating that those who were pushing the story were eager to hide the institutional origins of the information.
Behind that sensational story was a federal agency seeking to establish its leadership within the national security state apparatus on cybersecurity, despite its limited resources for such responsibility. In late summer and fall 2016, the Department of Homeland Security was maneuvering politically to designate state and local voter registration databases and voting systems as “critical infrastructure.” Such a designation would make voter-related networks and websites under the protection a “priority sub-sector” in the DHS “National Infrastructure Protection Plan, which already included 16 such sub-sectors.
DHS Secretary Jeh Johnson and other senior DHS officials consulted with many state election officials in the hope of getting their approval for such a designation. Meanwhile, the DHS was finishing an intelligence report that would both highlight the Russian threat to U.S. election infrastructure and the role DHS could play in protecting it, thus creating political impetus to the designation. But several secretaries of state—the officials in charge of the election infrastructure in their state—strongly opposed the designation that Johnson wanted.
On Jan. 6, 2017—the same day three intelligence agencies released a joint “assessment” on Russian interference in the election—Johnson announced the designation anyway.
Media stories continued to reflect the official assumption that cyber attacks on state election websites were Russian-sponsored. Stunningly, The Wall Street Journal reported in December 2016 that DHS was itself behind hacking attempts of Georgia’s election database.
The facts surrounding the two actual breaches of state websites in Illinois and Arizona, as well as the broader context of cyberattacks on state websites, didn’t support that premise at all.
In July, Illinois discovered an intrusion into its voter registration website and the theft of personal information on as many as 200,000 registered voters. (The 2018 Mueller indictments of GRU officers would unaccountably put the figure at 500,000.) Significantly, however, the hackers only had copied the information and had left it unchanged in the database.
That was a crucial clue to the motive behind the hack. DHS Assistant Secretary for Cyber Security and Communications Andy Ozment told a Congressional committee in late September 2016 that the fact hackers hadn’t tampered with the voter data indicated that the aim of the theft was not to influence the electoral process. Instead, it was “possibly for the purpose of selling personal information.” Ozment was contradicting the line that already was being taken on the Illinois and Arizona hacks by the National Protection and Programs Directorate and other senior DHS officials.
In an interview with me last year, Ken Menzel, the legal adviser to the Illinois secretary of state, confirmed what Ozment had testified. “Hackers have been trying constantly to get into it since 2006,” Menzel said, adding that they had been probing every other official Illinois database with such personal data for vulnerabilities as well. “Every governmental database—driver’s licenses, health care, you name it—has people trying to get into it,” said Menzel.
In the other successful cyberattack on an electoral website, hackers had acquired the username and password for the voter database Arizona used during the summer, as Arizona Secretary of State Michele Reagan learned from the FBI. But the reason that it had become known, according to Reagan in an interview with Mother Jones, was that the login and password had shown up for sale on the dark web—the network of websites used by cyber criminals to sell stolen data and other illicit wares.
Furthermore, the FBI had told her that the effort to penetrate the database was the work of a “known hacker” whom the FBI had monitored “frequently” in the past. Thus, there were reasons to believe that both Illinois and Arizona hacking incidents were linked to criminal hackers seeking information they could sell for profit.
Meanwhile, the FBI was unable to come up with any theory about what Russia might have intended to do with voter registration data such as what was taken in the Illinois hack. When FBI Counterintelligence official Bill Priestap was asked in a June 2017 hearing how Moscow might use such data, his answer revealed that he had no clue: “They took the data to understand what it consisted of,” said the struggling Priestap, “so they can affect better understanding and plan accordingly in regards to possibly impacting future elections by knowing what is there and studying it.”
The inability to think of any plausible way for the Russian government to use such data explains why DHS and the intelligence community adopted the argument, as senior DHS officials Samuel Liles and Jeanette Manfra put it, that the hacks “could be intended or used to undermine public confidence in electoral processes and potentially the outcome.” But such a strategy could not have had any effect without a decision by DHS and the U.S. intelligence community to assert publicly that the intrusions and other scanning and probing were Russian operations, despite the absence of hard evidence. So DHS and other agencies were consciously sowing public doubts about U.S. elections that they were attributing to Russia.
DHS Reveals Its Self-Serving Methodology
In June 2017, Liles and Manfra testified to the Senate Intelligence Committee that an October 2016 DHS intelligence report had listed election systems in 21 states that were “potentially targeted by Russian government cyber actors.” They revealed that the sensational story leaked to the press in late September 2016 had been based on a draft of the DHS report. And more importantly, their use of the phrase “potentially targeted” showed that they were arguing only that the cyber incidents it listed were possible indications of a Russian attack on election infrastructure.
Furthermore, Liles and Manfra said the DHS report had “catalogued suspicious activity we observed on state government networks across the country,” which had been “largely based on suspected malicious tactics and infrastructure.” They were referring to a list of eight IP addresses an August 2016 FBI “flash alert” had obtained from the Illinois and Arizona intrusions, which DHS and FBI had not been able to attribute to the Russian government.

Manfra: No doubt it was the Russians. (C-SPAN)
The DHS officials recalled that the DHS began to “receive reports of cyber-enabled scanning and probing of election-related infrastructure in some states, some of which appeared to originate from servers operated by a Russian company.” Six of the eight IP addresses in the FBI alert were indeed traced to King Servers, owned by a young Russian living in Siberia. But as DHS cyber specialists knew well, the country of ownership of the server doesn’t prove anything about who was responsible for hacking: As cybersecurity expert Jeffrey Carr pointed out, the Russian hackers who coordinated the Russian attack on Georgian government websites in 2008 used a Texas-based company as the hosting provider.
The cybersecurity firm ThreatConnect noted in 2016 that one of the other two IP addresses had hosted a Russian criminal market for five months in 2015. But that was not a serious indicator, either. Private IP addresses are reassigned frequently by server companies, so there is not a necessary connection between users of the same IP address at different times.
The DHS methodology of selecting reports of cyber incidents involving election-related websites as “potentially targeted” by Russian government-sponsored hackers was based on no objective evidence whatever. The resulting list appears to have included any one of the eight addresses as well as any attack or “scan” on a public website that could be linked in any way to elections.
This methodology conveniently ignored the fact that criminal hackers were constantly trying to get access to every database in those same state, country and municipal systems. Not only for Illinois and Arizona officials, but state electoral officials.
In fact, 14 of the 21 states on the list experienced nothing more than the routine scanning that occurs every day, according to the Senate Intelligence Committee. Only six involved what was referred to as a “malicious access attempt,” meaning an effort to penetrate the site. One of them was in Ohio, where the attempt to find a weakness lasted less than a second and was considered by DHS’s internet security contractor a “non-event” at the time.
State Officials Force DHS to Tell the Truth
For a year, DHS did not inform the 21 states on its list that their election boards or other election-related sites had been attacked in a presumed Russian-sponsored operation. The excuse DHS officials cited was that it could not reveal such sensitive intelligence to state officials without security clearances. But the reluctance to reveal the details about each case was certainly related to the reasonable expectation that states would publicly challenge their claims, creating a potential serious embarrassment.
On Sept. 22, 2017, DHS notified 21 states about the cyber incidents that had been included in the October 2016 report. The public announcement of the notifications said DHS had notified each chief election officer of “any potential targeting we were aware of in their state leading up to the 2016 election.” The phrase “potential targeting” again telegraphed the broad and vague criterion DHS had adopted, but it was ignored in media stories.
But the notifications, which took the form of phone calls lasting only a few minutes, provided a minimum of information and failed to convey the significant qualification that DHS was only suggesting targeting as a possibility. “It was a couple of guys from DHS reading from a script,” recalled one state election official who asked not to be identified. “They said [our state] was targeted by Russian government cyber actors.”
A number of state election officials recognized that this information conflicted with what they knew. And if they complained, they got a more accurate picture from DHS. After Wisconsin Secretary of State Michael Haas demanded further clarification, he got an email response from a DHS official with a different account. “[B]ased on our external analysis,” the official wrote, “the WI [Wisconsin] IP address affected belongs to the WI Department of Workforce Development, not the Elections Commission.”
California Secretary of State Alex Padilla said DHS initially had notified his office “that Russian cyber actors ‘scanned’ California’s Internet-facing systems in 2016, including Secretary of State websites.” But under further questioning, DHS admitted to Padilla that what the hackers had targeted was the California Department of Technology’s network.
Texas Secretary of State Rolando Pablos and Oklahoma Election Board spokesman Byron Dean also denied that any state website with voter- or election-related information had been targeted, and Pablos demanded that DHS “correct its erroneous notification.”
Despite these embarrassing admissions, a statement issued by DHS spokesman Scott McConnell on Sept. 28, 2017 said the DHS “stood by” its assessment that 21 states “were the target of Russian government cyber actors seeking vulnerabilities and access to U.S. election infrastructure.” The statement retreated from the previous admission that the notifications involved “potential targeting,” but it also revealed for the first time that DHS had defined “targeting” very broadly indeed.
It said the category included “some cases” involving “direct scanning of targeted systems” but also cases in which “malicious actors scanned for vulnerabilities in networks that may be connected to those systems or have similar characteristics in order to gain information about how to later penetrate their target.”
It is true that hackers may scan one website in the hope of learning something that could be useful for penetrating another website, as cybersecurity expert Prof. Herbert S. Lin of Stanford University explained to me in an interview. But including any incident in which that motive was theoretical meant that any state website could be included on the DHS list, without any evidence it was related to a political motive.
Arizona’s further exchanges with DHS revealed just how far DHS had gone in exploiting that escape clause in order to add more states to its “targeted” list. Arizona Secretary of State Michele Reagan tweeted that DHS had informed her that “the Russian government targeted our voter registration systems in 2016.” After meeting with DHS officials in early October 2017, however, Reagan wrote in a blog post that DHS “could not confirm that any attempted Russian government hack occurred whatsoever to any election-related system in Arizona, much less the statewide voter registration database.”
What the DHS said in that meeting, as Reagan’s spokesman Matt Roberts recounted to me, is even more shocking. “When we pressed DHS on what exactly was actually targeted, they said it was the Phoenix public library’s computers system,” Roberts recalled.
In April 2018, a CBS News “60 Minutes” segment reported that the October 2016 DHS intelligence report had included the Russian government hacking of a “county database in Arizona.” Responding to that CBS report, an unidentified “senior Trump administration official” who was well-briefed on the DHS report told Reuters that “media reports” on the issue had sometimes “conflated criminal hacking with Russian government activity,” and that the cyberattack on the target in Arizona “was not perpetrated by the Russian government.”
NSA Finds a GRU Election Plot

National Security Agency headquarters in Fort Meade, Md. (Wikimedia)
NSA intelligence analysts claimed in a May 2017 analysis to have documented an effort by Russian military intelligence (GRU) to hack into U.S. electoral institutions. In an intelligence analysis obtained by The Intercept and reported in June 2017, NSA analysts wrote that the GRU had sent a spear-phishing email—one with an attachment designed to look exactly like one from a trusted institution but that contains malware design to get control of the computer—to a vendor of voting machine technology in Florida. The hackers then designed a fake web page that looked like that of the vendor. They sent it to a list of 122 email addresses NSA believed to be local government organizations that probably were “involved in the management of voter registration systems.” The objective of the new spear-phishing campaign, the NSA suggested, was to get control of their computers through malware to carry out the exfiltration of voter-related data.
But the authors of The Intercept story failed to notice crucial details in the NSA report that should have tipped them off that the attribution of the spear-phishing campaign to the GRU was based merely on the analysts’ own judgment—and that their judgment was faulty.
The Intercept article included a color-coded chart from the original NSA report that provides crucial information missing from the text of the NSA analysis itself as well as The Intercept’s account. The chart clearly distinguishes between the elements of the NSA’s account of the alleged Russian scheme that were based on “Confirmed Information” (shown in green) and those that were based on “Analyst Judgment” (shown in yellow). The connection between the “operator” of the spear-phishing campaign the report describes and an unidentified entity confirmed to be under the authority of the GRU is shown as a yellow line, meaning that it is based on “Analyst Judgment” and labeled “probably.”
A major criterion for any attribution of a hacking incident is whether there are strong similarities to previous hacks identified with a specific actor. But the chart concedes that “several characteristics” of the campaign depicted in the report distinguish it from “another major GRU spear-phishing program,” the identity of which has been redacted from the report.
The NSA chart refers to evidence that the same operator also had launched spear-phishing campaigns on other web-based mail applications, including the Russian company “Mail.ru.” Those targets suggest that the actors were more likely Russian criminal hackers rather than Russian military intelligence.
Even more damaging to its case, the NSA reports that the same operator who had sent the spear-phishing emails also had sent a test email to the “American Samoa Election Office.” Criminal hackers could have been interested in personal information from the database associated with that office. But the idea that Russian military intelligence was planning to hack the voter rolls in American Samoa, an unincorporated U.S. territory with 56,000 inhabitants who can’t even vote in U.S. presidential elections, is plainly risible.
The Mueller Indictment’s Sleight of Hand
The Mueller indictment of GRU officers released on July 13 appeared at first reading to offer new evidence of Russian government responsibility for the hacking of Illinois and other state voter-related websites. A close analysis of the relevant paragraphs, however, confirms the lack of any real intelligence supporting that claim.
Mueller accused two GRU officers of working with unidentified “co-conspirators” on those hacks. But the only alleged evidence linking the GRU to the operators in the hacking incidents is the claim that a GRU official named Anatoly Kovalev and “co-conspirators” deleted search history related to the preparation for the hack after the FBI issued its alert on the hacking identifying the IP address associated with it in August 2016.
A careful reading of the relevant paragraphs shows that the claim is spurious. The first sentence in Paragraph 71 says that both Kovalev and his “co-conspirators” researched domains used by U.S. state boards of elections and other entities “for website vulnerabilities.” The second says Kovalev and “co-conspirators” had searched for “state political party email addresses, including filtered queries for email addresses listed on state Republican Party websites.”

Mueller: Don’t read the fine print. (The White House/Wikimedia)
Searching for website vulnerabilities would be evidence of intent to hack them, of course, but searching Republican Party websites for email addresses is hardly evidence of any hacking plan. And Paragraph 74 states that Kovalev “deleted his search history”—not the search histories of any “co-conspirator”—thus revealing that there were no joint searches and suggesting that the subject Kovalev had searched was Republican Party emails. So any deletion by Kovalev of his search history after the FBI alert would not be evidence of his involvement in the hacking of the Illinois election board website.
With this rhetorical misdirection unraveled, it becomes clear that the repetition in every paragraph of the section of the phrase “Kovalev and his co-conspirators” was aimed at giving the reader the impression the accusation is based on hard intelligence about possible collusion that doesn’t exist.
The Need for Critical Scrutiny of DHS Cyberattack Claims
The DHS campaign to establish its role as the protector of U.S. electoral institutions is not the only case in which that agency has used a devious means to sow fear of Russian cyberattacks. In December 2016, DHS and the FBI published a long list of IP addresses as indicators of possible Russian cyberattacks. But most of the addresses on the list had no connection with Russian intelligence, as former U.S. government cyber-warfare officer Rob Lee found on close examination.
When someone at the Burlington, Vt., Electric Company spotted one of those IP addresses on one of its computers, the company reported it to DHS. But instead of quietly investigating the address to verify that it was indeed an indicator of Russian intrusion, DHS immediately informed The Washington Post. The result was a sensational story that Russian hackers had penetrated the U.S. power grid. In fact, the IP address in question was merely Yahoo’s email server, as Rob Lee told me, and the computer had not even been connected to the power grid. The threat to the power grid was a tall tale created by a DHS official, which the Post had to embarrassingly retract.
Since May 2017, DHS, in partnership with the FBI, has begun an even more ambitious campaign to focus public attention on what it says are Russian “targeting” and “intrusions” into “major, high value assets that operate components of our Nation’s critical infrastructure”, including energy, nuclear, water, aviation and critical manufacturing sectors. Any evidence of such an intrusion must be taken seriously by the U.S. government and reported by news media. But in light of the DHS record on alleged threats to election infrastructure and the Burlington power grid, and its well-known ambition to assume leadership over cyber protection, the public interest demands that the news media examine DHS claims about Russian cyber threats far more critically than they have up to now.
Gareth Porter is an independent investigative journalist and winner of the 2012 Gellhorn Prize for journalism. His latest book is Manufactured Crisis: The Untold Story of the Iran Nuclear Scare.
Promoters of Saudi Prince as Feminist Reformer Are Silent on His Crackdown on Women
By Adam Johnson | FAIR | May 23, 2018
During his US PR tour in March, Saudi prince and de facto ruler of the absolute monarchy Mohammed bin Salman (often referred to as “MBS”) touted the progress the kingdom was making in the area of “women’s rights”—namely letting women drive and combatting nebulous reactionary forces that were somehow separate from the regime.
Since then, at least seven major women’s rights advocates—Eman al-Nafjan, Loujain al-Hathloul, Aziz al-Yousef, Aisha al-Manea, Madiha Al-Ajroush, Walaa Al-Shubbar and Hasah Al-Sheikh—have been detained by Saudi authorities and, according to at least one report (Middle East Eye, 5/22/18), may face the death penalty.
Two of the biggest media corners that helped sell bin Salman as a feminist reformer during the trip and the months leading up to it—the New York Times opinion pages and CBS News’ 60 Minutes—have not published any follow-up commentary on bin Salman’s recent crackdown on women’s rights campaigners (Independent, 5/22/18). Let’s review their past coverage:
- “In some ways, Prince Mohammed bin Salman, who serves as defense minister, is just what his country needs…. He would allow concerts, and would consider reforming laws tightly controlling the lives of women.” —New York Times editorial board (“The Young and Brash Saudi Crown Prince,” 6/23/17)
- “I never thought I’d live long enough to write this sentence: The most significant reform process underway anywhere in the Middle East today is in Saudi Arabia….There was something a 30-year-old Saudi woman social entrepreneur said to me that stuck in my ear. ‘We are privileged to be the generation that has seen the before and the after.’ The previous generation of Saudi women, she explained, could never imagine a day when a woman could drive and the coming generation will never be able to imagine a day when a woman couldn’t.” —Thomas Friedman (New York Times, 11/23/17)
- “He is emancipating women…. He has curbed the powers of the country’s so-called ‘religious police,’ who until recently were able to arrest women for not covering up.”—Norah O’Donnell (60 Minutes, 3/19/18)
The 60 Minutes interview was panned by many commentators at the time. “A crime against journalism,” The Intercept’s Mehdi Hasan (3/19/18) called it. “Embarrassing to watch,” insisted Omar H. Noureldin, VP of the the Muslim Public Affairs Council (Twitter, 3/20/18). “It was more of an Entertainment Tonight puff piece than a serious interview with journalistic standards.”
The New York Times editorial, while not quite as overtly sycophantic as Friedman and O’Donnell, still broadly painted the ruler as a “bold” and “brash” “reformer.”
Since the mass arrests of women’s group’s on Saturday, the Times news section has run several AP stories (5/18/18, 5/22/18) on the crackdown and one original report (5/18/18), but the typically scoldy editorial board hasn’t issued a condemnation of the arrests. They did, however, take time to condemn in maximalist terms the “violent regime” of Venezuela (5/21/18), insisting on “getting rid” of recently re-elected president Nicolas Maduro, and ran a separate editorial cartoon (5/22/18) showing Maduro declaring victory over the corpses of suffering Venezuelans.
Nor did MBS’s biggest court stenographer, Thomas Friedman, find room in his latest column in his latest column (5/22/18) to note the crackdown. Given Times opinion page editor James Bennet was clear his paper was axiomatically “pro-capitalism” (3/1/18), one wonders whether he views Latin American socialists as uniquely worthy of condemnation, whereas Middle East petrol dictatorships that invest in American corporations and hosts glossy tech conferences deserve nuance and mild “reform” childing. We have to “get rid of” the former, and the latter simply need “guidance” from the US—their respective human rights records a total non-factor.
CBS ran a 50-second story on the “emancipating” MBS’s crackdown on its web-only news network, CBSN (5/21/18), and an AP story on its website (5/19/18), but CBS News has thus far aired nothing on the flagrant human rights violation on any of the news programs on its actual network, and certainly nothing in the ballpark of its most-watched prime time program, 60 Minutes.
If influential outlets like the Times opinion section and CBS News are going to help build up bin Salman’s image as a “reformer” and a champion of women’s rights, don’t they have a unique obligation to inform their readers and viewers when the image they built up is so severely undermined? Shouldn’t Bennet’s editorial board and Friedman—who did so much to lend legitimacy to the Saudi ruler’s PR strategy—be particularly outraged when he does a 180 and starts arresting prominent women’s rights advocates? Will 60 Minutes do a comparable 27-minute segment detailing these arrests and their chilling effect on activism?
This is all unlikely, since US allies’ crackdown on dissent is never in urgent need of clear moral condemnation; it’s simply a hiccup on the never-ending road to “reform.”
Witch Hunt: “Fake News” Software Touted by CBS News
Creator Admits He Made Up Who Went on Hit List
Yves Smith | Naked Capitalism | December 7, 2016
One of most pernicious means underway to crush independent news sites is the release of software tools that brand them as unreliable. This means that hidden developers and the parties that fed them information are beyond any accountability, yet would serve as censors.
Last week, the Financial Times described efforts to use software to designate certain sites as suspect:
Concern over the impact on voters of soaring amounts of fake news during the US election has sparked a hackathon where the technology industry and the media’s top thinkers are seeking to find new ways to prioritise the truth.
A community has gathered to share ideas around a 58-page Google document started by Eli Pariser, the author of a best-selling critique of social media, The Filter Bubble: What the Internet is hiding from you. A professor has circulated a spreadsheet of reliable and less reliable news sources for comment, while hackathons at Princeton and in the Bay Area have produced prototype products that Facebook could copy…
A team of students won a prize sponsored by Google at a Princeton hackathon last week by creating a quick and dirty prototype of a product that does just that: showing Facebook users a “trust rating” for stories they see, based on an online safety rating provided by “World of Trust”.
If you read the article in full, you’ll see it depicts Wikipedia as a gold standard. As Gary Null discussed yesterday in his Progressive Commentary Hour show (we were a guest; the archived interview should be up later today), it is in fact very difficult to get corrections of Wikipedia entries. Similarly, on certain topics, such as economics, Wikipedia minimizes or excludes non-mainstream views even when they have solid empirical underpinnings and have been given a hearing in academic journals and the press.
The faith in coders coming up with a magic bullet for information validation is similarly questionable. The concern about “fake news” on the Internet is almost comical given that more citizens encounter “fake news” via seeing National Enquirer and National Examiner covers in grocery stores than via websites. It is not hard to imagine that much of the tender concern expressed by the mainstream media is commercial: independent news and analysis sites threaten their legitimacy by exposing how dependent they are on stories planted by government or business sources that these press outlets often fail to vet adequately.
One approach is browser extensions that flag sites as suspect via undisclosed, unverifiable methods. Browser extensions are a particularly pernicious approach, since many users are not even aware that they have installed them, and they update automagically in the background. Most consumers do not know how to check for them or remove them.
Shadowproof exposed how this technological response is being deployed in a reckless, fact-free, libelous manner against Shadowproof, Naked Capitalism, and other long-standing, well-regarded websites. Worse, this dodgy tool was promoted by CBS News. As Kevin Gosztola reports:
CBS News reported developers increased pressure on Facebook to address its “fake news problem” with a browser extension for Chrome and Firefox called the “B.S. Detector.” It claimed the extension relies upon “a constantly-updated list of known fake news sites, propaganda mills and ‘promoters of kooky conspiracy theories’” as a reference point.
However, CBS News was wrong. The extension is not “constantly updated.” The extension, as developer Daniel Sieradski shared, was created to “make fun” of Facebook. Sieradski “scraped some data together” that included sites, which are not “fake news” websites. (One of those sites was Shadowproof.com.)
“B.S. Detector” displays a red banner that indicates a news website is “not a reliable news source.” Up until publication, the extension still flagged Consortium News, Naked Capitalism, Truthout, and Truthdig, even though Sieradski said they would not be listed in the update….
Sieradski claims he never expected this to achieve the kind of success or interest it has garnered in the past couple weeks. He seems reluctant to own the mistakes made and publish a list of the websites that were wrongly included in the initial launch in order to exonerate them.
It does not matter if the improper inclusion of certain websites was done maliciously or accidentally. The effect is the same, at this point. People who do not know better can install the extension, and if they become a unique or new viewer to Consortium News, Naked Capitalism, Truthout, or Truthdig, they will see a red banner that may discourage them from further reading and visits to these sites.
Gosztola is being unduly charitable in how he characterizes the casual way with which Sieradski went about smearing small websites. Sieradski’s Twitter handle is @selfagency and business name is The Self Agency, LLC. This page on GitHub, selfagency/bs-dector, contains this astonishing admission:
As I have repeatedly stated in the press, on our repo, and on our homepage, the dataset was somewhat indiscrimintely compiled and we are slowly making our way through it. We are also looking to partner with media watchdog groups to provide research to back up our inclusions and classifications so that it is neither arbitrary nor the decision of a sole authority.
This is an admission of reckless disregard for accuracy for someone who is making himself an arbiter and doing damage to small sites that have worked long and hard to establish their reputations. This is defamation, pure and simple. Sieradski claims that he is not acting as a censor when he is doing precisely that. The fact that he may get others to participate in this witch hunt does not change the fundamental nature of the activity.
In fact, Sieradski’s ability to rationalize that what he is doing here is on the up and up by virtue of his having donated to the EFF, ACLU, and Chelsea Manning’s defense funds is yet another example of Upton Sinclair’s aphorism, “It is difficult to get a man to understand something when his salary depends on his not understanding it.”
Gosztola points out that the reason that Sieradski was so casual about smearing well-established sites and so unapologetic about reputational harm is that they are assumed to lack the resources to take legal action:
The developers also possess a few viewpoints, which may inhibit their ability to develop an extension that is objective and valuable to news readers.
One, Sieradski has no idea how to handle the problem of corporate news media, which publishes “fake news.” Journalist Marcy Wheeler asked Sieradski why “mainstream fake news” was not flagged through this extension. She wondered why “Squawk Box” financial-type news that pushes a made-up “market” narrative is not flagged. Or what about Fox News? Why aren’t they flagged as a “fake news” website?
Sieradski replied, “We’re working on gathering data on all NewsCorp titles,” and looking for “examples of false stories that point to a pattern of intent to mislead the public.”
It is abundantly evident the developers are going through a much more rigorous process to determine whether it is proper to include Fox News than it is going through other independent news media sites that possibly should not be flagged. Of course, their inclusion is much more detrimental to them because unlike corporate news outlets they do not have significant money and resources.
Due to the traditional media’s eagerness to use the “fake news” meme to regain control over what they once called “the discourse,” independent news sites are under the threat of death by a thousand at best uninformed and at worst malicious efforts to silence them. And for a soi-disant progressive like Sieradski to take up this rancid cause is deeply disturbing.
Corporate Media Backing Clinton Exploits Orlando Shooting for Passive Holocaust Denial
By Robert Barsocchini | Empire Slayer | June 16, 2016
Within hours of the mass shooting in Orlando, the corporate media backing neoconservative favorite Hillary Clinton began, almost unanimously, to exploit the opportunity to passively promote holocaust and genocide denial.
Outlets including the NY Times, CBS News, NBC News, CNN, Newsweek, USA Today, and so on, all referred to the Orlando massacre unequivocally as the worst shooting and/or worst act of gun violence in US history. (CBS News, at the time it was accessed for this piece, was running a large “I’m With Her” ad for Hillary Clinton at the top of its page.) A useful comparison to the corporate assessment might be to imagine if a German civilian gassed a group of people to death and the German press reported it as the worst gassing in German history. After the Paris shooting, the Western press likewise reported that as the worst shooting in recent Parisian history, despite that the Parisian police not long ago massacred some 300 peaceful marchers protesting the French dictatorship in Algeria and dumped their bodies in the river that runs through the city (more info in previous piece).
Native News Online quickly pointed out that the corporate media was almost completely whitewashing “mass killings of American Indians in its reporting” on Orlando. It gave two well-known (as far as these go) examples of worse gun-violence and mass-shootings: some 300 Native men, women, and children, were massacred at Wounded Knee, and 70 to 180 were massacred at Sand Creek.
One commenter on the Native News piece shared that she “wrote to every single news outlet yesterday from the New York Times, the Guardian, the Huffington Post, and Salon to CNN, NBC, and the BBC. I have yet to receive a reply from any of them with the exception of the Oregonian, who changed its language immediately. They also informed me that the Associated Press has just begun to change its language. I’m hoping the Guardian and BBC begin to do the same too.”
Another commenter on the Native News piece gave a short list of some acts of gun-violence, mass-shootings, or mass killings perpetrated in US history, by US forces:
1864 – 300 Yana in California
1863 – 280 Shoshone in Idaho
1861 – 240 Wilakis in California
1860 – 250 Wiyot in California
1859 – 150 Yuki in California
1853 – 450 Tolowa in California
1852 – 150 Wintu in California
1851 – 300 Wintu in California
1850 – 100 Pomo in California
1840 – 140 Comanches in Colorado
1833 – 150 Kiowa in Oklahoma
1813 – 200 Creek in Alabama
1813 – 200 Creek in Alabama
1782 – 100 Lanape in Pennsylvania
1730 – 500 Fox in Illinois
1713 – 1000 Tuscarora in North Carolina
1712 – 1000 Fox in Michigan
1712 – 300 Tuscarora in North Carolina
1704 – 1000 Apalachee killed & 2000 sold into slavery in North Carolina
1676 – 100 Algonquian and Nipmuc in Massachusetts.
1676 – 100 Occaneechi in Virginia
1675 – 340 Narragansett in Rhode Island
1644 – 500 Lanape in New York
1640 – 129 Massapeag in New York
1637 – 700 Pequot in Connecticut
1623 – 200 Powhatan & Pamunkey in Virginia with “poison wine”
Professor David E. Stannard describes one such massacre, wherein US forces weakened a Delaware group of Native men, women, children, and elders through starvation, convinced them it would be in their best interest to disarm, then tied them up and exterminated them and mutilated their dead bodies. Stannard notes that such massacres by US forces “were so numerous and routine that recording them eventually becomes numbing”. (American Holocaust, pp. 125/6)
A couple of corporate news outlets used somewhat more precise language to describe the Orlando massacre, editorializing (while again presenting it as fact) that it was the ‘worst shooting in modern US history’.
However, this still leaves unstated the writer’s opinion of what constitutes ‘modern’. The wounded knee massacre took place in 1898, and the Black Wall Street massacre, for example, in which 55-400 people were murdered and a wealthy black community in Oklahoma ethnically cleansed, took place in 1921. (More examples.)
And, of course, the US has massacred millions of people, many of them with rifles and other types of guns, but also in far worse ways, outside the territory it officially claims, and continues to do so. Obama recently massacred almost a hundred people at one time with what could be viewed as an AR-15 on steroids. Is any of this part of ‘modern US history’? Why or why not? The qualifications are unstated and thus subjective. The vague language from the neoliberal, government-linked corporate outlets may lead readers to believe that all of US history is included in their ‘factual’ statements, and that the US has never massacred more than fifty people anywhere.
In some cases, this impression will have been intentional on the part of the oligarch mouthpiece outlets, which have an interest in fostering a benevolent image of the US to help elites further capture global markets . In others, it will have been a result of conveniently self-aggrandizing ignorance on behalf of the writers and editors – an ignorance that makes an important contribution to their job security.
As some of them partially or belatedly demonstrated, all of the corporate outlets could have easily avoided any holocaust/genocide-denial by calling the shooting the worst by a single civilian on US territory in at least the last thirty years, or any number of other obvious, simple, direct phrasings, which are supposed to be integral to journalism, anyway.
But as John Ralston Saul points out, the neoliberal/neoconservative ideology relies on the ‘whitewashing of memory’. That doesn’t always work, though, especially on survivors of US and Western genocides, which is why, as Ralston Saul further notes, the West and its proxies are behind most of the global murders of writers, who may try to expose facts and evidence that interfere with the West’s historical whitewashing.
Since the Orlando massacre, both Clinton and Trump have called for further escalation of Western aggression in the Middle East.
Robert Barsocchini is an internationally published author who focuses on force dynamics, national and global, and also writes professionally for the film industry. Updates on Twitter.
Law Enforcement Misrepresentation of Orlando Killer’s 911 Call Ignores U.S. Foreign Policy Motivation
By Matt Peppe | Just the Facts | June 14, 2016
In the aftermath of the horrific mass murder at the Pulse nightclub in Orlando over the weekend in which 50 people were killed, media including CNN, USA Today, NPR, NBC News, and CBS News, all reported that the gunman called 911 during his murderous rampage and pledged allegiance to ISIS. None of the journalists writing for any of these news outlets heard the call themselves; they all cite the FBI as their source.
The U.S. government has been engaged in a war against the self-professed Islamic State for the last two years. Their military intervention consists of a bombing campaign against ISIS targets in Iraq and Syria. Hyping the threat members connected to the terror group – or spiritually loyal to it – pose to American citizens is supportive of U.S. foreign policy. If ISIS, or people claiming to act on behalf of ISIS, are a real danger to Americans, it bolsters the notion that the group is a threat to national security and helps justify the government’s military response.
The FBI seems eager to show itself as disrupting ISIS plots in the States. As Adam Johnson has written in FAIR, the FBI has put Americans in contact with informants who claim to represent ISIS and then led the targets to believe they would help the targets join the terrorist organization. The media have then conflated this with an “ISIS Plot” and “ISIS Support,” when no members of ISIS were ever involved in any way.
The FBI’s motivation to portray events in a way that supports U.S. foreign policy, and its history of portraying its actions in a way that has served to hype an ISIS threat should make journalists cautious about taking officials’ words at face value. Especially in the case of a 911 call, which is a public record in Florida, proper journalistic due diligence would be to consult the actual source of the claims being disseminated.
Instead, not a single journalist appears to have done this with Orlando killer Omar Mateen’s 911 call.
On Tuesday, CNN aired interviews of eyewitnesses to the shooting spree who described their harrowing encounters with the gunman inside the club. Patience Carter, who was inside a bathroom stall feet from the gunman when he called 911, said he told the dispatcher that “the reason why he was doing this is because he wants America to stop bombing his country.” (Mateen is a native of the United States, but he was presumably referring to Afghanistan, where both of his parents are from.) She said he then declared that “from now on he pledges his loyalty to ISIS.”
This demonstrates that his primary motive for his terror attack was retaliation for the U.S. aggression in Afghanistan, where nearly 100,000 people have been killed since the illegal U.S. invasion in 2001. His mention of ISIS seems merely adjunct to what he admits was his justification for the attack. His motivation precedes his ideological alignment with ISIS, not the other way around.
Anti-war activists have long argued that overseas military operations endanger not only the populations whose countries are invaded, occupied and bombed, but Americans in the United States who are at risk of terrorist retaliation from people outraged by the death and destruction war inevitably produces to the point of being willing to resort to violence themselves.
Carter’s version of the 911 call reveals a very different picture than the partial one revealed by the FBI and reprinted by each of the largest news organizations. The complete conversation depicts Mateen as indicating that he considered his actions a response to U.S. foreign policy. Of course, the murder of innocent civilians is always reprehensible and can never be justified by claiming they are a response to a state’s military aggression, regardless of how deadly and devastating such military operations are. But it should be predictable that some people will use this rationalization regardless and seek out soft targets in the country whose government they claim to be retaliating against.
The FBI chose to omit Mateen’s professed motive entirely when recounting the 911 call to the media, and merely state that he professed allegiance to ISIS. Perhaps they recognized how putting Mateen’s call in context may lead people to question whether U.S. wars in Afghanistan (and Iraq) raise the terrorist threat at home.
After all, this is not the first time this has happened. The surviving Boston Marathon bomber cited the U.S. wars abroad as his motivation for committing the attack that killed three people and maimed dozens more.
It is not clear whether any journalist even asked to hear the 911 call themselves. But it is clear that they chose to disseminate second-hand information when the primary source should have been easily accessible. If it was not made available (as required by law), the public deserves to know that it was suppressed and be given an explanation why.
Media stenographers parroted government officials’ descriptions of the call, which left out the killer’s professed motivation for his politically motivated attack and failed to put the ISIS claim in any context. Unsurprisingly, their misrepresentation served the government’s policy agenda and avoided having the incident serve as an example of a negative consequence of U.S. foreign policy – one that anti-war dissenters have used in arguing against the wars in Afghanistan and Iraq since the War on Terror was launched more than a decade and a half ago.
Israel Censors Bob Simon’s Report on Palestinian Christians
Al-Manar | April 26, 2012
During Sunday night’s episode of “60 Minutes,” reporter Bob Simon’s story on Arab Christians included a heated confrontation between himself and the Zionist ambassador to the United States Michael Oren.
The “60 Minutes” story tackled the displacement of Palestinian Christians by the Zionist Occupation of the West Bank and East Jerusalem.
Oren also called Simon’s report “outrageous” and “incomprehensible,” and reportedly called Jeff Fager, the chairman of CBS News, before the broadcast and said he had information the “60 Minutes” story was “a hatchet job.” He was concerned that the piece was critical of the Zionist entity and could harm its reputation among American Christians.
In its report, Simon told Americans that there are Palestinian Christians, and the Right wing Zionists have attempted to displace, expropriate and erase the Palestinian nation, and to convince them that Palestinians don’t exist or if they do are enemies of the U.S.
According to the report, when the foe of the US was the Soviet Union, they made the Palestinians Communists. When the foe became al-Qaeda, they made the Palestinians violent fundamentalists. But if some percentage of Palestinians is Christians, then that fact disrupts the propaganda. In fact, millions of Palestinians are descended from the 700,000 or so Palestinians ethnically cleansed by the Israelis from what is now Israel in 1948, of whom about 10 percent were Christian.
The report also mentioned that some Palestinians are Lutherans, Catholics and Episcopalians, establishing a link of commonality between them and Americans, which raised the ire of the entity of occupation because it wants Americans identifying only with the so-called ‘Israelis’, not with Palestinians.
It also told Americans that ‘Israel’ is occupying and colonizing Palestinian land, and it let it slip that Palestinians in the West Bank need a permit to travel to Arab East Jerusalem and are subjected within the West Bank to humiliating check points that turn a 7 mile journey into an all-day ordeal.
Simon’s story allowed Palestinians to speak for themselves as well, and to refute Oren’s anti-Palestinian talking points, where it mentioned a prominent Palestinian businessman and Coca Cola distributor saying that he knew of no Palestinian Christians who were leaving the West Bank and Jerusalem because of Muslims but that rather they were leaving because of the “Israeli Oppression.”
The report allowed the Palestinians to point out that the West Bank now looks like Swiss cheese, with Zionist colonies grabbing the good land and water, and the stateless Palestinians pushed into the holes; and that the way the Israelis built the Separation Wall isolated Bethlehem, Jesus’s birthplace and a city that still is 18% Christian, had made it “an open-air prison.”
It also described the Palestinian Kairos Document, calling for nonviolence, as a peaceful struggle by Palestinians against the Zionist Occupation and land grabs, particularly when it quoted a Zionist scholar putting “Political Judaism” on par with “Political Islam.”
According to sources, news of Simon’s “60 Minutes” report reached the highest governmental levels of the Zionist entity, where a main daily Haaretz reported Tuesday that PM Benjamin Netanyahu and his political adviser Ron Dermer were “fully informed on the affair almost since its start.”
A source told Haaretz that Israel’s unsuccessful attempts to kill the “60 Minutes” report backfired as Oren’s call to Fager became a central part of the story. “We awakened the dead,” the source said.
However, officials in the Prime Minister’s Office disagreed and insisted that their efforts delayed the broadcast and made the final version “softer.”
Related articles
- A Palestinian Christian response to Michael Oren (alethonews.wordpress.com)
 This recently-issued study (the “Assessment”) was seized on by the media as proof of the massive damage the US will suffer if nothing is done about climate change. The Assessment’s conclusions are based largely on speculative model projections that aren’t amenable to checking, but it also claims that the US is already experiencing some of the impacts of man-made climate change, and these claims can be checked. This post accordingly evaluates them claim-by-claim and finds that they are rarely backed up by any hard data, that in some cases they are contradicted by disclaimers buried in the text, and that in no case is there any hard evidence that conclusively relates the impacts to man-made climate change. The credibility of the Assessment’s predictions can be judged accordingly.
This recently-issued study (the “Assessment”) was seized on by the media as proof of the massive damage the US will suffer if nothing is done about climate change. The Assessment’s conclusions are based largely on speculative model projections that aren’t amenable to checking, but it also claims that the US is already experiencing some of the impacts of man-made climate change, and these claims can be checked. This post accordingly evaluates them claim-by-claim and finds that they are rarely backed up by any hard data, that in some cases they are contradicted by disclaimers buried in the text, and that in no case is there any hard evidence that conclusively relates the impacts to man-made climate change. The credibility of the Assessment’s predictions can be judged accordingly.





 Figure 7: Record daily highs in the US. The meaning of “ratio of daily temperature records” isn’t clear
Figure 7: Record daily highs in the US. The meaning of “ratio of daily temperature records” isn’t clear Figure 8: US annual heat wave index since 1895
Figure 8: US annual heat wave index since 1895
 Figure 10: Acres burned by US wildfires. Figure 9 data carried back to 1926
Figure 10: Acres burned by US wildfires. Figure 9 data carried back to 1926 Figure 11: Acreage burned by naturally-occurring wildfires vs. acreage burned by climate-change-caused wildfires
Figure 11: Acreage burned by naturally-occurring wildfires vs. acreage burned by climate-change-caused wildfires Figure 12: Unadjusted hurricane counts, hurricane counts adjusted for undercounting and hurricanes making landfall in the US
Figure 12: Unadjusted hurricane counts, hurricane counts adjusted for undercounting and hurricanes making landfall in the US






 Figure Figure 20: Relative sea level rise, Sewell’s Point, Virginia
Figure Figure 20: Relative sea level rise, Sewell’s Point, Virginia
 Figure 22: Snow-Covered Area in North America, 1972-2015
Figure 22: Snow-Covered Area in North America, 1972-2015