Poland Lost World War II
Tales of the American Empire | July 22, 2021
World War II began to defend Poland from foreign invaders. Millions of Poles perished as their nation was devastated during the war, yet it remained under foreign rule. Official history suggests that the United States and Britain had no choice but to cede Poland to the Soviets. This is false since the Germans were anxious for peace with the West and had offered to withdraw to 1914 German borders several times. A peace treaty could have been signed with Germany, which may have included the exile of Nazi leaders, perhaps after a military coup. A conditional surrender agreement was never pursued leaving Europe was much worse off after the war.
__________________________________________
Related Tale: “Everyone Lost in World War II”; https://www.youtube.com/watch?v=lXHxi…
Related Tale: “The American Occupation of Iran 1941-1978”; https://www.youtube.com/watch?v=78yu7…
“The French and British Betrayal of Poland in 1939”; World Future Fund; http://www.worldfuturefund.org/wffmas…
“List of assassination attempts on Adolf Hitler”; Wikipedia; https://en.wikipedia.org/wiki/List_of…
“Roosevelt’s Fraud at Yalta and the Mirage of the ‘Good War’”; James Bovard; The Future of Freedom Foundation; August 25, 2020; https://www.fff.org/explore-freedom/a…
“Churchill’s Betrayal of Poland”; History Channel; https://www.youtube.com/watch?v=mYJ1_…
July 26, 2021 Posted by aletho | Timeless or most popular, Video | France, UK, United States | Leave a comment
Vaccine Lawsuit Filed: Insider Blows Whistle on Coverup
By Spiro Skouras | Activist Post | July 22, 2021
In this exclusive interview, Spiro is joined by Attorney Ana Garner who is a member of the legal team that recently filed a lawsuit against the Secretary of the Department of Health and Human Services (HHS).
The lawsuit is focused on the experimental Covid vaccine, the Emergency Use Authorization (EUA) and includes sworn testimony from a whistleblower alleging the government reporting systems for adverse reactions to the Covid vaccine is under-reporting deaths by at least five times and projects the real numbers are closer to 45,000 people who died after receiving the vaccine.
https://www.bitchute.com/embed/k1YYsLBT7HIF/
Previous Interview With Ana Garner
Or watch on YouTube:
July 25, 2021 Posted by aletho | Timeless or most popular, Video | Covid-19, COVID-19 Vaccine, United States | Leave a comment
Meet Toka, the Most Dangerous Israeli Spyware Firm You’ve Never Heard Of
By Whitney Webb | MintPress News | July 21, 2021
LONDON –This past Sunday, an investigation into the global abuse of spyware developed by veterans of Israeli intelligence Unit 8200 gained widespread attention, as it was revealed that the software – sold to democratic and authoritarian governments alike – had been used to illegally spy on an estimated 50,000 individuals. Among those who had their communications and devices spied on by the software, known as Pegasus, were journalists, human rights activists, business executives, academics and prominent political leaders. Among those targeted political leaders, per reports, were the current leaders of France, Pakistan, South Africa, Egypt, Morocco and Iraq.
The abuse of Pegasus software in this very way has been known for several years, though these latest revelations appear to have gained such traction in the mainstream owing to the high number of civilians who have reportedly been surveilled through its use. The continuation of the now-years-long scandal surrounding the abuse of Pegasus has also brought considerable controversy and notoriety to the Israeli company that developed it, the NSO Group.
While the NSO Group has become infamous, other Israeli companies with even deeper ties to Israel’s intelligence apparatus have been selling software that not only provides the exact same services to governments and intelligence agencies but purports to go even farther.
Originally founded by former Israeli Prime Minister and Jeffrey Epstein associate Ehud Barak, one of these companies’ wares are being used by countries around the world, including in developing countries with the direct facilitation of global financial institutions like the Inter-American Development Bank (IDB) and the World Bank. In addition, the software is only made available to governments that are “trusted” by Israel’s government, which “works closely” with the company.
Despite the fact that this firm has been around since 2018 and was covered in detail by this author for MintPress News in January 2020, no mainstream outlet – including those that have extensively covered the NSO Group – has bothered to examine the implications of this story.
Worse than Pegasus
Toka was launched in 2018 with the explicit purpose of selling a “tailored ecosystem of cyber capabilities and software products for governmental, law enforcement, and security agencies.” According to a profile of the company published in Forbes shortly after it launched, Toka advertised itself as “a one-stop hacking shop for governments that require extra capability to fight terrorists and other threats to national security in the digital domain.”
Toka launched with plans to “provide spy tools for whatever device its clients require,” including not only smartphones but a “special focus on the so-called Internet of Things (IoT).” Per the company, this includes devices like Amazon Echo, Google Nest-connected home products, as well as connected fridges, thermostats and alarms. Exploits in these products discovered by Toka, the company said at the time, would not be disclosed to vendors, meaning those flaws would continue to remain vulnerable to any hacker, whether a client of Toka or not.
Today, Toka’s software suite claims to offer its customers in law enforcement, government and intelligence the ability to obtain “targeted intelligence” and to conduct “forensic investigations” as well as “covert operations.” In addition, Toka offers governments its “Cyber Designers” service, which provides “agencies with the full-spectrum strategies, customized projects and technologies needed to keep critical infrastructure, the digital landscape and government institutions secure and durable.”
Given that NSO’s Pegasus targets only smartphones, Toka’s hacking suite – which, like Pegasus, is also classified as a “lawful intercept” product – is capable of targeting any device connected to the internet, including but not limited to smartphones. In addition, its target clientele are the same as those of Pegasus, providing an easy opportunity for governments to gain access to even more surveillance capabilities than Pegasus offers, but without risking notoriety in the media, since Toka has long avoided the limelight.
In addition, while Toka professes that its products are only used by “trusted” governments and agencies to combat “terrorism” and maintain order and public safety, the sales pitch for the NSO Group’s Pegasus is remarkably similar, and that sales pitch has not stopped its software from being used to target dissidents, politicians and journalists. It also allows many of the same groups who are Toka clients, like intelligence agencies, to use these tools for the purpose of obtaining blackmail. The use of blackmail by Israeli security agencies against civilian Palestinians to attempt to weaken Palestinian society and for political persecution is well-documented.
Toka has been described by market analysts as an “offensive security” company, though the company’s leadership rejects this characterization. Company co-founder and current CEO Yaron Rosen asserted that, as opposed to purely offensive, the company’s operations are “something in the middle,” which he classifies as bridging cyber defense and offensive cyber activities — e.g., hacking.
The company’s activities are concerning in light of the fact that Toka has been directly partnered with Israel’s Ministry of Defense and other Israeli intelligence and security agencies since its founding. The company “works closely” with these government agencies, according to an Israeli Ministry of Defense website. This collaboration, per Toka, is meant to “enhance” their products. Toka’s direct IDF links are in contrast to the NSO Group, a company that does not maintain overt ties with the Israeli security state.
Toka’s direct collaboration with Israel’s government is also made clear through its claim that it sells its products and offers its services only to “trusted” governments, law enforcement agencies and intelligence agencies. Toka’s Rosen has stated that Russia, China, and “other enemy countries” would never be customers of the company. In other words, only countries aligned with Israeli policy goals, particularly in occupied Palestine, are permitted to be customers and gain access to its trove of powerful hacking tools. This is consistent with Israeli government efforts to leverage Israel’s hi-tech sector as a means of countering the Boycott, Divest and Sanctions (BDS) movement globally.
Further evidence that Toka is part of this Israeli government effort to seed foreign governments with technology products deeply tied to Israel’s military and intelligence services is the fact that one of the main investors in Toka is Dell Technologies Capital, which is an extension of the well-known tech company Dell. Dell was founded by Michael Dell, a well-known pro-Israel partisan who has donated millions of dollars to the Friends of the IDF and is one of the top supporters of the so-called “anti-BDS” bills that prevent publicly employed individuals or public institutions in several U.S. states from supporting non-violent boycotts of Israel, even on humanitarian grounds. As MintPress previously noted, the fact that a major producer of consumer electronic goods is heavily investing in a company that markets the hacking of that very technology should be a red flag.
The government’s initial admitted use of the hi-tech sector to counter the BDS movement coincided with the launch of a new Israeli military and intelligence agency policy in 2012, whereby “cyber-related and intelligence projects that were previously carried out in-house in the Israeli military and Israel’s main intelligence arms are transferred to companies that, in some cases, were built for this exact purpose.”
One of the reasons this was reportedly launched was to retain members of Unit 8200 engaged in military work who were moving to jobs in the country’s high-paying tech sector. Through this new policy that has worked to essentially merge much of the private tech sector with Israel’s national security state, some Unit 8200 and other intelligence veterans continue their work for the state but benefit from a private sector salary. The end result is that an unknown – and likely very high – number of Israeli tech companies are led by veterans of the Israeli military and Israeli intelligence agencies and serve, for all intents and purposes, as front companies. A closer examination of Toka strongly suggests that it is one such front company.
Toka — born out of Israel’s national security state
The company was co-founded by Ehud Barak, Alon Kantor, Kfir Waldman and retired IDF Brigadier General Yaron Rosen. Rosen, the firm’s founding CEO and now co-CEO, is the former Chief of the IDF’s cyber staff, where he was “the lead architect of all [IDF] cyber activities,” including those executed by Israeli military intelligence Unit 8200. Alon Kantor is the former Vice President of Business Development for Check Point Software, a software and hardware company founded by Unit 8200 veterans. Kfir Waldman is the former CEO of Go Arc and a former Director of Engineering at technology giant Cisco. Cisco is a leader in the field of Internet of Things devices and IoT cybersecurity, while Go Arc focuses on applications for mobile devices. As previously mentioned, Toka hacks not only mobile devices but also has a “special focus” on hacking IoT devices.
A slide from an April 20, 2021 presentation given by Toka’s VP of Global Sales, Michael Anderson
In addition to having served as prime minister of Israel, Toka co-founder Ehud Barak previously served as head of Israeli military intelligence directorate Aman, as well as several other prominent posts in the IDF, before eventually leading the Israeli military as minister of defense. While minister of defense, he led Operation Cast Lead against the blockaded Gaza Strip in 2009, which resulted in the deaths of over 1,000 Palestinians and saw Israel illegally use chemical weapons against civilians.
Toka is the first start-up created by Barak. However, Barak had previously chaired and invested in Carbyne911, a controversial Israeli emergency services start-up that has expanded around the world and has become particularly entrenched in the United States. Carbyne’s success has been despite the Jeffrey Epstein scandal, given that the intelligence-linked pedophile and sex trafficker had invested heavily in the company at Barak’s behest. Barak’s close relationship with Epstein, including overnight visits to Epstein’s now-notorious island and apartment complexes that housed trafficked women and underage girls, has been extensively documented.
Barak stepped away from Toka in April of last year, likely as the result of the controversy over his Epstein links, which also saw Barak withdraw from his chairmanship of Carbyne in the wake of Epstein’s death. Considerable evidence has pointed to Epstein having been an intelligence asset of Israeli military intelligence who accrued blackmail on powerful individuals for the benefit of Israel’s national security state and other intelligence agencies, as well as for personal gain.
Another notable Toka executive is Nir Peleg, the company’s Vice President for Strategic Projects. Peleg is the former head of the Research and Development Division at Israel’s National Cyber Directorate, where he led national cybersecurity projects as well as government initiatives and collaborations with international partners and Israeli cybersecurity innovative companies. Prior to this, Peleg claims to have served for more than 20 years in leading positions at the IDF’s “elite technology unit,” though he does specify exactly which unit this was. His LinkedIn profile lists him as having been head of the IDF’s entire Technology Department from 2008 to 2011.
While at Israel’s National Cyber Directorate, Peleg worked closely with Tal Goldstein, now the head of strategy for the World Economic Forum’s Partnership against Cybercrime (WEF-PAC), whose members include government agencies of the U.S., Israel and the U.K., along with some of the world’s most powerful companies in technology and finance. The goal of this effort is to establish a global entity that is capable of controlling the flow of information, data, and money on the internet. Notably, Toka CEO Yaron Rosen recently called for essentially this exact organization to be established when he stated that the international community needed to urgently create the “cyber” equivalent of the World Health Organization to combat the so-called “cyber pandemic.”
Claims that a “cyber pandemic” is imminent have been frequent from individuals tied to the WEF-PAC, including CEO of Checkpoint Software Gil Shwed. Checkpoint is a member of WEF-PAC and two of its former vice presidents, Michael Anderson and Alon Kantor, are now Vice President for Global Sales and co-CEO of Toka, respectively.
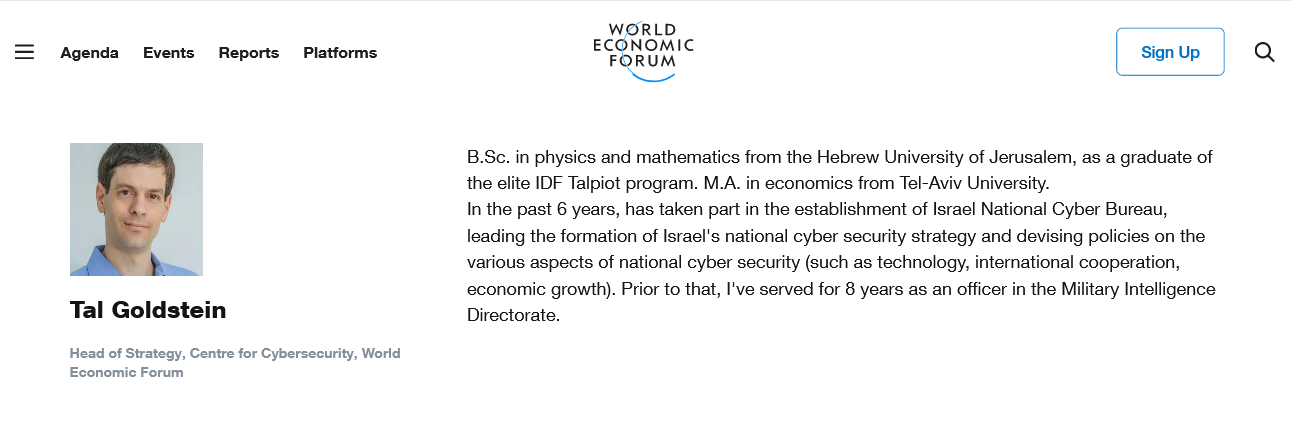
The Wolrd Economic Forum does little to hide its partnership with former Israeli intelligence officials
Toka’s Chief Technology Officer, and the chief architect of its hacking suite, is Moty Zaltsman, who is the only chief executive of the company not listed on the firm’s website. Per his LinkedIn, Zaltsman was the Chief Technology Officer for then-Israeli Prime Minister Benjamin Netanyahu. Last January, when Toka was covered by MintPress News, his profile stated that he had developed “offensive technologies” for Israel’s head of state, but Zaltsman has since removed this claim. The last Toka executive of note is Michael Volfman, the company’s Vice President of Research and Development. Volfman was previously a cyber research and development leader at an unspecified “leading technology unit” of the IDF.
Also worth mentioning are Toka’s main investors, particularly Entrèe Capital, which is managed by Aviad Eyal and Ran Achituv. Achituv, who manages Entrée’s investment in Toka and sits on Toka’s board of directors, was the founder of the IDF’s satellite-based signals intelligence unit and also a former senior vice president at both Amdocs and Comverse Infosys. Both Amdocs and Comverse courted scandal in the late 1990s and early 2000s for their role in a massive Israeli government-backed espionage operation that targeted U.S. federal agencies during that period.
Despite this scandal and others in the company’s past, Comverse subsidiary Verint was subsequently contracted by the U.S. National Security Agency (NSA) to bug the telecommunications network of Verizon shortly after their previous espionage scandal was covered by mainstream media. The contract was part of Operation Stellar Winds and was approved by then-NSA Director Keith Alexander, who has since been an outspoken advocate of closer Israeli-American government cooperation in cybersecurity.
In addition to Entrèe Capital, Andreessen Horowitz is another of Toka’s main investors. The venture capital firm co-founded by Silicon Valley titan Marc Andreessen is currently advised by former Secretary of the Treasury Larry Summers, a close friend of the infamous pedophile Jeffery Epstein. Early investors in Toka that are no longer listed on the firm’s website include Launch Capital, which is deeply tied to the Pritzker family — one of the wealthiest families in the U.S., with close ties to the Clintons and Obamas as well as the U.S.’ pro-Israel lobby — and Ray Rothrock, a venture capitalist who spent nearly three decades at VenRock, the Rockefeller family venture capital fund.
In light of the aforementioned policy of Israel’s government to use private tech companies as fronts, the combination of Toka’s direct Israeli government ties, the nature of its products and services, and the numerous, significant connections of its leaders and investors to both Israeli military intelligence and past Israeli espionage scandals strongly suggests that Toka is one such front.
If this is the case, there is reason to believe that, when Toka clients hack and gain access to a device, elements of the Israeli state could also gain access. This concern is born out of the fact that Israeli intelligence has engaged in this exact type of behavior before as part of the PROMIS software scandal, whereby Israeli “superspy” Robert Maxwell sold bugged software to the U.S. government, including highly sensitive locations involved in classified nuclear weapons research. When that software, known as PROMIS, was installed on U.S. government computers, Israeli intelligence gained access to those same systems and devices.
The U.S. government was not the only target of this operation, however, as the bugged PROMIS software was placed on the networks of several intelligence agencies around the world as well as powerful corporations and several large banks. Israeli intelligence gained access to all of their systems until the compromised nature of the software was made public. However, Israel’s government was not held accountable by the U.S. government or the international community for its far-reaching espionage program, a program directly facilitated by technology-focused front companies. The similarities between the products marketed and clients targeted by Maxwell during the PROMIS scandal and currently by Toka are considerable.
World Bank, IDB aid Toka in targeting Palestine’s allies
While the ties between Toka and Israel’s national security state are clear as day, what is also significant and unsettling about this company is how its entry into developing and developed countries alike is being facilitated by global financial institutions, specifically the World Bank and the Inter-American Development Bank. Notably, these are the only deals with governments that Toka advertises on its website, as the others are not made public.
Several projects funded by one or another of these two institutions have seen Toka become the “cyber designer” of national cybersecurity strategies for Nigeria and Chile since last year. Significantly, both countries’ populations show strong support for Palestine and the BDS movement. In addition, Toka garnered a World Bank-funded contract with the government of Moldova, an ally of Israel, last September.
The World Bank selected Toka in February of last year to “enhance Nigeria’s cyber development,” which includes developing “national frameworks, technical capabilities and enhancement of skills.” Through the World Bank contract, Toka has now become so intimately involved with both the public and private sectors of Nigeria that it relates to the country’s “cyber ecosystem.” The World Bank’s decision to choose Toka is likely the result of a partnership forged in 2019 by the state of Israel with the global financial institution “to boost cybersecurity in the developing world,” with a focus on Africa and Asia.

Toka executives pose with Nigerian officials in 2020. Photo | Israel Defense
“Designing and building sustainable and robust national cyber strategy and cyber resilience is a critical enabler to fulfilling the objectives of Nigeria’s national cybersecurity policy and strategic framework,” Toka CEO Yaron Rosen said in a press release regarding the contract.
Given Toka’s aforementioned use of its technology for only “trusted” governments, it is notable that Nigeria has been a strong ally of Palestine for most of the past decade, save for one abstention at a crucial UN vote in 2014. In addition to the government, numerous student groups, human rights organizations, and Islamic organizations in the country are outspoken in their support for Palestine. With Toka’s efforts to offer its products only to countries who align themselves with “friendly” countries, their now intimate involvement with Nigeria’s cyber development could soon have consequences for a government that has tended to support the Palestinian cause. This is even more likely given Toka CEO Rosen’s statements at an April 2021 event hosted by Israel’s Ministry of Economy, where he emphasized the role of cyber in developing countries specifically in terms of their national defense and economic strategy.
Three months after the deal was struck with Nigeria through the World Bank, the Inter-American Development Bank (IDB) selected Toka to advise the government of Chile on “next steps for the country’s national cybersecurity readiness and operational capacity building.” As part of the project, “Toka will assess the current cybersecurity gaps and challenges in Chile and support the IDB project implementation by recommending specific cybersecurity readiness improvements,” per a press release. Toka claims it will help “establish Chile as a cybersecurity leader in South America.” Regarding the deal, Toka’s Rosen stated that he was “thankful” that the IDB had “provided us with this opportunity to work with the Government of Chile.”
Israel signed consequential agreements for cooperation with the IDB in 2015, before further deepening those ties in 2019 by partnering with the IDB to invest $250 million from Israeli institutions in Latin America specifically.

Toka executives are pictured with Chilean officials during a 2020 meeting in Santiago
Like Nigeria, Chile has a strong connection with Palestine and is often a target of Israeli government influence efforts. Though the current far-right government of Sebastián Piñera has grown close to Israel, Chile is home to the largest Palestinian exile community in the world outside of the Middle East. As a result, Chile has one of the strongest BDS movements in the Americas, with cities declaring a non-violent boycott of Israel until the Piñera administration stepped in to claim that such boycotts can only be implemented at the federal level. Palestinian Chileans have strong influence on Chilean politics, with a recent, popular presidential candidate, Daniel Jadue, being the son of Palestinian immigrants to Chile. Earlier this year, in June, Chile’s congress drafted a bill to boycott goods, services and products from illegal Israeli settlements.
While Toka frames both of these projects as aimed at helping the cyber readiness and economies of the countries it now services, Israeli media has painted a different picture. For instance, Haaretz wrote that Israel’s partnerships with development banks, specifically those made in 2019 that resulted in these Toka contracts, were planned by an inter-ministerial committee set up by then-Prime Minister Benjamin Netanyahu “to realize the potential of international development to strengthen the Israeli economy, improve Israel’s political standing and strengthen its international role.” One source, quoted by Haaretz as being close to this undertaking, stated that “development banks are a way to help advance Israel’s interests and agenda in the developing world, including Latin America. But it’s not philanthropy.”
Given these statements, and Toka’s own modus operandi as a company and its background, it seems highly likely that the reason both Nigeria and Chile were chosen as the first of Toka’s development banks contracts was aimed at advancing the Israeli government’s agenda in those specific countries, one that seeks to counter and mitigate the vocal support for Palestine among those countries’ inhabitants.
The spyware problem goes far beyond NSO Group
The NSO Group and its Pegasus software is clearly a major scandal that deserves scrutiny. However, the treatment of the incident by the media has largely absolved the Israeli government of any role in that affair, despite the fact that the NSO Group’s sales of Pegasus to foreign governments has been approved and defended by Israel’s government. This, of course, means that Israel’s government has obvious responsibility in the whole scandal as well.
In addition, the myopic focus on the NSO Group when it comes to mainstream media reporting on Israeli private spyware and the threats it poses means that other companies, like Toka, go uninvestigated, even if their products present an even greater potential for abuse and illegal surveillance than those currently marketed and sold by the NSO Group.
Given the longstanding history of Israeli intelligence’s use of technology firms for international surveillance and espionage, as well as its admitted policy of using tech companies as fronts to combat BDS and ensure Israel’s “cyber dominance,” the investigation into Israeli spyware cannot stop just with NSO Group. However, not stopping there risks directly challenging the Israeli state, particularly in Toka’s case, and this is something that mainstream media outlets tend to avoid. This is due to a mix of factors, but the fact that NSO’s Pegasus has been used to spy on journalists so extensively certainly doesn’t help the matter.
Yet, Israel’s weaponization of its tech industry, and the global use of its spyware offerings by governments and security agencies around the world, must be addressed, especially because it has been explicitly weaponized to prevent non-violent boycotts of Israel’s occupation of Palestine, including those solely based on humanitarian grounds or out of respect for international laws that Israel routinely breaks. Allowing a government to engage in this activity on a global scale to stifle criticism of flagrantly illegal policies and war crimes cannot continue and this should be the case for any government, not just Israel.
If the outlets eagerly reporting on the latest Pegasus revelations are truly concerned with the abuse of spyware by governments and intelligence agencies around the world, they should also give attention to Toka, as it is actively arming these same institutions with weapons far worse than any NSO Group product.
Whitney Webb has been a professional writer, researcher and journalist since 2016. She has written for several websites and, from 2017 to 2020, was a staff writer and senior investigative reporter for MintPress News. She currently writes for her own outlet Unlimited Hangout and contributes to The Last American Vagabond and MintPress News.
July 24, 2021 Posted by aletho | Civil Liberties, Timeless or most popular | Africa, Human rights, Israel, Latin America | Leave a comment
FBI Using the Same Fear Tactic From the First War on Terror: Orchestrating its Own Terrorism Plots
Questioning the FBI’s role in 1/6 was maligned by corporate media as deranged. But only ignorance about the FBI or a desire to deceive could produce such a reaction.
By Glenn Greenwald | July 24, 2021
The narrative that domestic anti-government extremism is the greatest threat to U.S. national security — the official position of the U.S. security state and the Biden administration — received its most potent boost in October 2020, less than one month before the 2020 presidential election. That was when the F.B.I. and Michigan state officials announced the arrest of thirteen people on terrorism, conspiracy and weapons charges, with six of them accused of participating in a plot to kidnap Michigan’s Democratic Governor Gretchen Whitmer, who had been a particular target of criticism from President Trump for her advocacy for harsh COVID lockdown measures.
The headlines that followed were dramatic and fear-inducing: “F.B.I. Says Michigan Anti-Government Group Plotted to Kidnap Gov. Gretchen Whitmer,” announced The New York Times. That same night, ABC News began its broadcast this way: “Tonight, we take you into a hidden world, a place authorities say gave birth to a violent domestic terror plot in Michigan — foiled by the FBI.”
Democrats and liberal journalists instantly seized on this storyline to spin a pre-election theme that was as extreme as it was predictable. Gov. Whitmer herself blamed Trump, claiming that the plotters “heard the president’s words not as a rebuke but as a rallying cry — as a call to action.” Rep. Maxine Waters (D-CA) claimed that “the president is a deranged lunatic and he’s inspired white supremacists to violence, the latest of which was a plot to kidnap Gov. Whitmer,” adding: “these groups have attempted to KILL many of us in recent years. They are following Trump’s lead.” Vox’s paid television-watcher and video-manipulator, Aaron Rupar, drew this inference: “Trump hasn’t commended the FBI for breaking up Whitmer kidnapping/murder plot because as always he doesn’t want to denounce his base.” Michael Moore called for Trump’s arrest for having incited the kidnapping plot against Gov. Whitmer. One viral tweet from a popular Democratic Party activist similarly declared: “Trump should be arrested for this plot to kidnap Governor Whitmer. There’s no doubt he inspired this terrorism.”
New York Governor Andrew Cuomo instantly declared it to be a terrorist attack on America: “We must condemn and call out the cowardly plot against Governor Whitmer for what it is: Domestic terrorism.” MSNBC’s social media star Kyle Griffin cast it as a coup attempt: “The FBI thwarted what they described as a plot to violently overthrow the government and kidnap Michigan Gov. Gretchen Whitmer.” CNN’s Jim Sciutto pronounced it “deeply alarming.”
A lengthy CNN article — dressed up as an investigative exposé that was little more than stenography of FBI messaging disseminated from behind a shield of anonymity — purported in the headline to take the reader “Inside the plot to kidnap Gov. Whitmer.” It claimed that it all began when angry discussions about COVID restrictions “spiraled into a terrorism plot, officials say, with Michigan Gov. Gretchen Whitmer the target of a kidnapping scheme.” CNN heralded the FBI’s use of informants and agents to break up the plot but depicted them as nothing more than passive bystanders reporting what the domestic terrorists were plotting:
The Watchmen had been flagged to the FBI in March, and one of its members was now an informant. That informant, others on the inside, as well as undercover operatives and recordings, allowed the bureau to monitor what was happening from then on.
The article never once hinted at let alone described the highly active role of these informants and agents themselves in encouraging and designing the plot. Instead, it depicted these anti-government activists as leading one another — on their own — to commit what CNN called “treason in a quaint town.” The more honest headline for this CNN article would have been: “Inside the FBI’s tale of the plot to kidnap Gov. Whitmer.” But since CNN never questions the FBI — they employ their top agents and operatives once they leave the bureau in order to disseminate their propaganda — this is what the country got from The Most Trusted Name in News:

Gov. Whitmer herself attempted to prolong the news cycle as much as possible, all but declaring herself off-limits from criticism by equating any critiques of her governance with incitement to terrorism. Appearing on Meet the Press two Sundays after the plot was revealed, Whitmer said it was “incredibly disturbing that the president of the United States—10 days after a plot to kidnap, put me on trial, and execute me, 10 days after that was uncovered—the president is at it again, and inspiring, and incentivizing, and inciting this kind of domestic terrorism.”
On October 22 — just two weeks before Election Day — MSNBC’s Rachel Maddow hosted Whitmer and told the Michigan Governor that the evidence was clear that Trump had been “turning on a faucet of violent threats” against her. Whitmer agreed that Trump was to blame for the kidnapping plot by having repeatedly attacked her in his rallies:
Joe Biden also made repeated use of this storyline. Appearing at a campaign rally in Michigan on October 16, the Democratic candidate blasted Trump for the crime of continuing to criticize Whitmer even after she was the target of a terror plot. He explicitly blamed Trump for having incited it: “When the president tweeted ‘Liberate Michigan, Liberate Michigan,’ that’s the call that was heard. That was the dog whistle.” And he accused Trump of purposely stoking a wave of the worst kind of terrorism on U.S. soil: “it’s the sort of behavior you might expect from ISIS,” he said of the accused.
Yet from the start, there were ample and potent reasons to distrust the FBI’s version of events. To begin with, FBI press releases are typically filled with lies, yet media outlets — due to some combination of excessive gullibility, an inability to learn lessons, or a desire to be deceived — continue to treat them as Gospel. For another, the majority of “terror plots” the FBI claimed to detect and break up during the first War on Terror were, in fact, plots manufactured, funded and driven by the FBI itself.
Indeed, the FBI has previously acknowledged that its own powers and budget depend on keeping Americans in fear of such attacks. Former FBI Assistant Director Thomas Fuentes, in a documentary called “The Newberg Sting” about a 2009 FBI arrest of four men on terrorism charges, uttered this extremely candid admission:
If you’re submitting budget proposals for a law enforcement agency, for an intelligence agency, you’re not going to submit the proposal that “We won the war on terror and everything’s great,” cuz the first thing that’s gonna happen is your budget’s gonna be cut in half. You know, it’s my opposite of Jesse Jackson’s ‘Keep Hope Alive’—it’s ‘Keep Fear Alive.’ Keep it alive.
In the Whitmer kidnapping case, the FBI’s own affidavit in support of the charges acknowledged the involvement in the plot of both informants and undercover FBI agents “over several months.”

Excerpt of FBI affidavit criminal complaint accompanying the criminal complaint in U.S. District Court against six defendants in the Whitmer plot
In sum, there was no way to avoid suspicions about the FBI’s crucial role in a plot like this absent extreme ignorance about the bureau’s behavior over the last two decades or an intentional desire to sow fear about right-wing extremists attacking Democratic Party officials one month before the 2020 presidential election. In fact, the signs of FBI involvement were there from the start for those who — unlike CNN — wanted to know the truth.
A report from the Detroit Free Press published just two days after CNN’s FBI stenography noted that the FBI agents were incapable of identifying any specifics of this supposed plot, adding that defense attorneys were adamant that those accused were merely engaged in idle chatter, boasting that they were never really serious about following through. Then the paper added that, for defense lawyers, “it remains to be seen what roles the undercover informants and FBI agents played in the case, and whether they pushed the others into carrying out the plan.” Meanwhile, an actually independent journalist, Michael Tracey, had no trouble identifying the telltale signs of FBI orchestration that were so apparent countless times during the first War on Terror. Three days before the CNN story, he wrote:

But the value of depicting Trump as having incited a frightening terrorist attack just weeks before the election, and the zeal to feed the broader narrative pushed by the U.S. security state that anti-government extremism is America’s greatest national security threat, drowned out any skepticism. The storyline was clear and unquestioned: Trump was inciting ISIS-like terrorism on U.S. soil and right-wing extremists, who would fester even after Trump was done, were the primary menace that requires new domestic powers and larger budgets in order to defeat.
Yet just as happened with so many other narratives — from the origins of COVID to Hunter Biden’s corrupt use of his ties to his father — Trump’s defeat means the media is now willing to reconsider some of the propaganda that was pushed in the lead-up to the election. An excellent piece of investigative journalism published by BuzzFeed on Tuesday documents that, far from being passive observers of the plot, FBI informants and agents were the key drivers of it:
An examination of the case by BuzzFeed News also reveals that some of those informants, acting under the direction of the FBI, played a far larger role than has previously been reported. Working in secret, they did more than just passively observe and report on the actions of the suspects. Instead, they had a hand in nearly every aspect of the alleged plot, starting with its inception. The extent of their involvement raises questions as to whether there would have even been a conspiracy without them.
So central to this plot were those acting at the behest of the FBI that many of the accused plotters only met each other because of meetings arranged at the direction of the FBI, who targeted them based on social media postings and other political activities that suggested anti-government and anti-Whitmer sentiments which could be exploited:
A longtime government informant from Wisconsin, for example, helped organize a series of meetings around the country where many of the alleged plotters first met one another and the earliest notions of a plan took root, some of those people say. The Wisconsin informant even paid for some hotel rooms and food as an incentive to get people to come.
One of the FBI’s informants, a former Iraq War soldier, “became so deeply enmeshed in a Michigan militant group that he rose to become its second-in-command.” With his leadership role in one of the key groups, and all while acting under the direction of the FBI, he was “encouraging members to collaborate with other potential suspects and paying for their transportation to meetings.” Indeed, he even “prodded the alleged mastermind of the kidnapping plot to advance his plan, then baited the trap that led to the arrest.”
A review of not only the BuzzFeed reporting but also the underlying court documents leaves little doubt that the primary impetus for this plot came over and over from the FBI. On July 12, a lawyer for one of the defendants filed a motion asking the court to compel the FBI to turn over all chats which their agents and informants involving the plot. He did so on the ground that the few chats they had obtained themselves — from their own clients — repeatedly show the FBI pushing and prodding its agents over and over to lure defendants into more meetings, to join in “recon” exercises, and to take as many steps as possible toward the plot.
While it was clear from the start that there were FBI informants and agents in the middle of all of this, it turns out that at least half of those involved were acting on FBI orders: twelve informants and agents. As BuzzFeed says, those acting at the behest of the FBI “had a hand in nearly every aspect of the alleged plot, starting with its inception.” All of that, concluded the reporters, “raises questions as to whether there would have even been a conspiracy without them.”
But this evidence does not so much raise that question as much as it answers it. The idea of kidnapping Gov. Whitmer came from the FBI. It was a plot designed by the agency, and they then went on the hunt to target people they believed they could manipulate into joining their plot — either people were easily manipulated due to psychological weakness, financial vulnerability, and/or their strongly held political views. In sum, the FBI devised this plot, was the primary organizer of it, funded it, purposely directed their targets to pose for incriminating pictures that they then released to the press, and then heaped praise on themselves for stopping what they themselves had created.
For anyone covering the FBI during the first War on Terror, none of this is new. So many of the supposed “terror plots” the FBI purported to disrupt over the last twenty years were — just like the Michigan plot — ones that were created and driven by, and would not have happened without, the FBI’s own planning, funding and direction.
Just as they are doing now, the FBI used those plots to elevate fear levels and justify more domestic surveillance power and funding for the U.S. security state. While the targets then were typically young American Muslims with anti-government views rather than young right-wing white men with anti-government views, the tactics were identical.
The examples are far too numerous to count. As one illustrative example, in 2015, the FBI flamboyantly praised itself for arresting three Brooklyn men on charges of “attempt and conspiracy to provide material support to the Islamic State of Iraq.” Then, as now, outlets such as The New York Times promoted the FBI’s maximalist-fear-mongering version of events: “3 Brooklyn Men Accused of Plot to Aid ISIS’ Fight,” blared the headline.
But even that largely pro-FBI Times article raised the question of whether this plot was real or manufactured by the bureau:
The case against the three men relies in part on a confidential informant paid by the government, court documents show. Defense lawyers have criticized the government’s use of informers in similar cases, saying they may lure targets into making extreme plans or statements. In some cases, the threat has turned out to be overstated.
And the FBI itself admitted that the “threats of violence” from the three arrested — such as killing President Obama — “had an ‘aspirational’ quality to them, with no indication that the suspects were close to staging an attack, large or small.” The Times article also noted that the FBI observed that “in online postings, the two younger men seem to be searching for meaning in their lives,” adding that “as they were led into court, the youthfulness of Mr. Juraboev and Mr. Saidakhmetov was striking.”
Analyzing all the evidence in this case, my then-colleague at The Intercept Murtaza Hussain documented “the integral role a paid informant appears to have played in generating the charges against the men, and helping turn a fantastical ‘plot’ into something even remotely tangible.” Indeed, he wrote, “none of the three men was in any condition to travel or support the Islamic State, without help from the FBI informant.” It was only when the FBI sent an older Muslim man to gain their trust — acting as an FBI informant and being paid for his services — did anything resembling a crime start to form. The paid FBI informant encouraged the young men to pursue the plan more concretely, and only then did they begin agreeing with the informant’s proposed plot. The informant befriended them, moved in with them, and spent months “convincing both of them that he intended to travel to Syria and join Islamic State.”
Just as was true in the Michigan case, Hussain wrote about this arrest: “Crucially, it appears that only after the introduction of the informant did any actual arrangements to commit a criminal act come into existence.” In sum, “the covert informant under the direction of the FBI” — which employs teams of psychologists and other mental health professions who are experts in how to manipulate people’s thinking — “evidently helped encourage the two toward terrorism over the course of these months.”

Article by Murtaza Hussain of The Intercept, Feb. 20, 2015
I have also covered countless other FBI plots over the years where all the same attributes were present. After the 2015 “ISIS arrest,” I wrote an article compiling how often the FBI was doing this and asked this question in the headline: “Why Does the FBI Have to Manufacture its Own Plots if Terrorism and ISIS Are Such Grave Threats?,” noting that the bureau’s behavior “is akin to having the DEA constantly warn of the severe threat posed by drug addiction while it simultaneously uses pushers on its payroll to deliberately get people hooked on drugs so that they can arrest the addicts they’ve created and thus justify their own warnings and budgets.”
Months before the 2015 ISIS arrests, the FBI issued a press release praising itself for arresting “a Cincinnati-area man for a plot to attack the U.S. Capitol and kill government officials.” But as I reported, the scary terrorist was “20-year-old Christopher Cornell, [who] is unemployed, lives at home, spends most of his time playing video games in his bedroom, still addresses his mother as ‘Mommy’ and regards his cat as his best friend; he was described as ‘a typical student’ and ‘quiet but not overly reserved’ by the principal of the local high school he graduated in 2012.”
Then House Speaker John Boehner immediately seized on that arrest to warn Americans to be afraid: “We live in a dangerous country, and we get reminded every week of the dangers that are out there.” Boehner also told Americans they should be grateful for domestic surveillance and not try to curb it: the Speaker claimed that “the National Security Agency’s snooping powers helped stop a plot to attack the Capitol and that his colleagues need to keep that in mind as they debate whether to renew the law that allows the government to collect bulk information from its citizens.” Yet the only way Cornell got close to any crimes was because the FBI informant began suggesting to him that he act on his rage against U.S. officials by attacking the Capitol.

Salon articles of my reporting on FBI’s creation of terror plots it “stops”: Nov. 28, 2010 and Sep. 29, 2011
One of the most egregious cases I covered was the 2011 arrest of James Cromitie, an African-American convert to Islam who the FBI attempted to convince — over the course of eight months — to join a terror plot, only for him to adamantly refuse over and over. Only once they dangled a payment of $250,000 in front of his nose right after the impoverished American had lost his job did he agree to join, and then the FBI swooped in, arrested him, and touted their heroic efforts in stopping a terrorist plot.
The U.S. federal judge who sentenced Cromitie to decades in prison, Colleen McMahon, said she did so only because the law of “entrapment” is so narrow that it is virtually impossible for a defendant to win, but in doing so, she repeatedly condemned the FBI in the harshest terms for single-handedly converting Cromitie from a helpless but resentful anti-government fanatic into a criminal. The defendant “was incapable of committing an act of terrorism on his own,” she said, adding: “only the government could have made a terrorist out of Mr. Cromitie, whose buffoonery is positively Shakespearean in scope.” She added: “There is not the slightest doubt in my mind that James Cromitie could never have dreamed up the scenario in which he actually became involved.”
Her written ruling is worth quoting at length because of how relevant it is to current FBI activities. The judge began by noting that Cromitie “had successfully resisted going too far for eight months,” and agreed only after “the Government dangled what had to be almost irresistible temptation in front of an impoverished man from what I have come (after literally dozens of cases) to view as the saddest and most dysfunctional community in the Southern District of New York.” It was the FBI’s own informant, she wrote, who “was the prime mover and instigator of all the criminal activity that occurred.” She then wrote (emphasis added):
The Government indisputably “manufactured” the crimes of which defendants stand convicted. The Government invented all of the details of the scheme – many of them, such as the trip to Connecticut and the inclusion of Stewart AFB as a target, for specific legal purposes of which the defendants could not possibly have been aware (the former gave rise to federal jurisdiction and the latter mandated a twenty-five year minimum sentence). The Government selected the targets. The Government designed and built the phony ordnance that the defendants planted (or planned to plant) at Government-selected targets. The Government provided every item used in the plot: cameras, cell phones, cars, maps and even a gun. The Government did all the driving (as none of the defendants had a car or a driver’s license). The Government funded the entire project. And the Government, through its agent, offered the defendants large sums of money, contingent on their participation in the heinous scheme.
Additionally, before deciding that the defendants (particularly Cromitie, who was in their sights for nine months) presented any real danger, the Government appears to have done minimal due diligence, relying instead on reports from its Confidential Informant, who passed on information about Cromitie information that could easily have been verified (or not verified, since much of it was untrue), but that no one thought it necessary to check before offering a jihadist opportunity to a man who had no contact with any extremist groups and no history of anything other than drug crimes.
One of the reporters who has most extensively covered the FBI’s role in manufacturing terrorism cases it then proceeds to “break up” is Trevor Aaronson. In 2011, he documented, working with the Investigative Reporting Program at the University of California-Berkeley, that of 508 post-9/11 terrorism defendants, “nearly half the prosecutions involved the use of informants, many of them incentivized by money.” After 9/11, the FBI’s budget-increasing, power-enhancing strategy was to target “tens of thousands of law-abiding people, seeking to identify those disgruntled few who might participate in a plot given the means and the opportunity” by monitoring their social media postings, and “then, in case after case, the government provides the plot, the means, and the opportunity.” Of the terrorism arrests from sting operations, almost 1/3 were ones in which “defendants participated in plots led by an agent provocateur—an FBI operative instigating terrorist action.”
It is this long history and mountain of evidence that compels an investigation into the role played by the FBI in the planning of the 1/6 riot at the Capitol. And it is that same evidence that made the corporate media’s derisive reaction to such demands — as voiced by Darren Beattie’s Revolver News, Fox News’ Tucker Carlson and myself — so ignorant and subservient. They acted as if only some unhinged conspiracy theorist could possibly believe that the FBI would have informants and agents embedded in the groups that planned that Capitol riot rather than what it is: the only logical conclusion for anyone who knows how the FBI actually behaves.
Indeed, the BuzzFeed reporters who investigated the FBI’s key role in the Michigan case must have been very disturbed by what they found since they used their reporting to raise that taboo topic: what role did the FBI have in 1/6? Moreover, they asked, is this yet another era where the FBI is targeting Americans not for criminality but for their political views, and then orchestrating their own plots that justify the U.S. security state’s massive budget and unlimited powers?
Instead, [the accused] say, they were targeted because of their political views. Some describe the case as a premeditated campaign by the government to undermine the Patriot movement, an ideology based on fealty to the Second Amendment and the conviction that the government has violated the Constitution and is therefore illegitimate. They argue that the recordings and text messages that the government calls proof of a criminal conspiracy are in fact constitutionally protected speech — expressions of frustration at what they see as the government’s betrayal of its citizens.
The Michigan case is unfolding at another fraught moment in American history. In court, the government has drawn a direct line between the alleged kidnapping plot and the Jan. 6 insurrection, holding up the storming of the US Capitol as evidence that the Michigan defendants posed a profound threat. . . . [I]f the defense is able to undermine the methods used to build the Michigan case, it could add weight to the theory that the administration is conducting a witch hunt against militant groups — and, by extension, that the Jan. 6 insurrection was a black op engineered by the FBI.
When Carlson raised these same questions on his Fox program, he did what I did when doing so: cited my reporting as well as Trevor Aaronson’s about the FBI’s long history of orchestrating such plots and luring people into them using informants and undercover agents. Much of that reporting about the FBI’s tactics was published by The Intercept, which — when aimed at American Muslims during the First War on Terror — had an editorial view that it was extremely improper and dangerous for the FBI to do this. But now that it is being done to American anti-government activists on the right, the site’s liberal editors seem happy about it. They got Aaronson to write an article under the headline “Tucker Carlson Distorted My Reporting in His Latest Jan. 6 Conspiracy Theory.”
But that headline was an absolute lie. There was nothing in Aaronson’s article that pointed to any “distortions” in how Carlson (or I) cited Aaronson’s work. To the contrary, Aaronson himself acknowledged that the FBI’s past history — including in the Whitmer case — made such questions highly rational and necessary:
In many of these stings, informants or undercover agents provided all the money and weapons for terrorist plots, and sometimes even the ideas — raising significant questions about whether any of these people would have committed the crimes were it not for the FBI’s encouragement. Many targets of these FBI stings were mentally ill or otherwise easily manipulated. . . .
Carlson’s claim fits an existing and well-established argument: that the FBI creates crimes through aggressive stings where no crimes would otherwise exist. . . . I think it’s worth noting that there’s a reason for the cultural stickiness of the claim by Revolver and Carlson. It might be a conspiracy theory, but it’s not exactly “baseless,” as the Post described it. That’s because there are genuine concerns that the sting tactics used over the past two decades against impressionable Muslims will be used against equally impressionable Americans with right-wing ideologies. In the supposed plot to kidnap Michigan Gov. Gretchen Whitmer, for example, FBI agents and an informant played significant roles, raising the same question that surrounds so many supposed Islamic State and Al Qaeda cases in the United States: Would this plot have happened were it not for the FBI?
In addition, there is evidence the FBI is assigning informants to infiltrate groups based solely on right-wing ideology. And the increase in right-wing violence in recent years has prompted calls for new anti-terorrism laws that would give the FBI even more power.
I think the FBI’s investigation of potential right-wing threats, and the degree to which the bureau replicates its abusive post-9/11 tactics, will be a critically important story in the coming years. How news organizations report on it will be a significant test.
While Aaronson insists that no proof has yet been presented that the FBI had foreknowledge of the 1/6 plot or encouraged it to happen, and also seized on a minor error in the Revolver News article originally raising these questions about “confidential informants” — an error I noted in my own article about this topic while explaining that it was ancillary and insignificant to the overall question — Aaronson’s article has far more in common with the primary theme raised by Carlson than it does arguments that Carlson “distorted” anything. In particular, Aaronson writes, the FBI’s ample history requires a serious investigation into the role it may have played in knowing about and/or encouraging the 1/6 plotters.

As I documented in my own reporting on this question, there is ample evidence to believe that the FBI had informants embedded in at least two of three key groups it says were behind the 1/6 Capitol riot. As I noted at the time, most of the corporate press spewed contempt and scorn on these questions because 1/6 has become an event that carries virtually religious importance to them, and their reverence for the U.S. security state makes them resistant to any suggestions that the FBI may have acted deceitfully — an utterly bizarre mindset for U.S. journalists to possess. But such is the state of the liberal sector of the corporate press today.
Now that one of their own liberal members in good standing — BuzzFeed — has not only proven the FBI’s key role in the Whitmer plot but also themselves suggested that it makes more plausible the bureau’s involvement in 1/6, these questions are becoming increasingly unavoidable. Both the Whitmer plot and especially 1/6 are absolutely crucial to everything that has happened since: the launch of the new War on Terror, billions more in funds for the security state, proposals for greater surveillance, Biden’s use of the intelligence community to insist that anti-government activists constitute the greatest threat to U.S. national security. Asking what role the FBI played in the episode at the Capitol is not only rational but imperative.
July 24, 2021 Posted by aletho | Deception, Fake News, False Flag Terrorism, Mainstream Media, Warmongering, Timeless or most popular | FBI, United States | Leave a comment
“ABOUT HALF THE CASES ARE VACCINE FAILURES”
https://www.bitchute.com/video/64CAk8DKvagD/
The Highwire with Del Bigtree | July 22, 2021
Dr. Peter McCullough, joins the Highwire again, this time to discuss the serious problem with the efficacy of the #Covid19 vaccines and how mass vaccination is creating this runaway train of a pandemic.
July 24, 2021 Posted by aletho | Deception, Science and Pseudo-Science, Timeless or most popular, Video | Covid-19, COVID-19 Vaccine, Human rights, United States | Leave a comment
Billionaires Segregate Themselves on Luxury Private Islands as Ordinary People Told They Can’t Travel
By Paul Joseph Watson | Summit News | July 23, 2021
News that billionaire Google co-founder Larry Page has been hiding out on and buying isolated private islands in Fiji to avoid tourists who aren’t allowed in once again underscores how the elite is using the fallout from the pandemic to segregate themselves from the general public.
Page has been living off grid for over a year and forced a state-owned news website to remove an article about his activities that was also de-listed by Google in an apparent effort to conceal his location.
“He has spent months in Fiji during the coronavirus pandemic – mostly on the island of Tavarua – and it has been rumored the billionaire has bought at least one island in the country’s Mamanuca archipelago,” reports the Daily Mail.
“Page has also been spotted an a smaller island called Namotu – which a sailor named Lorenzo Cipriani claimed Page bought in a blog post in August.”
Page, who has a net worth of $117 billion, making him the sixth-wealthiest person in the world, was able to take advantage of Fiji’s ‘Blue Lane’ program, which “lets the super wealthy visit the archipelago on their superyachts and private jets, even when other travelers were banned.”
So while Page gets to enjoy a sumptuous view of the South Pacific while being attended to on his luxury private island by 30 staff waiting on him, ordinary people who have lost their jobs, businesses and homes due to the lockdown aren’t even allowed to travel there.
Page’s story is just a microcosm of how wealthy elitists have rapaciously exploited the lockdowns that they have vehemently supported and facilitated to further expand the economic inequality gap and segregate themselves from the peasants.
While Page has his staff prepare him cocktails and the finest cuisine after a day of surfboarding in paradise, children in his home country are either permanently traumatized and afraid to go outside or literally committing suicide out of loneliness caused by lockdown.
Meanwhile, the World Economic Forum – architects of ‘the Great Reset’ that has been rapidly advanced thanks to lockdown policies – tells people that they’ll “own nothing and be happy.”
It tells them to look forward to their rental servitude under a system of neo-feudalism that will make home ownership completely unaffordable.
Meanwhile, Davos billionaires like Bill Gates are buying up huge swathes of property, with Gates recently becoming the largest owner of farmland in America.
In terms of individual land owners, Gates is still far behind media mogul John C. Malone, who is in top spot with 2.2 million acres of ranches and forests and CNN founder Ted Turner, who owns 2 million acres of ranch land.
Amazon’s Jeff Bezos is also “investing in land on a large scale,” according to Forbes.
While billionaire philanthropists and technocrats are acquiring land at an accelerating speed, they appear to be telling the general public that in the future private property will virtually cease to exist.
The WEF also celebrates the notion that “lockdowns are quietly improving cities,” greasing the skids for climate lockdowns and regulated air travel even as the likes of Page and his ilk jet off for luxury holidays whenever they please, absent the nuisance of those pesky tourists who might spoil their tranquility.
While our quality of life is eroded, while we have to take vaccines and jump through 100 flaming hoops to be allowed to travel internationally, they’re all completely exempt – exempt from the same rules they onerously impose on us.
Tourists are flushed out and banned from entering countries so Page and his rich friends can enjoy their days of pampered, opulent leisure in total seclusion.
Indeed, many elitists have expressed delight at how global lockdowns have left roads, airports and luxury resorts in Caribbean countries virtually empty, allowing them to avoid any interaction whatsoever with the unwashed masses.
This then has the knock-on impact of forcing low income workers to flood to western countries in search of work, exacerbating tensions caused by mass uncontrolled immigration.
Billionaires also exploited the pandemic to snuff out their remaining competition and create even more centralized monopolies.
Worldwide, the combined wealth of the world’s 10 richest men rose by $540bn during the first year of the pandemic, including Amazon founder Jeff Bezos who saw his personal wealth grow by $86 billion as Amazon shares soared.
According to an Oxfam report, billionaires exploited the the impact of lockdown to create a “rigged economy,” causing expanding wealth inequality during the “worst economic downturn in a century.”
A record number of billionaires were also created in the UK during the pandemic even as millions of ordinary people lost their jobs and saw their businesses go under.
Meanwhile, lockdowns caused 150 million people globally to be pushed into extreme poverty.
But for those lucky enough to hold onto their jobs, they’re kept at arms length by ‘stay at home’ orders, remote working and Zoom calls, even as globalists continue to enjoy maskless BBQ parties at the G7 and socially un-distanced black tie dinners at Davos.
They still get to meet each other in person (while avoiding the worker drones), but you don’t.
None of this is anything new.
Since humanity began to divide into class systems, entrenched elites have always sought to aggressively separate themselves from the public, prevent the creation of a strong middle class, and maintain a poor service class that is only good for attending to their needs.
The major difference now is that the elite have built a giant technocracy which enables them to maintain total surveillance of the populations under their control, while they get to enjoy total exclusivity and privacy.
As Larry Page’s successful effort to get the article about his whereabouts removed from the news media proves, they get to conceal everything about their activities while demanding to know everything about yours.
They get to avoid attention and they get to avoid people knowing their location.
Meanwhile, your government health app knows your every locations and ‘pings’ you back under quarantine at the drop of a hat.
The advancement of robotics and artificial intelligence will also ensure that even much of the elite’s servant class will become obsolete in the near future.
This agenda will all be facilitated through puppet governments and private corporations, allowing Page, Gates, Zuckerberg and other billionaires to fade into the background and hide their role in the managed decline of civilization.
While they continue to inflict all of this upon humanity, we continue to bicker over identity politics, racism and all manner of relative trivialities that keep us divided and asleep.
And if you’re naive enough to think that this is all coming to an end as the coronavirus pandemic winds down, rest assured that there are many more ‘variants’ to be discovered and innumerable more reasons to put you back under lockdown.
Don’t worry though, because none of these restrictions will apply to Larry Page and his billionaire friends, who will remain totally isolated on their luxury private islands as the rest of the world goes to hell in a hand basket thanks to the economic warfare they declared on us.
July 23, 2021 Posted by aletho | Civil Liberties, Economics, Supremacism, Social Darwinism, Timeless or most popular | Covid-19, Human rights | Leave a comment
The African Union is self-destructing by letting Israel have observer status
By Dr Mustafa Mheta | MEMO | July 23, 2021
The Israeli Foreign Ministry announced yesterday that it has regained its observer status at the African Union. Until 2002, the colonial state was an observer member of the Organisation of African Unity, until the latter was dissolved and replaced by the African Union.
Who has decided to readmit Israel to the AU as an observer state? We know those responsible very well, because ever since they came to power in the continental body they have made some very unpopular decisions of no benefit to Africa and its people. Instead, they have sold us all to the highest bidder.
One day they will be exposed as traitors because Africa and its states have been born out of the struggles against slavery and colonialism; we don’t need to associate ourselves with colonial states such as the Zionist entity. In days gone by our kings and chiefs sold us for a teaspoon of sugar and a shiny mirror. Today our leaders are selling us again to the descendants of the same imperialists wearing democratic cloaks to hide their colonialist intentions.
Is there any difference between these modern African leaders and those who sold us into colonial slavery? Quite simply, none at all. They are the people who allow imperialists and Zionists to have access to our continent’s natural resources in exchange for spyware technology and weapons to enable their continuing grip on power.
When former Libyan leader Muammar Gaddafi spearheaded the formation of the African Union in 2002, he made sure that Zionist Israel was sidelined. Little did he know that his African brothers would go on to betray him and his anti-colonialist legacy.
Israel is a racist, apartheid state, so why should it have observer status at the AU? Before any such readmission was even considered, the union should have demanded that the Zionist state complies with the many UN resolutions hanging over it. It was a perfect opportunity to put pressure on Israel to withdraw from all Arab land that it occupies — Lebanese, Syrian and Palestinian alike — and facilitate the independence of the State of Palestine.
The AU needs to wake up to what Israel is capable of doing. Just this week, Britain’s Guardian newspaper has reported that an Israeli company has developed and sold Pegasus spyware to a number of governments, including some in Africa, and that at least fourteen world leaders (among many activists, journalists and human rights campaigners), including South African President Cyril Ramaphosa, have been targeted by the technology.
This is just one example of what befriending Israel means. One of the African leaders said to be implicated in such use of the Pegasus technology is Paul Kagame of Rwanda. He is a well-known friend of Israel and his relations with many of his neighbours in Africa are strained. Such relations are going to be tested even further after the Pegasus leak.
Kagame is known for pursuing his political opponents wherever they might be, and assassinating them. His relationship with the South African government is tense for that very reason. He also has problems with President Yoweri Museveni of Uganda, who accuses him of espionage using the very same Pegasus spyware. The government of Burundi is also complaining about Kagame for doing the same thing.
Rwanda recently deployed its troops to northern Mozambique and a fierce war of words has since erupted within the ruling FRELIMO party in Maputo. Given the Pegasus situation, how can the Southern African Development Community, of which Mozambique is part, trust the Rwandan military working alongside its forces? This arrangement could go very wrong. It is impossible to fight alongside those who are spying on you.
It’s a fact that wherever Israel goes and is welcomed, problems of this nature tend to arise. Countries are destabilised and turn on each other. It’s the old colonial tactic of divide and rule, playing one side off against another while pretending to be friends of both.
The Israel observer status move is the second serious blunder made by the AU recently. The first was to allow Morocco to return to the fold before withdrawing its forces from occupied Western Sahara.
With the Zionist entity involved in the AU, we can expect the continent to be destabilised even further. Africa simply cannot afford or allow that to happen. The AU must, as a matter of urgency, rescind the decision about Israel’s status unless and until it complies with all UN resolutions concerning its withdrawal from all occupied territories and facilitate Palestinian independence. If the colonial-occupation state refuses to do so, then formal relations between Tel Aviv and the African Union should be off the agenda.
July 23, 2021 Posted by aletho | Ethnic Cleansing, Racism, Zionism, Timeless or most popular | Africa, Israel, Zionism | Leave a comment
From COINTELPRO to Whitmer Kidnapping Plot: FBI ‘Manufactures’ Terrorism to Fight It
By Ekaterina Blinova – Sputnik – 23.07.2021
The FBI’s extensive role in Governor Whitmer’s case has once again raised the question of the bureau’s possible infiltration of the Capitol riots, says independent American journalist Max Parry, citing the federal agency’s long record of incitement, including the infamous COINTELPRO.
On 20 July, BuzzFeed reported that at least 12 FBI informants had infiltrated the group behind the Governor Gretchen Whitmer kidnapping plot. What’s more, these informants were not passively sitting there wearing wires but were actively involved with the group. One of them, an Iraq War veteran, rose to become the second-in-command of the Michigan militant group, taught the members of the militia military tactics, told them to convene with other potential suspects, and even paid for their transportation.
Yet another plotter who advised the militia on where to place explosives and offered to get them as much as the task would require turned out to be an undercover FBI agent, according to the media outlet.
Prior to this, members of the militia group stormed the State Capitol in April 2020 as part of a larger crowd that entered the building wearing protective gear and carrying rifles to protest against Whitmer’s COVID restrictions.
At the time, the US mainstream media largely blamed Trump for the April riot and the kidnapping plot, citing his Twitter posts targeting the state’s Democratic governor.
Fox News host Tucker Carlson picked up the BuzzFeed story raising the question as to what extent the FBI directed the Michigan militia’s conduct in both cases and reiterated his earlier assumption that the agency could have infiltrated and instigated the January 6th protests as well.
Tucker Carlson & @julie_kelly2 Discuss The Buzzfeed Report About The FBI's Involvement In The Governor Whitmer Plot & The Striking Similarities It Has To January 6th
Tucker: "So what does this suggest about January 6th, before you dismiss it as a 'conspiracy theory?'" pic.twitter.com/f7WCV3zIp6
— The Columbia Bugle 🇺🇸 (@ColumbiaBugle) July 22, 2021
Could the FBI Have Organised 1/6?
“The new revelations about the extent to which informants were involved in the devising of the plot to kidnap Governor Whitmer raises serious questions about 1/6”, says independent American journalist Max Parry. “If they were encouraging, arranging, and directing the Michigan extremists to try and capture the governor, they very well could have planned, controlled, and engineered the storming of the US Capitol if the Proud Boys, Oath Keepers, and other groups were as heavily penetrated by law enforcement as believed”.
This brings up the question: “Would the storming of Congress have happened without the instigations of undercover informants?”, the journalist notes.
According to Parry, there are reasons to believe that the militia groups participating in the Capitol siege in DC could have been infiltrated by federal agents, given it is known that Proud Boys leader Enrique Tarrio used to be an FBI informant. For its part, on 30 June, Revolver News, presumed that Stewart Rhodes, the founder and the leader of The Oath Keepers, America’s largest militia, could possibly be in cahoots with the bureau.
Per the media, it appears suspicious that while the DoJ has enough evidence to jail the leader of “the most extensively prosecuted paramilitary group” in connection with the Capitol riots, he, unlike his group mates, has not been arrested.
In any event, the bureau cannot deny that they, at the very least, had foreknowledge of the apparent 1/6 plot, Parry notes. A US Senate report last month detailed the intelligence failures leading up to the Capitol attack where the FBI and DHS dismissed the credibility of online rhetoric calling for violence.
FBI’s Long Record of Incitement
The mainstream media in America is dismissing the claims that the FBI could have played a role in the siege. Tucker Carlson, who suggested in June that federal agents may have helped organise the riot, was immediately called a conspiracy theorist. However, this assumption by no means sounds outlandish given the FBI’s long record of incitement.
On 21 June, Revolver News listed at least five cases when the bureau did just that, including the 1993 attempt to blow up the World Trade Centre and the agency’s infamous 15-year Counter Intelligence Programme (COINTELPRO) best-known for spying on Martin Luther King Jr.
COINTELPRO, which aimed at surveilling, infiltrating, discrediting, and disrupting political organisations and movements perceived as “subversive” by then-FBI Director J. Edgar Hoover, officially ran from 1956-1971. The tactics included smearing individuals and groups by using forged documents and by planting false reports in the media, IRS audits, harassment, incitement, warrantless surveillance and surreptitious entries, incarcerations on false pretexts, withholding exculpatory evidence, targeted assassinations, etc.
In June 1975, the American Civil Liberties Union submitted a report for Senate investigators on the Secret Army Organisation (SAO), a South California paramilitary group that was reportedly funded by the bureau to commit acts of violence and intimidation against left-wingers and their sympathisers between 1971 and 1972.
In 1976, American lawmakers detailed the methods of the FBI’s covert operation in a 994-page report and concluded that “many techniques used would be intolerable in a democratic society even if all its targets had been involved in violent activity but COINTELPRO went far beyond that”. Still, the bureau insisted that all of these were for the greater good, i.e. to protect national security and deter violence by “preventing the growth of dangerous groups and the propagation of dangerous ideas”.
It appears, however, that COINTELPRO tactics have still been used by the FBI, judging from the controversial Operation Crossfire Razor targeting General Michael Flynn, the details of which was exposed during his trial, or the bureau’s FISA abuses aimed at extending spying on Donald Trump aide Carter Page. Likewise, the DoJ and FBI’s extensive manhunt for January Sixers accompanied with pre-dawn raids, interrogations without an attorney, harassment, and apparent human rights abuses of detained January 6th defendants evoke strong memories of the 15-year intelligence op. One might wonder whether a loose network of Antifa militants who harassed US citizens and clashed with conservative groups during the 2020 summer riots was also in some sense inspired by COINTELPRO.
“The common thread throughout these operations where federal law enforcement orchestrates and participates in terror plots is exploiting individuals who are an easy target and prone to militancy, be it religious fanaticism or political extremism at either end of the spectrum”, highlights Parry. “Amid the current political climate in the country, the threat of right-wing extremism is most suitable to this particular time. During COINTELPRO, the target was the anti-war movement, the civil rights movement, and the political left. In the War on Terror, the aim was combating Islamic extremism. Recently we’ve seen how the bureau’s mission has shifted its focus to right-wing militia groups”.
What’s happening now is that with the Domestic Terrorism Prevention Act of 2021 and USA Patriot Act’s subsequent redefining of homegrown terrorism, “the national security apparatus is manufacturing the threats needed to broaden its surveillance state and unconstitutional powers at this particular historical moment”, the journalists presumes.
The Left Should be Alarmed
The American Left should not be deluded by the government having shifted its focus to the right and pro-Trump groups, says Parry.
“Following January 6th we have seen Democrats leading the charge for new domestic terror laws”, he stresses. “The left should have the sense to understand that these new expanded powers for the security state will inevitably be used against them and will backfire, especially given the precedent set by history and COINTELPRO. These are lawless and rogue agencies with no transparency or accountability and the FBI in particular routinely impedes oversight and goes totally out of bounds of the US Constitution”.
According to the journalist, “it is particularly disturbing the way the national security complex has managed to rehabilitate its image overnight during the Trump era where high-ranking intelligence officials and FBI directors have become media darlings and liberal heroes”.
Yet, in both the Whitmer case and, possibly, on 6 January, “the FBI has put the public at greater risk under the guise of protecting it and manufactured terrorism in the name of fighting it”, Parry concludes.
July 23, 2021 Posted by aletho | Civil Liberties, False Flag Terrorism, Timeless or most popular | FBI, Human rights, United States | Leave a comment
More Bad News for Masks
By Dr. Joseph Mercola | July 16, 2021
Mandating children to wear facemasks for long periods of time while at school and participating in other activities is an unprecedented move, one that was put into place despite no research showing the practice is safe. It’s not simply a case of “something is better than nothing,” because the act of mask wearing comes with a risk of adverse effects.
Now that the pandemic is more than a year behind us, evidence is starting to accumulate showing that the use of face masks in children may cause more harm than good. One of the latest studies noted that the evidence base for making face masks compulsory in schoolchildren is “weak,” and looked into their effects on carbon dioxide in inhaled air.1
Masks Increase Carbon Dioxide Inhalation
Your body produces carbon dioxide (CO2) as a byproduct of cellular function.2 This odorless, colorless gas is then transported via your blood to your lungs, where it is exhaled from your body. Normally, the CO2 then dissipates into the air around you before you take another breath. In the open air, carbon dioxide typically exists at about 400 parts per million (ppm), or 0.04% by volume.
The German Federal Environmental Office set a limit of CO2 for closed rooms of 2,000 ppm, or 0.2 percent by volume. If you’re wearing a facemask, the CO2 cannot escape as it usually does and instead becomes trapped in the mask. In a study published in JAMA Pediatrics, researchers analyzed the CO2 content of inhaled air among children wearing two types of masks, as well as wearing no mask.3
Children in the study ranged in age from 6 to 17 years, with a mean age of 10.7. While no significant difference in CO2 was found between the two types of masks, there was a significant elevation when wearing masks compared to not wearing them.
CO2 in inhaled air under surgical and filtering facepiece masks came in between 13,120 ppm and 13,910 ppm, “which is higher than what is already deemed unacceptable by the German Federal Environmental Office by a factor of 6,” the researchers noted.4 Also important, this level was reached after only three minutes, while children wear masks at school for a mean of 270 minutes at a time.
Even the child who had the lowest measured CO2 level had a measurement threefold greater than the closed room CO2 limit of 0.2 percent. However, younger children appeared to have the highest CO2 values; a level of 25,000 ppm was measured from a 7-year-old wearing a facemask.5
The study attracted criticism and calls for retraction by those questioning mask risks to children, but in a thoughtful synopsis by Dr. Vinay Prasad, a hematologist-oncologist and associate professor of medicine at the University of California San Francisco, it’s noted that there are both benefits and risks to forcing children to wear masks.6
While large, empirical studies could answer the question of whether masks help or harm children, “we did literally zero of them,” Prasad said, and the CO2 study is attempting to add some clarity. He added:7
“Here is the real answer to the question of whether it’s worth it to mask kids: No one has any clue. During the last year and half, the scientific community has failed to answer these questions. Failed entirely.
We have no idea if masks work for 2-year-olds and above, 5 and above, 12 and above. No idea if they only work for some period of time. No idea if this is linked to community rates. No idea if the concerns over language loss offset the gains in reduced viral transmission, and if so, for what ages.”
Children’s Mask Complaints Could Be Caused by Elevated CO2
A German study using data from 25,930 children showed that 68% reported adverse effects from wearing facemasks.8 Among them, 29.7% reported feeling short of breath, 26.4% being dizzy and 17.9% were unwilling to move or play.9
Hundreds more experienced “accelerated respiration, tightness in chest, weakness and short-term impairment of consciousness.” Additional symptoms were also reported among the children, who wore facemasks for an average of 270 minutes a day:10
|
Irritability (60 percent) |
Headaches (53 percent) |
|
Difficulty concentrating (50 percent) |
Less happiness (49 percent) |
|
Reluctance to go to school/kindergarten (44 percent) |
Malaise (42 percent) |
|
Impaired learning (38 percent) |
Drowsiness or fatigue (37 percent) |
Signs of mild to moderate hypercapnia, which is a buildup of CO2 in your bloodstream, include shortness of breath, daytime sluggishness, headache, daytime sleepiness and anxiety.11
Hypercapnia is often associated with chronic obstructive pulmonary disease (COPD), which makes it harder for you to breathe, but it can also be caused by activities that limit you from breathing fresh air, such as scuba diving or being on a ventilator.12,13 The researchers of the featured study believe, however, that the use of facemasks could lead to “impairments attributable to hypercapnia,” adding:14
“Most of the complaints reported by children can be understood as consequences of elevated carbon dioxide levels in inhaled air. This is because of the dead-space volume of the masks, which collects exhaled carbon dioxide quickly after a short time.
This carbon dioxide mixes with fresh air and elevates the carbon dioxide content of inhaled air under the mask, and this was more pronounced in this study for younger children … We suggest that decision-makers weigh the hard evidence produced by these experimental measurements accordingly, which suggest that children should not be forced to wear face masks.”
Nanoparticles, Pollutants Detected In Facemasks
Disposable plastic facemasks pose another risk in terms of the pollution they contain. A study by Swansea University researchers noted that 200 million disposable plastic facemasks are produced in China daily, and “improper and unregulated disposals” have led to a significant plastic pollution problem.15
The researchers submerged seven disposable facemask brands in water to simulate what happens with littering, when masks end up in waterways. Micro- and nanoscale fibers and particles and heavy metals, including lead, antimony and copper, were detected, raising significant environmental and public health concerns. According to a university news release:16
“The findings reveal significant levels of pollutants in all the masks tested — with micro/nano particles and heavy metals released into the water during all tests.
Researchers conclude this will have a substantial environmental impact and, in addition, raise the question of the potential damage to public health — warning that repeated exposure could be hazardous as the substances found have known links to cell death, genotoxicity and cancer formation.”
Not only are masks not being recycled, but their materials make them likely to persist and accumulate in the environment. Most disposable face masks contain three layers — a polyester outer layer, a polypropylene or polystyrene middle layer and an inner layer made of absorbent material such as cotton.
Polypropylene is already one of the most problematic plastics, as it’s widely produced and responsible for large waste accumulation in the environment. Leading researchers from the University of Southern Denmark and Princeton University also warned that masks could quickly become “the next plastic problem.”17
A performance study published in the June 2021 issue of Journal of Hazardous Materials18 also highlighted the little talked about fact that wearing masks poses a risk of microplastic inhalation, and reusing masks increases the risk.
The Link Between Masks And Advanced Stage Lung Cancer
A National Institutes of Health study19 published in February 2021 confirmed that when you wear a mask, most of the water vapor you would normally exhale remains in the mask, becomes condensed and is re-inhaled.20 They went so far as to suggest that wearing a moist mask and inhaling the humid air of your own breath was a good thing, because it would hydrate your respiratory tract.
But researchers from New York University (NYU) Grossman School of Medicine revealed that when oral commensals — microbes that live in your mouth — are “enriched” in the lungs, it’s associated with cancer.21
Specifically, in a study of 83 adults with lung cancer, those with advanced-stage cancer had more oral commensals in their lungs than those with early-stage cancer. Those with an enrichment of oral commensals in their lungs also had decreased survival and worsened tumor progression.
While the study didn’t look into how mask usage could affect oral commensals in your lungs, they did note, “The lower airway microbiota, whether in health or disease state, are mostly affected by aspiration of oral secretions, and the lower airway microbial products are in constant interaction with the host immune system.“22
It seems highly likely that wearing a mask would accelerate the accumulation of oral microbes in your lungs, thereby raising the question of whether mask usage could be linked to advanced stage lung cancer.
Masks Developed That Test For COVID-19
Adding further support that masking leads to an accumulation of breath droplets, which you can then re-inhale, engineers from the Massachusetts Institute of Technology and Harvard University developed a face mask that tests such droplets for the presence of COVID-19.23
The facemasks contain tiny, freeze-dried sensors surrounded by water. When the wearer pushes a button, the water is released, hydrating the sensor, which then begins the test.
Reportedly, the mask can diagnose COVID-19 within 90 minutes and is “as sensitive as the gold standard, highly sensitive PCR tests,“24 which have been fraught with trouble since the beginning of the pandemic.
CDC Study Finds Masks In Schools Had Little Effect On COVID
If children are risking inhalation of excessive levels of CO2 to wear masks at school, what benefit are they receiving in exchange? Very little, if any, according to a CDC study that compared the incidence of COVID-19 in Georgia kindergarten through grade 5 schools that were open for in-person learning in fall 2020 with various recommended prevention strategies, such as mandatory masks and improvements to ventilation.25
The study revealed that COVID-19 incidence was 37 percent lower in schools that required teachers and staff members to use masks and 39 percent lower in schools that improved ventilation, compared to schools that did not use these strategies.26
Because the COVID-19 incidence at the schools was extremely low to begin with, even with a 37 percent reduction in incidence from staff members wearing masks, that only reduced COVID-19 incidence by about one case in the entire school. When students were masked, it also made virtually no difference. Further, ventilation led to better outcomes, reducing incidence by 39 percent.
Dilution methods, which work by diluting the number of airborne particles, include opening windows and doors or using fans. This led to a 35 percent lower incidence of COVID-19, while methods to filter airborne particles, such as using HEPA filtration systems with or without ultraviolet germicidal irradiation, led to a 48 percent lower incidence.
More States Ban Mask Mandates In Schools
While the CDC continues to recommend “universal and correct use of masks and physical distancing” in kindergarten through grade 12 schools,27 a number of states, including Texas, Iowa, South Carolina and Arkansas, are defying the CDC’s nonsensical advice and proceeding to ban mask mandates in public schools or at least make mask usage optional.28
In addition to the physical risks, experts have warned that masks are likely to be causing psychological harm to children and interfering with their development.29 All of these risks come at little benefit to children, as, one expert report noted, “Figures illustrate that the risk of death from this disease for this age group is negligible … To introduce these [compulsory face covering measures] without detailed, thorough and meticulous risk assessment, is potentially reckless.“30
Mass, peaceful protests are often effective at compelling change, so if you’re unhappy with the facemask policies at your child’s school, contact your local district and let them know.
References:
1, 3, 4, 5, 8, 14 JAMA Pediatrics June 30, 2021
2 Wisconsin Department of Health Services, Carbon Dioxide
6, 7 MedPage Today July 7, 2021
9 Montana Daily Gazette, January 25, 2021
10 Research Square April 28, 2021
13 Open Anesthesia Hypercapnia Causes
15 Water Res. 2021 May 15;196:117033. doi: 10.1016/j.watres.2021.117033. Epub 2021 Mar 10
16 Swansea University May 5, 2021
17 Front. Environ. Sci. Eng. 2021, 15(6): 125
18 Journal of Hazardous Materials June 5, 2021; 411: 124955
19 Biophysical Journal February 11, 2021 DOI: 10.1016/j/bpj.2021.02.002
20 Healthing.ca February 16, 2021
21, 22 Cancer Discov. 2021 Feb;11(2):293-307. doi: 10.1158/2159-8290.CD-20-0263. Epub 2020 Nov 11
23 Nature Biotechnology June 28, 2021
24 The Jerusalem Post July 3, 2021
25, 26 U.S. CDC, Morbidity and Mortality Weekly Report May 21, 2021
27 U.S. CDC, Operational Strategy for K-12 Schools May 15, 2021
30 Health, Safety and Wellbeing Report in respect of Civil Proceedings April 9, 2021, Page 7
July 23, 2021 Posted by aletho | Civil Liberties, Science and Pseudo-Science, Solidarity and Activism, Timeless or most popular | Covid-19, Human rights | Leave a comment
Photoshopping, fraud and circular logic in research

By Mike Hearn | Daily Sceptic | July 22, 2021
It is simply no longer possible to believe much of the clinical research that is published, or to rely on the judgement of trusted physicians or authoritative medical guidelines. I take no pleasure in this conclusion, which I reached slowly and reluctantly over my two decades as an editor of the New England Journal of Medicine.
Check out this image from a peer reviewed research paper that supposedly shows skin lesions being treated by a laser:

Left: before treatment for keratoses. Right: after they were airbrushed out. (image diff is available here)
On being challenged the authors said:
The photograph was taken in the same room with a similar environment; unfortunately the patient wore the same shirt.
The journal found this explanation acceptable and forwarded the response to the complainants.
It’s becoming clear that science has major difficulties with not only a flood of incorrect and intellectually fraudulent claims, but also literally faked, entirely made up papers with random data, imaginary experiments and photoshopped images in them. Some of these papers are sold by organised gangs to Chinese doctors who need them to get promoted. But others come from really sketchy outfits like (sigh) the National Health Service, to whom we owe the masterpiece seen above.
The British Government hasn’t noticed that its doctors are massaging medical evidence. Instead this example comes from Elizabeth Bik, who runs a blog where she and a few other volunteers try to spot clusters of fraudulent papers. She embarrassed the journal in public here, and the paper was finally retracted. But she’s just a volunteer who raises money on Patreon for her work. Here’s her assessment of what’s going on:
Science has a huge problem: 100s (1000s?) of science papers with obvious photoshops that have been reported, but that are all swept under the proverbial rug, with no action or only an author-friendly correction… There are dozens of examples where journals rather accept a clean (better photoshopped?) figure redo than asking the authors for a thorough explanation.
As the only people trying to spot these fake papers are bloggers, we can safely assume that far larger numbers of papers are fake than the “thousands” they have already found and reported. For example,
0.04% of papers are retracted. At least 1.9% of papers have duplicate images “suggestive of deliberate manipulation”. About 2.5% of scientists admit to fraud, and they estimate that 10% of other scientists have committed fraud.
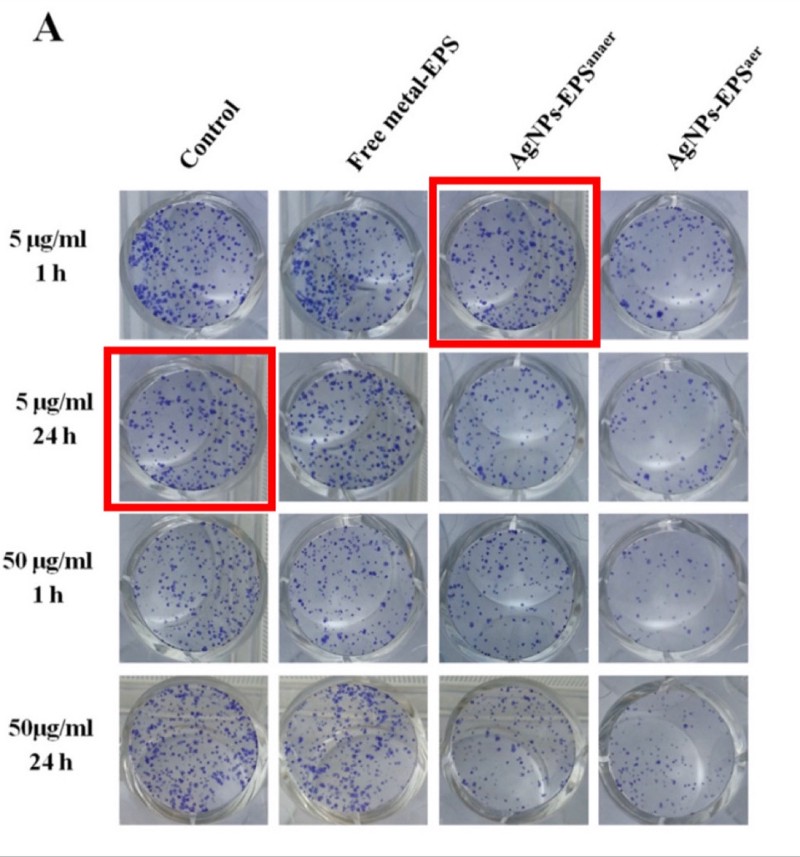
Photos of supposedly different samples in which two images are identical. From “Anticancer activity of biogenerated silver nanoparticles: an integrated proteomic investigation”. The journal investigated and concluded that this is fine.
It’s been known for years that a lot of claims made by scientists can’t be replicated. In some fields, the majority of all claims appear to not replicate due to a large mix of issues like overly lax thresholds for claiming statistical significance, poor study design and other somewhat subtle errors. But how much research is deliberate falsehood?
The sad truth is the size of the fraud problem is entirely unknown because the institutions of science have absolutely no mechanisms to detect bad behaviour whatsoever. Academia is dominated by (and largely originated) the same ideology calling for the total defunding of the police, so no surprise that they just assume everyone has absolute integrity all the time: research claims are constantly accepted at face value even when obviously nonsensical or fake. Deceptive research sails through peer review, gets published, cited and then incorporated into decision making. There are no rules and it’d be pointless to make any because there’s nobody to enforce them: universities are notorious for solidly defending fraudulent professors.
So let’s turn over the rock and see what crawls out. We’ll start with China and then turn our attention back to more western types of deception.
Chinese fraud studios
In 2018, the U.S. National Science Foundation announced that: “For the first time, China has overtaken the United States in terms of the total number of science publications.” Should the USA worry about this? Perhaps not. After some bloggers exposed an industrial research-faking operation that had generated at least 600 papers about experiments that never happened, a Chinese doctor reached out to beg for mercy:
Hello teacher, yesterday you disclosed that there were some doctors having fraudulent pictures in their papers. This has raised attention. As one of these doctors, I kindly ask you to please leave us alone as soon as possible… Without papers, you don’t get promotion; without a promotion, you can hardly feed your family… You expose us but there are thousands of other people doing the same. As long as the system remains the same and the rules of the game remain the same, similar acts of faking data are for sure to go on. This time you exposed us, probably costing us our job. For the sake of Chinese doctors as a whole, especially for us young doctors, please be considerate. We really have no choice, please!
Note the belief that “thousands of other people” are doing the same, and that these doctors need more than one paper to keep being promoted, so the 600 found so far is surely the tip of an iceberg given China’s size. There are about 3.8 million doctors in China implying that there are quite possibly tens of thousands, maybe hundreds of thousands of these things in circulation.
The fake papers are remarkable:
- They are so good they are undetectable in isolation. The NHS photo is an aberration – normally these papers get spotted by noticing re-used technical images across papers that claim to be different experiments by different people. The fake papers are probably produced by real scientists with access to real lab equipment. The use of spammy-looking Gmail accounts is also a signal because Gmail is banned in China (e.g.
BrendaWillingham12192@gmail.com,RosettajKirkland3814@gmail.com,CaseyPeiffer8311@gmail.com). The reliance on bot-generated Gmail accounts implies enormous scale. - They are peer reviewed and published in western journals. For instance, the Journal of Cellular Biochemistry by Wiley or Biomedicine & Pharmacotherapy by Elsevier. They claim to be doing advanced micro-biology on serious diseases: a typical title is something like “MicroRNA-125b promotes neurons cell apoptosis and Tau phosphorylation in Alzheimer’s disease”. Journals have no way to detect these papers and aren’t trying to develop any.
- Some of them present traditional Chinese medicine as scientific. TCM is more or less the Chinese equivalent of homeopathy with lots of herbal remedies, eating body parts of exotic animals to cure erectile dysfunction, and so on. But the Chinese Government is obsessed with it and thinks it’s the same as normal medicine. From the top down, Chinese scientists are expected to produce papers claiming that TCM works, and they do! Mostly this stuff stays in Chinese but the ever increasing reliance of western universities on Chinese funding means it’s now finding its way into the English language literature as well, e.g. “Probing the Qi of traditional Chinese herbal medicines by the biological synthesis of nano-Au” was published by the Royal Society of Chemistry.

Advert by a research faking operation. Credit to “Smut Clyde” and “TigerBB8”.
Most western scientists are too clever to buy a completely fake paper (or so we hope). But their promotion incentives are identical, and there are other techniques that let you publish as many fake papers as you want. Let’s turn our attention to…
Impossible numbers in western science
The case against science is straightforward: much of the scientific literature, perhaps half, may simply be untrue.
Richard Horton, editor of the Lancet
How many scientists just make up their data? A well known recent case of this was the Surgisphere scandal, in which a paper appeared in The Lancet that claimed to be based on a proprietary dataset of nearly 100,000 COVID-19 patients across over 670 U.S. hospitals. This figure was larger than the official case counts of some entire continents at the time, and there was no reason for hospitals to share tightly controlled medical data with a random company nobody had heard of, so the claim was implausible on its face. Sure enough, when challenged it turned out none of the authors had ever actually seen the data, just summaries of it provided by one guy, who on investigation had a long track record of dishonesty. The Lancet probably accepted this paper because it made Trump look bad and the editor (Horton, quoted above) appears to hate Trump more than he hates bad science.
President Trump’s decision to defund WHO is simply this—a crime against humanity. Every scientist, every health worker, every citizen must resist and rebel against this appalling betrayal of global solidarity. https://t.co/7hTwUZ4lJV
— richard horton (@richardhorton1) April 14, 2020
There are some other cases like this that came to light over the years, like the story of Brian Wansink, or that of Paolo Macchiarini, who left a trail of dead patients in his wake. But while anecdotes about individual cases are interesting, can we be more rigorous?
One clue comes from automated tools that scan research papers looking for mathematically impossible numbers, which can sometimes be detected even in the absence of the raw original data. In recent years a few such tools have been developed and deployed, mostly against psychology and food science.
- The statcheck program showed that “half of all published psychology papers… contained at least one p-value that was inconsistent with its test”.
- The GRIM program showed that of the papers it could verify, around half contained averages that weren’t possible given the sample sizes, and more than 20% contained multiple such inconsistencies.
- The SPRITE program detected various experiments on food that would have required subjects to eat implausible quantities (e.g. a child needing to eat 60 carrots in a single sitting, or 3/4 kilogram of crisps).
Being flagged by a stats checker doesn’t guarantee the data is made up: GRIM can detect simple mistakes like typos and SPRITE requires common sense to detect that something is wrong (i.e., no child will eat a plate of 60 carrots). But when there are multiple such problems in a single paper, things start to look more suspicious. The fact that half of all papers had incorrect data in them is concerning, especially because it seems to match Richard Horton’s intuitive guess at how much science is simply untrue. And the GRIM paper revealed a deeper problem: more than half of the scientists refused to provide the raw data for further checking, even though they had agreed to share it as a condition of being published. This is rather suspicious.
One of the difficulties with detecting scientific fraud is that the line between dishonesty and simple absurdity can get quite blurry. Sometimes scientists “calculate” data that is clearly wrong, but don’t actually try to hide or it may even admit to it in the paper, knowing full well that nobody cares and nonsensical data won’t actually matter. Here’s an example from a COVID modelling paper:
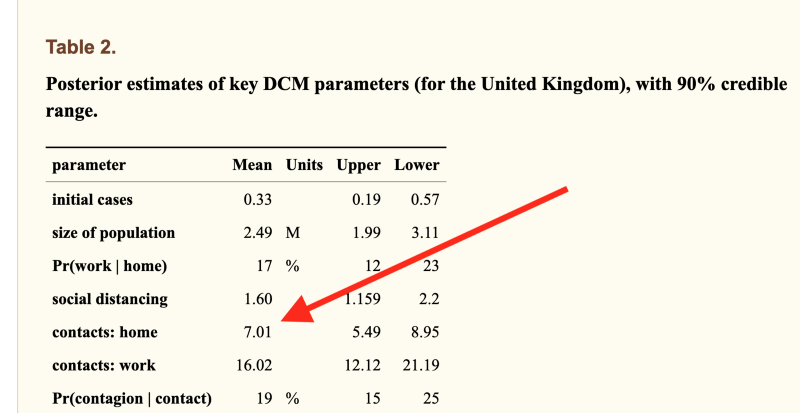
The model was allowed to calculate that the average Brit must live with 7 other people, because it couldn’t obtain data fit otherwise (actual number=2.4). This one comes from University College London, is written by 12 neuroscientists, passed peer review and has 37 citations. The peer reviewer noticed that the incorrect number was in the paper but signed off on it anyway.
For decades psychiatrists published research into the “gene for depression” 5-HTTLPR. They created an entire literature not only linking the gene to depression but explaining how it worked, linking it to parenting styles, developing treatments based up on it. Over 450 papers were published on the topic. Eventually a geneticist discovered what they were doing and used DNA databanks to point out that none of those papers could possibly be true.
Sometimes numbers aren’t “wrong” but are instead logically vacuous. The Flaxman et al paper from Imperial College that tried to prove lockdowns work had the usual problem of statistically implausible numbers, but more importantly was built on circular logic: their model assumed only government interventions could end epidemics. This is obviously nonsense and they breezily admitted it in the paper, where they said their work was “illustrative only” and that “in reality even in the absence of government interventions we would expect Rt to decrease”. No problem: this fictional illustration got published in Nature and the authors presented the model’s outputs as scientific proof of their own assumption to the media. The paper is vacuous mathematical obfuscation, but scientists either can’t tell or don’t care: it has racked up over 1,300 citations and the number is still growing rapidly. To put that number in perspective, in physics the top 1% of all researchers have around 2,000 citations over their entire career.
Time to assume that health research is fraudulent until proven otherwise?
Earlier this month, the BMJ published an astounding blog post with the same title as this section. There’s no need to add anything because simply quoting it is sufficient:
The anaesthetist John Carlisle analysed 526 trials submitted to Anaesthesia and found that… when he was able to examine individual patient data in 153 studies, 67 (44%) had untrustworthy data and 40 (26%) were zombie trials… [Ben] Mol’s best guess is that about 20% of trials are false. Very few of these papers are retracted.
We have now reached a point where those doing systematic reviews must start by assuming that a study is fraudulent until they can have some evidence to the contrary.
Richard Smith
Richard Smith is a former editor of the BMJ, cofounder of the Committee on Medical Ethics (COPE), for many years the chair of the Cochrane Library Oversight Committee, and a member of the board of the U.K. Research Integrity Office.
Or put another way, an overseer of the Research Integrity Office believes research has no integrity.
What can be done?
600 fraudulent papers here, 450 over there, 1300+ citations of just one bad paper… pretty quickly it starts adding up.
We’re often told science is self-correcting. Is that true? Probably not. “The Science Reform Brain Drain” is perhaps the bleakest essay I’ve read this year. Reformers like the men who developed SPRITE and GRIM have been giving up and leaving science entirely. Pointing out in public that your colleagues are dishonest is never a great career move, and the work was often futile. One scientist who quit and went into industry summed up his fraud detection work like this:
The clearest consequence of my actions has been that Zhang has gotten better at publishing. Every time I reported an irregularity with his data, his next article would not feature that irregularity.
Even when a bull enters the China shop and gets a few papers retracted, it doesn’t actually matter because it has little effect: retracted papers keep getting cited for years afterwards and actually may be cited more than non-retracted papers, because one of the effects of retraction is that the article becomes free to download.
In the past year most talk of bad science has been about models with bad assumptions. This is an issue but has been hiding problems that are far worse: scientists are buying fake papers, Photoshopping evidence, refusing to upload their data, knowingly publishing numbers that cannot be correct, citing papers that were retracted for being fraudulent and (of course) presenting mathematical obfuscations of what they want to be true as if it were science. Journals usually ignore fraud reports entirely, or when put under pressure let scientists submit “corrected” versions of their papers. And worst of all, the journal editors that are responsible for scientific gatekeeping know all this is happening, but aren’t doing anything about it.
In fact, very little can be done because above all, universities rely on reputation and don’t want anyone to find out about bad behaviour, so they fight tooth and nail to protect academics no matter how badly they are behaving. There are no rules. Any rules that are alleged to exist turn out when tested to be illusions.
Claims made by scientists are automatically trusted by the majority of people. Maybe they shouldn’t be?
Mike Hearn is a former Google software engineer. You can read his blog at Plan 99.
July 22, 2021 Posted by aletho | Corruption, Deception, Science and Pseudo-Science, Timeless or most popular | Leave a comment
A Conversation with Dr. Byram Bridle
Supervisor Jim Desmond | April 13, 2021
We sat down with Dr. Byram Bridle, an associate Professor of Viral Immunology, Department of Pathobiology at the University of Guelph. Here’s the article that we discussed: https://theconversation.com/a-year-of…
July 22, 2021 Posted by aletho | Science and Pseudo-Science, Timeless or most popular, Video | Canada, Covid-19, United States | Leave a comment
Where’s the Rage for Israel and NSO’s Pegasus the West Had for China’s Huawei?
By Morgan Artyukhina – Sputnik – 21.07.2021
Anger has swirled around the globe over revelations that Pegasus spyware created by Israeli software firm NSO Group has been used by governments to wiretap journalists and public figures. However, the fury is mild when compared to claims Beijing compelled Huawei to put a “backdoor” into its phones, which has never been proven.
Earlier this week, a group of news outlets including the Washington Post and Forbidden Stories, along with human rights group Amnesty International, revealed disturbing findings: governments around the globe have been buying up Pegasus spyware from NSO Group and using it to spy on journalists, public figures, and even other world leaders.
50,000 Phones Targeted
Thousands of phone numbers are on the list, with some of the biggest names including French President Emmanuel Macron and Moroccan journalists Omar Radi, both allegedly wiretapped by Morocco, and journalist Jamal Khashoggi, allegedly wiretapped by his native Saudi Arabia prior to being killed by a Saudi hit squad at the Saudi consulate in October 2019.
In all, 180 journalists were targeted in 20 countries, including Kazakhstan, India, the United Arab Emirates, Qatar, Azerbaijan, Hungary, Morocco, Rwanda, Democratic Republic of the Congo, Mexico, Egypt, Algeria, Togo, Turkey, France, Spain and the United Kingdom. They also targeted at least 65 business executives, 85 human rights activists, 189 journalists, and more than 600 politicians and government officials, including high-level officials like cabinet ministers, diplomats, and military officers, according to The Washington Post.
Also on the list were 10 prime ministers, three presidents, and one king, including Iraqi President Barham Salih, South African President Cyril Ramaphosa, the prime ministers of Pakistan, Egypt, and Morocco, and seven former heads of government from Lebanon, Uganda, and Belgium, and several other countries.
Shalev Hulio, NSO’s chief executive and co-founder, has cast the story as flimsy, but said the company is “investigating every allegation … and if we find that it is true, we will take strong action.”
“NSO Group’s technologies have helped prevent terror attacks, gun violence, car explosions and suicide bombings. NSO Group is on a lifesaving mission and the company will faithfully execute this mission undeterred, despite any and all continued attempts to discredit it on false grounds,” the company told the US Public Broadcasting Service.
On Wednesday, the firm put out a press release saying “enough is enough,” announcing it would cease responding to media inquiries about what it called a “vicious and slanderous campaign.”
“NSO is a technology company. We do not operate the system, nor do we have access to the data of our customers, yet they are obligated to provide us with such information under investigations,” the company added.
The Israeli government has confirmed it “approves the export of cyber products exclusively to governmental entities, for lawful use, and only for the purpose of preventing and investigating crime and counterterrorism, under end use /end user certificates provided by the acquiring government. In cases where exported items are used in violation of export licenses or end use certificates, appropriate measures are taken.”
However, it denied having any knowledge of the use of Pegasus to spy on other targets, and noted to the Post that “Israel does not have access to the information gathered by NSO’s clients.”
That said, a former senior US national security official who has worked closely with the Israeli security services also told the outlet “It’s crazy to think that NSO wouldn’t share sensitive national security information with the government of Israel. That doesn’t mean they’re a front for the Israeli security agencies, but governments around the world assume that NSO is working with Israel.”
How Have Nations Reacted?
Representatives from many of the nations implicated in the investigation have unanimously denied the reports they spied on journalists, dissidents, and world figures, insisting their governments are based on the rule of law. However, it’s notable that not all of the countries where journalists were targeted have been asked for comment, with France, Spain, and the UK being notable exceptions.
Asked by The Hindu, a White House spokesperson said on Wednesday that “The United States condemns the harassment or extrajudicial surveillance of journalists, human rights activists, or other perceived regime critics.”
However, despite the admission by NSO that it sells such software and by Israel that it, at the very least, approved of each sale, and in light of comments by foreign intelligence officials that Israel likely materially benefitted from the affair by gleaning information from the group, it seems that a bigger scandal would be expected. But not a single government has demanded punishment for either NSO or Israel, or decried even the possibility that Israel helped countries wiretap people not suspected of criminal actions, or raised fears that a country’s government likely got ahold of classified information from them via illegal means.
There have been no calls for sanctions against Israel or NSO or any senior figures at NSO, or prosecutions, or frankly even acknowledgements that the affair is even happening outside of dry-mouthed condemnations. In fact, the only calls for sanctions have been by journalists themselves, such as the Intercept’s Ryan Grim and Electronic Intifada’s Ali Abuminah.
The reactions – and lack thereof – stand in stark comparison to how Chinese tech giant Huawei has been treated.
Huawei Crucified Without Evidence
Shenzhen-based Huawei is the world’s largest manufacturer of both telecommunications equipment and smartphones and a major supplier of 5G internet service. The company was started in 1987 by Ren Zhangfei, a former Chinese military engineer, although he owns less than 2% of its shares, which are owned by Huawei employees.
The US has claimed for years that Ren’s military experience and membership in the Communist Party of China make Huawei a security liability, but in 2018 a more concerted effort began aimed at forcing US military and government agencies from using products by Huawei and another Chinese phone maker, ZTE, claiming that the CPC had forced Huawei to insert a secret “back door” into its phones and networks, enabling the Chinese government to spy on users if so desired.
The company and the Chinese government have both denied that such a backdoor does or even could exist or that they would pursue one if it were possible.
“If they believe there’s a backdoor, they should offer evidence to prove it,” Huawei chairman Liang Hua challenged US intelligence in January 2019. At the time, Washington said it didn’t need to, citing Huawei’s alleged proximity to the Chinese government as sufficient proof.
However, as the US began hounding allies in Germany and the “Five Eyes” nations to drop Huawei’s technologies, it did begin providing them with evidence to support its claims – evidence London, Berlin, and Paris all said wasn’t very convincing. Still, within months each of them had either rejected bids by Huawei or suddenly found new evidence to justify falling into line with US demands.
The firm was placed on a US blacklist in 2019, requiring Americans to obtain a special license from the US Department of Commerce before doing business with Huawei, effectively banning Americans from buying Huawei’s phones, and several nations have now sanctioned Huawei as well. The company’s CFO, Meng Wanzhou, was also arrested in Canada in connection with charges in a US court that aren’t related to the espionage allegations but which are widely seen as further persecution of the company.
The sanctions had their effect, too: in March, a first-quarter earnings report showed its sales down 16.5% year-on, part of a trend that caused it to sell its Honor smartphone marquee last year.
Legacy of Israeli Spying on Allies
In September 2019, Politico reported that US government officials had concluded Israel was responsible for placing cell phone surveillance devices called “Stingrays” around Washington, DC, and had even used them to spy on White House communications. A former senior official used as a source for the article said the devices were likely intended to spy specifically on then-US President Donald Trump, a known lover of his iPhone.
Then-Israeli Prime Minister Benjamin Netanyahu dismissed the report, saying, “Israel doesn’t conduct espionage operations in the United States, period.”
However, the claims go back much further. In 1985, US intelligence analyst Jonathan Pollard was arrested, charged, and later convicted of espionage after he passed classified US Navy documents to Israel, including dirt on Israel’s Arab neighbors, for $1,500 a month.

Jonathan Pollard, U.S. Navy ID picture
Israel also spied on then-US Secretary of State John Kerry in 2014 and 2015 during negotiations for what became the Joint Comprehensive Plan of Action, according to reports by Der Spiegel and the Wall Street Journal.
In 2017, Le Monde revealed that Israel’s Mossad had penetrated the French intelligence directorate in what it called Operation Ratafia, with the goal of developing close relationships with fellow spies “to the point of crossing the line of turning them into double agents.”
None of these brought calls for sanctions, either, revealing how politically motivated the attacks on Huawei and other Chinese tech firms really are. Why does the West continue to tolerate the Israeli government spying on them and their citizens?
July 21, 2021 Posted by aletho | Civil Liberties, Timeless or most popular | China, France, Human rights, Israel, United States | Leave a comment
Featured Video
Iran Blockade Complications
or go to
Aletho News Archives – Video-Images
Book Review
Alarmist climate science as a textbook example of groupthink
By Paul MacRae | May 1, 2012
… Groupthink was extensively studied by Yale psychologist Irving L. Janis and described in his 1982 book Groupthink: Psychological Studies of Policy Decisions and Fiascoes.
Janis was curious about how teams of highly intelligent and motivated people—the “best and the brightest” as David Halberstam called them in his 1972 book of the same name—could have come up with political policy disasters like the Vietnam War, Watergate, Pearl Harbor and the Bay of Pigs. Similarly, in 2008 and 2009, we saw the best and brightest in the world’s financial sphere crash thanks to some incredibly stupid decisions, such as allowing sub-prime mortgages to people on the verge of bankruptcy.
In other words, Janis studied why and how groups of highly intelligent professional bureaucrats and, yes, even scientists, screw up, sometimes disastrously and almost always unnecessarily. The reason, Janis believed, was “groupthink.” He quotes Nietzsche’s observation that “madness is the exception in individuals but the rule in groups,” and notes that groupthink occurs when “subtle constraints … prevent a [group] member from fully exercising his critical powers and from openly expressing doubts when most others in the group appear to have reached a consensus.”[2]
Janis found that even if the group leader expresses an openness to new ideas, group members value consensus more than critical thinking; groups are thus led astray by excessive “concurrence-seeking behavior.”[3] Therefore, Janis wrote, groupthink is “a model of thinking that people engage in when they are deeply involved in a cohesive in-group, when the members’ strivings for unanimity override their motivation to realistically appraise alternative courses of action.”[4]
The groupthink syndrome
The result is what Janis calls “the groupthink syndrome.” This consists of three main categories of symptoms:
1. Overestimate of the group’s power and morality, including “an unquestioned belief in the group’s inherent morality, inclining the members to ignore the ethical or moral consequences of their actions.” [emphasis added]
2. Closed-mindedness, including a refusal to consider alternative explanations and stereotyped negative views of those who aren’t part of the group’s consensus. The group takes on a “win-lose fighting stance” toward alternative views.[5]
3. Pressure toward uniformity, including “a shared illusion of unanimity concerning judgments conforming to the majority view”; “direct pressure on any member who expresses strong arguments against any of the group’s stereotypes”; and “the emergence of self-appointed mind-guards … who protect the group from adverse information that might shatter their shared complacency about the effectiveness and morality of their decisions.”[6]
It’s obvious that alarmist climate science—as explicitly and extensively revealed in the Climatic Research Unit’s “Climategate” emails—shares all of these defects of groupthink, including a huge emphasis on maintaining consensus, a sense that because they are saving the world, alarmist climate scientists are beyond the normal moral constraints of scientific honesty (“overestimation of the group’s power and morality”), and vilification of those (“deniers”) who don’t share the consensus. … Read full article
Blog Roll
-
Join 2,459 other subscribers
Visits Since December 2009
- 7,489,872 hits
Looking for something?
Archives
Calendar
Categories
Aletho News Civil Liberties Corruption Deception Economics Environmentalism Ethnic Cleansing, Racism, Zionism Fake News False Flag Terrorism Full Spectrum Dominance Illegal Occupation Mainstream Media, Warmongering Malthusian Ideology, Phony Scarcity Militarism Progressive Hypocrite Russophobia Science and Pseudo-Science Solidarity and Activism Subjugation - Torture Supremacism, Social Darwinism Timeless or most popular Video War Crimes Wars for IsraelTags
9/11 Afghanistan Africa al-Qaeda Australia BBC Benjamin Netanyahu Brazil Canada CDC Central Intelligence Agency China CIA CNN Covid-19 COVID-19 Vaccine Donald Trump Egypt European Union Facebook FBI FDA France Gaza Germany Google Hamas Hebron Hezbollah Hillary Clinton Human rights Hungary India Iran Iraq ISIS Israel Israeli settlement Japan Jerusalem Joe Biden Korea Latin America Lebanon Libya Middle East National Security Agency NATO New York Times North Korea NSA Obama Pakistan Palestine Poland Qatar Russia Sanctions against Iran Saudi Arabia Syria The Guardian Turkey Twitter UAE UK Ukraine United Nations United States USA Venezuela Washington Post West Bank WHO Yemen Zionism
 Aletho News
Aletho News- Ceasefire no longer viable after 200 days of Israeli violations: Hamas
- Israeli strikes intensify across southern Lebanon, casualties reported
- Left in Disbelief: Israel in Panic over Hezbollah FPV Drone Nightmare
- Trump Taps Israel Lobbyist From Mossad Cutout FDD To Join Iran Negotiations
- Trump’s Blockade Snatches Defeat from the Jaws of Victory
- Geopolitics and Geoeconomics of the Strait of Hormuz
- Mali: a new front in the Western war on multipolarism
- CHD Scientist: CDC, FDA COVID Vaccine Safety Monitoring ‘Insulting, and Many People Are Injured’
- COVID Conniving Receives First Federal Indictment
- Iran Blockade Complications /Lt Col Daniel Davis & Nima Alkhorshid
 If Americans Knew
If Americans Knew- Israel’s New Ambassador to the ‘Christian World’ Served as Envoy to Azerbaijan During the Ethnic Cleansing of Christians from Nagorno-Karabakh
- US set to sell $1B “Advanced Precision Kill Weapon System” to Israel – Daily Update
- Israeli Strikes Kill at Least 32 Across S Lebanon, Including Children – Amid “Ceasefire”
- Israel to pour $730m into propaganda arm amid reputational crisis
- Real Cost of Iran War Likely Double the $25 Billion Figure the Pentagon Gave to Congress
- Israel conducts farthest-ever strike in long history of attacks on Gaza humanitarian aid flotillas
- In Gaza, Israel commits 10+ ceasefire violations a day – Daily Update
- US ships 6,500 tons of munitions, equipment to Israel in 24 hours
- A New Library in Gaza Rises From the Ashes of Destruction
- Israel’s top Jewish religious body ‘refuses to condemn’ smashing of Jesus statue
 No Tricks Zone
No Tricks Zone- Oversupply Of Volatile Solar Energy Leads To Record NEGATIVE Prices!
- New Study: Extreme Heat Records, Heatwaves, Extreme Cold Records Declining Across US Since 1899
- It’s The Cold, Stupid! Cold 20 Times More Lethal Than Heat, Multiple Studies Show
- European Institute For Climate And Energy: “Climate Debate is Seldom About Science”
- New Study: The Climate May Be 5 Times More Sensitive To Solar Forcing Than Commonly Assumed
- EV Industry Reached $70 Billion In Losses In 2024 Due To Delusional Green Ideologies
- Reality Check: Maldives Have Actually Grown In Size Or Remained Stable Over Recent Decades
- Abrupt Climate Change Also Occurred NATURALLY In The Past …25 Times During Last Ice Age
- Cave Discovery Reveals Today’s Desert Climates Were Recently Far Warmer, Wetter, Teeming With Life
- German Expert: Heat Dome Led To Record Temps In Western USA…Warmer In 1934, 1936
Contact:
atheonews (at) gmail.com
Disclaimer
This site is provided as a research and reference tool. Although we make every reasonable effort to ensure that the information and data provided at this site are useful, accurate, and current, we cannot guarantee that the information and data provided here will be error-free. By using this site, you assume all responsibility for and risk arising from your use of and reliance upon the contents of this site.
This site and the information available through it do not, and are not intended to constitute legal advice. Should you require legal advice, you should consult your own attorney.
Nothing within this site or linked to by this site constitutes investment advice or medical advice.
Materials accessible from or added to this site by third parties, such as comments posted, are strictly the responsibility of the third party who added such materials or made them accessible and we neither endorse nor undertake to control, monitor, edit or assume responsibility for any such third-party material.
The posting of stories, commentaries, reports, documents and links (embedded or otherwise) on this site does not in any way, shape or form, implied or otherwise, necessarily express or suggest endorsement or support of any of such posted material or parts therein.
The word “alleged” is deemed to occur before the word “fraud.” Since the rule of law still applies. To peasants, at least.
Fair Use
This site contains copyrighted material the use of which has not always been specifically authorized by the copyright owner. We are making such material available in our efforts to advance understanding of environmental, political, human rights, economic, democracy, scientific, and social justice issues, etc. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. In accordance with Title 17 U.S.C. Section 107, the material on this site is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. For more info go to: http://www.law.cornell.edu/uscode/17/107.shtml. If you wish to use copyrighted material from this site for purposes of your own that go beyond ‘fair use’, you must obtain permission from the copyright owner.
DMCA Contact
This is information for anyone that wishes to challenge our “fair use” of copyrighted material.
If you are a legal copyright holder or a designated agent for such and you believe that content residing on or accessible through our website infringes a copyright and falls outside the boundaries of “Fair Use”, please send a notice of infringement by contacting atheonews@gmail.com.
We will respond and take necessary action immediately.
If notice is given of an alleged copyright violation we will act expeditiously to remove or disable access to the material(s) in question.
All 3rd party material posted on this website is copyright the respective owners / authors. Aletho News makes no claim of copyright on such material.
